This fact, largely driven by the rise of cost-effective CAPTCHA solving solutions offered by low-waged individuals internationally over the last couple of years, continues to empower virtually anyone possessing the right cybercrime-friendly tools, with the ability to abuse any major Web property in a potentially fraudulent or malicious way.
In this post, I'll profile one of the most recently released DIY fake account registration/management/promoting tool, targeting Instagram, highlight its core features, as well as emphasize on the true impact that these tools are having on some of the world's most popular Web properties.
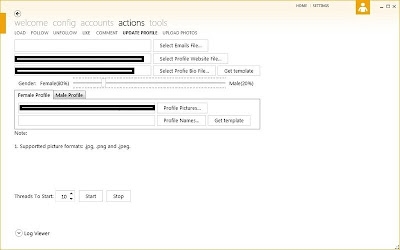
Sample screenshots of the tool in action:
Some of its core features are:
- support for multi-threads
- set number ot accounts to generate using a single proxy (malware-infected host)
- randomization of the posted bogus content to avoid easy detection of the pattern
- male/female fake account creating capabilities
- mass account validity checking capabilities
- CAPTCHA-solving integration with third-party CAPTCHA solving services
Known cases of abuse of legitimate infrastructure for fraudulent/malicious purposes over the years include:
Bogus "Shocking Video" Content at Scribd Exposes Malware Monetization Scheme Through Parked Domains
Fake Codec Serving Domains from Digg.com's Comment Spam Attack
Bogus LinkedIn Profiles Redirect to Malware and Rogue Security Software
Dissecting the Bogus LinkedIn Profiles Malware Campaign
From Ukraine with Scareware Serving Tweets, Bogus LinkedIn/Scribd Accounts, and Blackhat SEO Farms
Celebrity-Themed Scareware Campaign Abusing DocStoc and Scribd
Celebrity-Themed Scareware Campaign Abusing DocStoc
From Ukraine with Bogus Twitter, LinkedIn and Scribd Accounts
Pharmaceutical Spammers Targeting LinkedIn