Dear blog readers,
I've decided to share with everyone my most recent compilation in the fight against ransomware globally which is basically a compilation of known ransomware-themed personal email address accounts known to have been involved in the actual ransomware recruitment and funds solicitation process.
Sample list of known ransomware-themed email address accounts known to have been involved in various ransomware themed campaigns include:
goldwave@india.com
dokulus@tutanota.com
3mvlyd3@gmail.com
wowaanne@mail.ru
Brilliancebk@protonmail.com
James2020m@aol.com
legalrestore@tutanota.com
nCyberwars@protonmail.com
petrus34@p-security.li
BM-2cTzz6rwtd8d7qd1wVegH6sZ44GbNPV8Li@bitmessage.ch
Supportdecrypt@firemail.cc
koxic@cock.li
pentaxyz777@protonmail.com
hacker_decryption@protonmail.ch
securityagent@techmail.info
myqjs01@gmail.com
mvplocksvc@yahoo.com
alexbanan@tuta.io
filesrecoveren@onionmail.org
remotePChelper@tutanota.com
iknowyouandiseeyou@protonmail.ch
recoverydata99@protonmail.com
nvlastnou.hlavou@mailfence.com
helpmanager@iran.ir
Decipher@keemail.me
nmydataback@cock.li
Bossi_tosi@protonmail.com
Silver@decryption.biz
FreeWizard9@protonmail.com
karapooz@cock.li
20dfs@keemail.me
decrypt123@sent.com
cryptocash@aol.com
Dor.file@bk.ru
coronav2020@cock.li
truongquocvi@gmail.com
cstddetnkvcmknl@gmail.com
test.jpg.id-1235240425_help@decryptservice.info
phobos_help@xmpp.jp
lUUUUUUUUUUbasq@mail.ru
gxa34rttf50gqlagnes@gmail.com
nsoft.russian@secmail.pro
Marina.jeffeaux91@klachurch.org
AperywsQaroci@o2.pl
kcwjspen@gmail.com
gomer@horsefucker.org
f1220@tuta.io
seed@firemail.cc
decryptiondata@india.com
igbosshorse@xmpp.jp
0405000330@inbox.ru
encrypt2020@outlook.com
Blitzkriegpc@protonmail.com
dj.elton@hotmail.co.uk
nm67p7a@mailfence.com
asmo49@asmodeus.us
getdataback@fros.cc
Tuko.Salamanca@mailfence.com
05250lock@protonmail.com
Rtsghost@outlook.com
westlan@protonmail.ch
petropasevich@aol.com
silena.berillo@gmail.com
berr@keemail.me
nfileig@gtechie.com
element444@keemail.me
assistant@bitmessage.ch
lalabitch2017@yandex.com
gyeceeidia7y@gmx.com
decryptioncompany@inbox.ru
barracudahelper@exploit.im
devilguy@sigaint.org
nzdarovachel@gmx.at
Lemordewn@gmail.com
Apple.pass@mail.com
RecoveryData1@cock.li
geniusid@protonmail.ch
money21@onionmail.org
cryptget@tutanota.com
flower.harris@protonmail.com
Trojan.Win64.estemaniii@airmail.cc
recoryfile@tutanota.com
t310ea89b4347@protonmail.com
China.Helper@india.com
hallome@tutanota.com
numbermskpiter@dnmx.org
contatoaac@vpn.tg
gherardobaxter@aol.com
phrasitliter1981@protonmail.com
europay@india.com
gorentos@bitmessage.ch
technopc@protonmail.com
Decryptallfiles3@india.com
projectb@onionmail.org
nCobra_Locker@protonmail.com
tikitakbum@rambler.ru
bitcoin666@cock.li
lord_bomani@keemail.me
montserrat501@protonmail.com
BTCBREWERY@protonmail.com
hallome@firemail.cc
kirova.ls@orangedv.tmweb.ru
g8k4w@keemail.me
spaxl425@protonmail.com
Mk.goro@aol.com
your_last_chance_help@elude.in
supercrypt@mailer9.com
qatarworldcuplivedraw@gmail.com
Beulah34@1490.com
rikeistner@gmail.com
marjut56@cock.li
recoverydata@india.com
supportd@tfwno.gf
petrov441@protonmail.com
fmhir@protonmail.com
vlastnou.hlavou@mailfence.com
nreverso@cock.li
mydatarecovery@india.com
Beauchamp.tammie@mail.ru
hitsbtc@tuta.io
sill@tuta.io
torchwood@riseup.net
black.world@tuta.io
theonewhoknocks6969@mailinator.com
nrecoverymydata@protonmail.com
nBioawards@tutanota.com
flydragon@mailfence.com
realunlocker@india.com
tomascry@protonmail.com
lasvegasincel@cock.li
berserk666@tutanota.com
conactme@fake-box.com
Salesrestoresoftware@gmail.com
filedownload2020@protonmail.com
nown@ruggedinbox.com
decrfile@tutanota.com
andres11@cock.li
ex_parvis@aol.com
helpsend369@gmail.com
Repair_data@cryptmail.com
Deccoder431@protonmail.com
info@russianvip.io
decode77@sfletter.com
irmagetstein@india.com
Filegorilla1388@gmx.de
mr.dec@tutanota.com
nRobSmithMba@protonmail.com
pain@onefinedstay.com
teammarcy10@cock.li
61f1e8055af3f6a672959e6b0493a2@gmail.com
loggitore1984@tuta.io
costestu@cock.li
zitenmax@rambler.ru
help@ausi.com
Lizardbkup@protonmail.com
tom.anderson@india.com
ncrab1917@protonmail.com
mailnitrom@tutanota.com
kolobocheg@aol.com
Bioawards@tutanota.com
ngorentos2@firemail.cc
audrey.b@aol.com
nExte1@msgden.net
kamikizu@keemail.me
Recuperadados@protonmail.com
comodosec@yandex.com
ncrypto7892@protonmail.com
TimisoaraHackerTeam@protonmail.com
cage1@gmx.us
DecrypterSupport@protonmail.com
manager@time2mail.ch
RECOVERUNKNOWN@protonmail.com
lpe-cve@usa.com
fuck4u@cock.li
decode77777@gmail.com
UnluckyWare@torbox3uiot6wchz.onion
barracuda@airmail.cc
netcrash@msgsafe.io
deposithere@e-mail.ph
rocosmon@cock.li
padredelicato@secmail.pro
info@borontok.uk
decoderhelp@cock.li
Freedom29@Tutanota.com
dou876sh@mail.ee
Unlockdata@criptext.com
blower@firemail.cc
vashmail@protonmail.com
freshkart@420blaze.it
nBilly11@4302.com
Jchan@india.com
yagababushka@yahoo.com
backspace@riseup.net
geneve020@protonmail.com
yourmom@yahoo.com
helpyouhelpyou@cock.li
vote2024forjb@protonniail.com
vankosa@secmail.pro
ms.heisenberg@aol.com
neftet@tutanota.com
recfiles@protonmail.com
Gocrypt@aol.com
hildaseriesnetflix125@tutanota.com
Help@decryptservice.info
nJohnPennegZZ@aol.com
decryption@india.com
toolsl990m@gmail.com
supl0@post.com
Diablo_diablo2@aol.com
ncrypto7892@gmx.de
Encryptc4@elude.in
djranarony4@gmail.com
gorkmork@tutanota.de
n0301192293@protonmail.com
Alex.vlasov@aol.com
fonix@mailfence.com
Sos@anointernet.com
Ninja_gaiver@aol.com
doctorSune@protonmail.com
Helpme@freespeechmail.org
crypto7892@protonmail.com
nhelpmanager@firemail.cc
waiting@india.com
Sc0rpio@cock.li
ops2@mailc.net
dogeremembersss@protonmail.ch
abat2019@yahoo.com
__murzik@jabber.mipt.ru
nEmpty003@protonmail.com
monster666@tuta.io
goldmind@tuta.io
byaki_buki@aol.com
fileisafe@tuta.io
EMAIL@protonmail.com
loggitore1984@mailchuck.com
nLindaHunter474@gmail.com
amigo_a@india.com
Decryptmyfiles@qq.com
fixprotectvvv@protonmail.com
rebushelper@exploit.im
johnsonwhate@protonmail.com
brbrcodes@gmail.com
Datarest0re@aol.com
decodeodveta@protonmail.com
mark_white@mail.ua
Suppteam03@india.com
crannbest@foxmail.com
Jackie7@asia.com
restore19@cock.li
Savefiles@india.com
btcdecoding@foxmail.com
numlock@2riseup.net
ncrab1917@gmx.de
j0ra@protonmail.com
u043aocode@gmail.com
decoder@cock.li
locked@vistomail.com
phomen@airmail.cc
jduy3jd87dhs@grr.la
myphoto.jpg.nefartanulo@protonmail.com
Decrpt@tutanota.com
andrey.taranov@protonmail.com
rescuerr@protonmail.com
Trojan.Win64.AiDcrypt@tutanota.com
greatideacompany@gmail.com
Cde@onionmail.info
Shark01@msgden.com
ferrari@msgsafe.io
Cyberwars@protonmail.com
rahidproject@cock.li
supportdecryption@cock.li
delafuente1945@outlook.com
Light_Yagami@tuta.io
developer.110@tutanota.com
coding_434@tutanota.com
raypas@goat.si
dr.crypt@aol.com
ncrab7765@protonmail.com
bannedlands@msgsafe.io
china_jm@protonmail.ch
crypt64@mail.ru
ursa2277@gmx.com
m4xroothackerteam@protonmail.com
frankhans@tuta.io
decryptorsoon301@aol.com
contato.arquivoszip@email.tg
AlanRed@criptext.com
universe11@bigmir.net
nfilein@yandex.com
darkwaiderr@tutanota.com
repairmyfile@tormail.org
Worldcry@cock.li
t_tasty@aol.com
loggitore1984@protonmail.com
Corpseworm@protonmail.com
FridaFarko@yahoo.com
lathelp16@gmail.com
azrdecryptorbuy@firemail.cc
helpshadow@india.com
belgorod8712kozos@airmail.cc
cobainOransom@cock.li
tlalpidas1978@aol.com
phobos_helper@xmpp.jp
im.online@aol.com
dec.service@protonmail.com
Admin@adsoleware.com
Gerentoshelp@firemail.cc
email_info@cryptedfiles.biz
File-help@india.com
you@domain.com
rdphack@onionmail.org
decrypt@india.com
stopfilesrestore@india.com
Meldonii@india.com
merosa@firemail.cc
happyness@keemail.me
support911@cock.li
lolitahelp@cock.li
files000001@gmail.com
johnsmith987654@tutanota.com
dcyptfils@protonmail.ch
dexp@cock.li
blackhat@iname.com
ctrlalt@cock.li
BatHelp@india.com
scryptx@meta.ua
Files2021@tutanota.com
mail@rapid2019.com
AiDcrypt@tutanota.com
nBeulah34@1490.com
Support_wc@bitmessage.ch
Decisivekey@tutanota.com
wyna@nyu.edu
batary5588@india.com
sumpterzoila@aol.com
hemant.frnz@gmail.com
jerry_glanville_data@aol.com
aes-ni@tuta.io
FilesRecoverEN@Protonmail.com
Iyieg9eB@secmail.pro
nmerosa@india.com
DecryptMyData@mailfence.com
Sosca@foxmail.com
lxhlp@protonmail.com
Trojan.Win32.help@decrypt-files.info
managerhelper@airmail.cc
ampkcz@onionmail.org
WannaRenemal@goat.si
Gregoryluton021021@gmail.com
lion7872@gmx.de
quiddoss@protonmail.com
Help_you@india.com
nefartanulo@protonmail.com
WOWSMith123456@encripted.net
Darknes@420blaze.it
sendr@tutanota.com
FilesRecoverFR@Gmail.com
decrypt.guarantee@aol.com
youneedmail@protonmail.com
kfrvokr@protonmail.ch
MildredRLewis@teleworm.us
themail@cock.li
kiaracript@gmail.com
decryptionwhy@india.com
goodjob24@foxmail.co
nullcipher@cock.li
brelox777@gmail.com
help73@protonmail.com
3542516480@qq.com
decryptfiles19@cock.li
biggsurprise@tutanota.com
onion33544@india.com
helpdatarestore@firemail.cc
ihurricane@sigaint.org
pipikaki@onionmail.org
rebushelp@airmail.cc
Usdatadecrypt@gmail.com
crazykillwe123@outlook.com
softs98@protonmail.com
nkrupalupium@india.com
TucoSalamanca@elude.in
Funnybtc@airmail.cc
DIGITALKEY@163.com
maxicrypt@cock.li
encfilesos@aol.com
helplovx@excite.co.jp
lanran-decrypter@list.ru
Zizz@tutanota.de
ks20296@email.vccs.edu
Merd@tutanota.com
decrypt.my.files@gmail.com
meowcorp@msgsafe.io
garrymagic@tutanota.com
ransom.izi.crypt@gmail.com
Recoverybat@protonmail.com
newrecoveryrobot@pm.me
aid.keepcalm@protonmail.com
jakie.nunes@tutanota.com
hildalolilovesyou@memeware.net
recovery94@cock.li
Cho.dambler@yandex.com
popstop@foxmail.com
nAskHeIp@india.com
desktopmain228@india.com
Redshitline@india.com
Tara72@1753.com
Gerkaman@aol.com
nblower@fireman.cc
n3tw0rm@tuta.io
contact@casinomtgox.com
SayanWalsworth96@protonmail.com
brovsky@airmail.cc
Mrcrypting@airmail.cc
skgrhk2018me@tutanota.com
g0dd@criptext.com
decode00001@gmail.com
unlock_rabbit@pm.me
artemy75@cock.li
nhands_q647t@pudxe.com
support@bestyourmail.ch
keypassdecrypt@india.com
jacdecr@tuta.io
pecunia0318@tutanota.com
universe1@protonmail.ch
B32588601@163.com
daves.smith@aol.co
1ss33ggur@scryptmail.com
decr@cock.li
info@cryptedfiles.biz
pain@cock.lu
farhani.ma98@gmail.com
nnaviteam@aol.com
swordofsakura@india.com
Decoder_master@aol.com
alexwind46@protonmail.com
workencryptincfolder@india.com
pabpabtab@tuta.io
Trojan.Win64.Merosa@india.com
uff1aitunes_decrypt@protonmail.com
burgeer@protonmail.ch
u201cSaveYou49@9399.com
kirova.l@mutualizm.ru
nAileen65@9033.com
flyingship@mail2tor.com
nExte2@protonmail.com
getacrypt@tuta.io
nmosteros@firemail.cc
JinMaglaya@protonmail.com
recover85@protonmail.com
ndatarestore@iran.ir
notopen@countermail.co
Trojan.Win64.Bitcharity@protonmail.com.com
n0x69x@protonmail.com
incantofiles@bitmessage.ch
langolier@airmail.cc
torrenttracker@india.com
nfilel@keemail.me
ouuohk@eclipso.eu
Blammo@cock.li
fud@lycos.com
my0day@aol.com
help@cairihi.com
help_havaneza@cryptolab.net
youhaveonechance@420blaze.it
HydaHelp1@tutanota.com
icq-is-firefox20@ctemplar.com
blackgoldl23@protonmail.com
debora2019@airmail.cc
grand@horsefucker.org
decryptor171@mail2tor.com
FilesHelp@tutanota.com
BatHelp@protonmail.com
Panzergen552@gmx.de
eiklot@hi2.in
criptoman@mailfence.com
carcinoma24@aol.com
ms_13@aol.com
thorntitini1979@danwin1210.me
ndecoder-help@protonmail.com
alphareserve@tuta.io
flowerboard@torguard.tg
Opencode@india.com
systems@tutanota.com
notnepo@cock.lu
nnomoreletters@protonmail.ch
fun63s@protonmail.com
Grapn206@india.com
bsprj1020@protonmail.com
databack2@airmail.cc
knoocknoo@cock.li
rekoh4th@secmail.pro
GetMyPass@qq.com
ndatarecovery@airmail.cc
decrypt25@protonmail.com
roterbro@cock.li
server.recover@mail.ru
recovery.company@protonmail.com
enter_software@india.com
Stevenseagal@airmail.cc
BM-2cUm1HG5NFf9fYMhPzLhjoBdXqde26iBm2@bitmessage.ch
4lok3r@tutanota.com
phomen@cock.li
Mailrepa.lotos@aol.com
crypto.support@aol.com
metan19@mail2tor.com
Vengisto@india.co
astra2eneca@aol.com
fileisafe@protonmail.com
xaodecrypt@airmail.cc
Blacklist@cock.li
nsupl0@oath.com
auinfo16@gmail.com
nguifullchartil1970@protonmail.com
axitrun2@tutanota.com
gluttonBD@protonmail.com
cryptomavens@protonmail.com
decoder-help@protonmail.com
itsupport831@reddithub.com
panda7499@protonmail.com
crypt32@jabber.ua
mailnitrom@protonmail.ch
ransomriggs@qq.com
newneo1312@protonmail.com
nCitrteam@aol.com
hlpp@protonmail.ch
Tizer77234@protonmail.com
johnsonwhate@tutanota.com
tara_fox5@aol.com
infodept1999@yandex.com
mars_dec@outlook.com
file_name.doc.workencryptincfolder@india.com
cryptgh0st@protonmail.com
decodedecode@tutanota.com
decryptbox@airmail.cc
tfastrecovery@airmail.cc
egalytyy@protonmail.com
beryl.mclennan@tutanota.de
alpha2018a@aol.com
Stevensons@tuta.io
cryptbit2.0@protonmail.com
randal_inman@aol.com
GuardBTC@cock.li
decrypt01.cq@protonmail.com
badhach2@aol.com
factfull0103@airmail.cc
elitebot@msgden.net
nJamesBaker78@tutanota.com
nowayout@sigaint.org
safeanonym14@sigaint.org
filein@yandex.com
BM-2cTAPjtTkqiW2twtykGm5mtocFAz7g5FZc@bitmessage.ch
yuzhou13@tutanota.com
259461356@qq.com
restoring_sup@india.com
telegramfirefox2029@protonmail.com
unl0ck@keemail.me
ninja777@cock.li
helpshadow@firemail.cc
samanta@scryptmail.com
ny0000@protonmai1.com
nBackuppc@dr.com
Ncrypt@cock.li
branden4505@airmail.cc
decryptiondata@bitmessage.ch
grethen@tuta.io
decryptor@cock.li
schusterboss@dnmx.org
decryptor666@420blaze.it
security@qnap.com
phobos_helper@exploit.im
felix@countermail.com
jsmith1974@mail.fr
decrypt0077@gmail.com
blackbyte1@onionmail.org
hnx911@yahoo.com
euphoria-help@elude.in
servicedigilogos@protonmail.com
Makedonskiy@gmx.com
foxnitro@tutanota.com
helper@tfwno.gf
leltitbedecrypteddzi@gmail.com
Nowayout@protonmail.com
Ramachandra7@india.com
UnluckyWare@mail2tor.com
Glenna52@2606.com
retrnyoufiles@tutanota.com
MarzocchiZadok95@mail.com
nmr.yoba@aol.com
decry1@cock.li
niggapoopool23@protonmail.com
DharmaParrack@protonmail.com
naes-ni@protonmail.com
nbizarrio@venom.io
blower@fireman.cc
Datarest0re@protonmail.com
eula.2052.txt.coder007@protonmail.com
french101@cock.li
nFridaFarko@protonmail.com
robocript@india.com
royroy@cock.li
1413201760@qq.com
newwave@airmail.cc
Honeylock@protonmail.com
justbtcwillhelpu@firemail.cc
doris.sammer@rasendmail.com
InkognitoMan@tutamail.com
vengisto@firemail.cc
decryptors@xmpp.is
vombombom@cock.li
venom@privatemail.com
Insane@airmail.cc
nmydataback@aol.com
flapalinta1950@protonmail.com
Exte2@protonmail.com
nmetan19@mail2tor.com
unl0ckme@cock.li
1.kazkavkovkiz@cock.li
pulpy@protonmail.ch
jundmd@cock.li
payoff@cock.li
gardengarden@cock.li
wwxxxxxww@protonmail.com
crab7765@protonmail.com
bitsupportz@protonmail.com
ex_parvis@protonmail.com
AskHeIp@protonmail.com
vendetta553@gmx.de
colambia@tutanota.com
cryptosupport@tormail.net
Dataadecrypt@Cock.li
mmm_reborn@tutamail.com
gladius_rectus@india.com
regem_regum@aol.com.onion
Encrypted_Roblox@mail.com
getthefiles2@protonmail.ch
a11back@protonmail.ch
Badfail@qq.com
windat@protonmail.com
encoderdecryption@yandex.ru
lion7872@india.com
FlamingoRans@tutamail.com
g.kulahmet@protonmail.com
Radxlove7@india.com
internationalassistance@tutanota.com
nmiddleman2020@protonmail.com
rep_stosd@protonmail.com
Filegorilla1388@india.com
mrdoc8869@xmpp.jp
admin@bugsfighter.com
easybackup@aol.com
TheYuCheng@yeah.net
klowershit1835@tutanota.com
nGlenna52@2606.com
decode99999@gmail.com
nhelprestoremanager@airmail.cc
nenter_software@india.com
cavefat@tuta.io
newhelper24@protonmail.ch
VitalyYermakov@cock.li
jerjis@tutamail.com
python.exe.coder007@protonmail.com
torchwood0000@yandex.com
Helprestore@firemail.cc
Colecyrus@mail.com
decryptbots@cock.li
btc_bitts@protonmail.com
nAdamBrown89@protonmail.com
test@mail.com
DecryptFox@protonmail.com
fantom12@techemail.com
support@amazon.com
contactfileszip@email.tg
avghost@oteteam.com
Rezcrypt@cock.li
AdvancedBackup@protonmail.com
help@decrypt-files.info
virusremovalg@gmail.com
vine77725@protonmail.com
reservedecryption@protonmail.com
Filedecryptor@protonmail.com
Whiteblackgroup002@gmail.com
blacknord@tutanota.com
NastasyaTurkina68@mail.ru
dc1@imap.cc
Hushange_delbar@outlook.com
thegodfather83@mailfence.com
itunes_decrypt@protonmail.com
absolutefreedom@cock.li
bigbro1@cock.li
Vengisto@india.com
xaodecrypt@protonmail.com
blacklist@clock.li
donovantudor@aol.com
filesreturn247@india.com
xxxxxxx@xxxx.xxx
m4zm0v@keemail.me
origami7@firemail.cc
desync@airmail.cc
pixell@tutanota.com.ph
proxy-failover@mozilla.com
helperx@tuta.io
evromaidan2014@aol.com
cryptor55@cock.li
checkcheck07@qq.com
fox2278@protonmail.com
garryhelpyou@qq.com
duskeer@protonmail.com
Blmmind@tuta.io
crypt@ctemplar.com
ziz777@gmx.com
ndatasafe@airmail.cc
Leviathan13@protonmail.com
Ftworksergey@gmail.com
nkeypass@india.com
octopusdoc@mail.ee
nataliaburduniuc96@gmail.com
jjcrypor@gmail.com
assistance@firemail.cc
care_nlm@tutamail.cc
sqqsdr01@keemail.me
djangounchained@cock.li
jackgreen13@protonmail.com
Averia@tuta.io
file1@techie.com
senha116@keemail.me
Julian.soto@gmail.com
mrcrypt@cock.li
adolfhackler@tutanota.com
blackroot54@protonmail.com
nkeypass@bitmessage.ch
support_blackkingdom2@protonmail.com
meowcorp@onionmail.org
happy_sysadmin@protonmail.ch
Steven77xx@protonmail.com
rescuers@india.com
help.apple@gmail.com
ponce.lorena@aol.com
passsenderdec@gmail.com
rstyle@kaliningrad.ru
warthunder089@mailfence.com
alt.ya-2oxswvd@yopmail.com
AskHeIp@tutanota.com
chily@tuta.io
suspendedfiles@bitmessage.ch
lockhelp@qq.com
antichrist666@tutamail.com
neuro.net@tuta.io
H911X@yahoo.com
cryptsvc@securejabber.me
bigbosshorse@xmpp.jp
Milarepa.lotos@aol.com
ea345@sigaint.org
nfastrecovery@airmail.cc
aes-ni@protonmail.com
Okean-1955@india.com
FilesRecoverDE@Gmail.com
batary5588@protonmail.com
omegax0@protonmail.com
Billy20@4425.com
decrypt@fros.cc
stephanie.jones2024@protonmail.com
Calipso.god@aol.com
nsohigh@jabb.im
heronpiston@xmpp.jp
excuses@protonmail.com
karlosdecrypt24@airmail.cc
y0000@yandex.com
nmanagerhelper@airmail.cc
payadobe@yahoo.com
MerlinWebster@aol.com.com
f1220@mail.ee
bizarrio@venom.io
leo20090707@outlook.com
flowerboard@protonmail.com
herkonasladok@onionmail.org
Nano18@airmail.cc
vassago_0203@tutanota.com
decrypter02@cumallover.me
varasto@firemail.cc
restoremanager@airmail.cc
twovm1iqzi@aol.com
nBatHelp@tutona.com
khalate@protonmail.com
shield0@usa.com
nMayth24@aol.com
zery@tuta.io
mammon0503@protonmail.com
Helprecovery@qbmail.biz
raziotix@tuta.io
decryptadm@criptext.com
CSGVyzko@mail2tor.com
Healforyou@outlook.com
m0nsters-tnc@proton.me
justdoit@msgsafe.io
hnumkhotep@india.com
decrypting-files@yandex.ru
ncammora19@protonmail.com
nmydatarecovery@india.com
bitsupportz@cock.li
Prestige.ranusomeware@Proton.me
helppme@india.com
t314.520@qq.com
rahidproject@secmail.pro
uscodes17@gmail.com
josefrendal797@gmail.com
nEmpty02@yahooweb.co
everest@airmail.cc
chaiRo7u@danwin1210.me
beijingS20@cock.li
bobwhite@msgsafe.io
johny3@mailfence.com
antich154@privatemail.com
ursa2277@bk.ru
darkencryptor@tutanota.com
JamesBaker78@protonmail.com
BM-2cUMY51WfNRG8jGrWcMzTASeUGX84yX741@bitmessage.ch
garryweber@protonmail.ch
creditosantajusta@gmail.com
Patagonoa92@tutanota.com
email-rahuldeeprastogi@gmail.com
databankasi@techmail.info
ndecryption@india.com
datahelper@protonmail.com
wowsmith123456@posteo.net
anoncrack@protonmail.com
sebastiennolet92@gmail.com
eucodes17@gmail.com
n1.kazkavkovkiz@cock.li
Trojan.AiDcrypt@tutanota.com
geneve010@protonmail.com
nmare@cock.li
returndb@airmail.cc
BatHelp@tutona.com
bondbond1@protonmail.com
maya_157_ransom@hotmail.com
sofucked@freespeechmail.org
JamesBaker78@criptext.com
Tizer78224@india.com
r3vo@protonmail.com
mr.yoba@aol.com
payfordecrypt@qq.com
omm72031@yandex.ru
yaga.babushka@yahoo.com
everbe@airmail.cc
s1an1er111@protonmail.com
shellexec@protonmail.com
decryptfiles5@gmail.com
l_abramova@wibor5.ru
keybtc@inbox.com
cricket@tutanota.com
onecrypt@aol.com
dc.dcrypt@cyberfear.com
nProjectJoke@aol.com
datareturn@protonmail.com
sendr@onionmail.org
fixallfiles@tuta.io
Deccripted@gmail.com
Aeghie6u@secmail.pro
neladovin1975@protonmail.com
Masterlock@india.com
pentros30@protonmail.com
Citrteam@tutanota.com
coinsman@tutanota.com
one_weaJc@rows.io
restorefiles@firemail.cc
Leoxrinse234@mailfence.com
amr.almekhlafe@gmail.com
webmafia@asia.com
nhelpmanager@iran.ir
iracomp2@protonmail.ch
mnovazeml@online.ua
decryptmystuff@protonmail.com
pecunia0318@goat.si
more.cce_2020_final@cce2020.kr
frogobigens@india.com
fairman0023@protonmail.com
python2.exe.coder007@protonmail.com
bkpdata@onionmail.org
makedonskiy@india.com
y0000@tuta.io
amundas@firemail.cc
Space_rangers@aol.com
Opensupport@india.com
zaronis@gmx.com
youneedmail@bitmai.la
silasw9pa@yahoo.co.uk
Decfile431@tutanota.com
ndatarestorehelp@airmail.cc
moshiax@aol.com
Peekabooo@qq.com
servicedeskpay@protonmail.com
bitkick@protonmail.com
aid.keepcalm@seznam.cz
nempty01@techmail.info
nzipper@email.tg
yoursalvations@protonmail.ch
fixfiles@protonmail.ch
vote2024forjb@protonmail.com
pausa@india.com
RemotePChelper@cock.li
guifullchartil1970@protonmail.com
eladovin1975@protonmail.com
helpteam38@protonmail.com
8472host@cock.li
mantiticvi1976@protonmail.com
BackFileHelp@protonmail.com
BM-2cX2s3Zoqw9JFc9QELpPPPmuKBGRqF7pL7@bitmessage.ch
kurosaki_ichigo@tutanota.co
sqlbackup3@mail.fr
tenagliamirella@gmail.com
pianist6@protonmail.com
datarestorehelp@airmail.cc
Mrpeterson@cock.li
decrypteasy@protonmail.cc
oymas@gmx.net
randomlocker@tuta.io
cryphelp963@gmail.com
mbrcodes@india.com
hebem@cock.li
slaker@india.com
Decryptallfiles@india.com
abennaki@india.com
support007@mailfence.com
AskHeIp@india.com
decryptfiles@horsefucker.org
SaveYou49@9399.com
helpmanager@airmail.cc
Alice_Malware@thesecure.biz
keysfordencryption@airmail.cc
joshua.mabelin@gmail.com
datebatut@gmail.com
0301192293@protonmail.com
help557@gmx.de
mirey@tutanota.com
brian.r.goodwin@protonmail.com
3048664056@qq.com
xrtnhelp@yandex.ru
nJamesBaker78@protonmail.com
antoniosanches@cock.li
Agella@scryptmail.com
blackpirate@cock.li
Trojan.Win32.crypted_luedtkis@feudtory.com
pulpy2@cock.li
ochennado@tutanota.com
decspeed@tutanota.com
gorentos@firemail.cc
pulpy@cock.li
recover_24_7@protonmail.com
Fud@india.com
FridaFarko@protonmail.com
decripted2017@gmail.com
gagima@gmail.com
nydataback@aol.com
crypted_luedtkis@feudtory.com
amagnus@india.com
oceanm@india.com
jborn@tuta.io
P2DqZHMg28A265z@postheo.de
ik253@email.vccs.edu
rescuer@cock.li
Cryptocash@aol.co
nChina.Helper@aol.com
lafoievologjanin123@protonmail.com
jonskuper578@gmx.de
cybergroup11@aol.com
decryptscrabber@mail.ru
keyforyou@tuta.io
hanesworth.fabian@aol.com
grupposupp@protonmail.ch
room1ahC@secmail.pro.cr
ffgghtdfg@cock.li
fileb@protonmail.com
jewsaintpeople@india.com
behappywithyourdata@airmail.cc
Recoverybat@cock.li
panerai794@gmail.com
vashmail@ctemplar.com
B1tc01n@aol.com
decryptfilekhoda@protonmail.com
postal.surgut@danwin1210.me
Decode@india.com
service@paypal.com
bugbugo@protonmail.com
jj@protonmail.ch
money.doc.coder007@protonmail.com
ccryptor@protonmail.com
host2021@tutanota.com
nvarasto@firemail.cc
decryptgroup@inbox.ru
enter_software@aol.com
team@yahooweb.co
mattpear@protonmail.com
databang2020@protonmail.com
ndesync@airmail.cc
BM-2cXonzj9ovn5qdX2MrwMK4j3qCquXBKo4h@bitmessage.ch
icrypt@cock.li
directreserve@airmail.cc
getscoin2@protonmail.com
vuyrk568gou@lelantos.org
Epta.mcold@gmail.com
adaline.lowell.85@mail.ru
ndogeremembersss@protonmail.ch
che808@protonmail.com
mrddnet_support@protonmail.ch
marjut65@tutanota.com
Cyber_baba2@aol.com
karlosdecrypt@outlook.com
test@matl.com
rimon.argan@gmail.com
Exte3@reddithub.com
anticrypto@protonmail.com
brcode2017@gmail.com
FileEngineering@tutanota.com
teslabrain@cock.li
TagFile_S.txt.coder007@protonmail.com
rickastley@keemail.me
Trojan.help@decrypt-files.info
DataBack@qbmail.biz
decoder83540@cock.li
nblower@india.com
pdfhelp@firemail.cc
unlock.locked.bitlocker@gmail.com
lolitahelp@protonmail.com
my_service@scryptmail.com
intercobros@mailfence.com
suspendedfiles@india.com
middleman2020@protonmail.com
anubi@cock.li
panda7499@gmx.de
Novikov.Vavila@gmail.com
fidel_romposo@aol.com
blackhatcyber789@gmail.com
mr.hacker@tutanota.com
y0000@protonmai1.com
crypto7892@gmx.de
supermax@cock.lu
Support@decrypt.ws
john.perezzka@gmail.com
passcode@gmx.com
n20dfs@keemail.me
xersami@protonmail.com
returndb@airmail.ee
helpDjvut@india.com
psychopath7@tutanota.com
hudsonamily@gmail.com
lechiffre@firemail.cc
gizmo12@tutanota.com
sportdieago@cock.li
codiv2021@tutanota.com
nBM-2cUPRnXJRuFYKcDUCLugjrCPY58nrvHrAV@bitmessage.ch
g8ksw@india.com
mail@mail.ru
waiting@bitmessage.ch
Age_empires@india.com
help@x-mail.pro
nbeijing520@aol.com
InfiniteDecryptor@protonmail.com
HappyNewYear2021@tutanota.com
decrypt_arena@india.com
kevinrobinson@inbox.ru
Lucifer.kobs@mailfence.com
JamesGouldiHip@yahoo.com
pablukl0cker638yzhgr@2tor.com
FlamingoRans@protonmail.com
ooosferaplus@protonmail.com
ramilo2122@yandex.com
back2restore@neomailbox.ch
decryptor171@scramble.io
crypto_wannacash@protonmail.com
coinsman@cock.li
yourfiles1@tutanota.com
Tizer78224@gmx.de
dresdent@protonmail.com
nfahydremu1981@protonmail.com
kts2018@protonmail.com
ndatahelper@protonmail.com
darkwaiderr@gmx.de
pinkiwinki78@mail.ru
dou876sh@tuta.io
xorthelp@yandex.ru
daves.smith@aol.com
decry2@cock.li
SchreiberEleonora@protonmail.com
ndecodedecode@tutanota.com
salutem@protonmail.com
decryptionfiles@gmail.com
btcdecoding@qq.com
mstr.hack@protonmail.com
nmanagersmaers@tutanota.com
onlymoney@firemail.cc
Backuppc@dr.com
nrtddecrypt@airmail.cc
grdoks@tutanota.com
Decryptions@protonmail.com
getscoin3@protonmail.com
l_abramova@festivalps.ru
Centrumfr@india.com
Szems@tutanota.com
iracomp4@protonmail.ch
EpsilonCrypt@tutanota.com
gorentos2@firemail.cc
0x69x@protonmail.com
nrestoremanager@firemail.cc
Gomanje@Indea.info
file@p-security.li
zfile@tuta.io
helpfilerestore@india.com
nhelpshadow@firemail.cc
ZANZIBAR@umpire.com
bad_dev@tuta.io
restorealldata@firemail.cc
burcr@airmail.cc
the.dodger@protonmail.com
RezawyreEdipi1998@o2.pl
price.decoding@aol.com
pskovmama@cock.li
donald888@mail.fr
garantos@mailfence.com
iamcanhelpyou@tuta.io
TwoHearts911@protonmil.com
helpisos@aol.com
gerentosrestore@firemail.cc
install.exe.coder007@protonmail.com
help5555@msgsafe.io
Mich78@usa.com
FreedomTeam@mail.ee
online24files@airmail.cc
China.Helper@aol.com
zdarovachel@gmx.at
sodinsupport@cock.li
WSS911@tutanota.com
robocript@protonmail.ch
ReftuOne@protonmail.com
restorehelp@qq.com
meterpreter@null.net
RestorFile@tutanota.com
Yourhope@airmail.cc
masterdecrypt@openmailbox.org
nhelpyouhelpyou@cock.li
lechiffre@india.com
iamfath3r@protonmail.com
rozlok@protonmail.com
1rest0re@cock.li
retrnyourfiles23@cock.li
backinfo@protonmail.com
dr.decrypt@aol.com
restoredjvu@firemail.cc
felix_dies@aol.com
danielnusradin@gmail.com
Supportvoid@elude.in
rebushelp@protonmail.com
Desparo@tuta.io
acva@foxmail.com
newrecoverybot@pm.me
helpersmasters@airmail.cc
Panzergen552@protonmail.com
dr.nemo@tutanota.com
A_Princ@aol.com
RobertaMacDonald1994@gmail.com
Recoveryhelp2019@protonmail.com
cr1-silvergold1@protonmail.com
aztecdecrypt@protonmail.com
Aileen65@9033.com
vashmail@firemail.cc
kiaracript@email.cz
decrypt24@protonmail.com
the1024rsa@i2pmail.org
homealone@msgden.net
skgrhk2018@tutanota.com
dweezells@airmail.cc
infileshop@gmail.com
blocksupport@tormail.net
dec_helper@excic.com
FHYPOLITE@dallasisd.org
albertkerr94@mail.com
brainfo17@gmail.com
patrik.swize@gmx.de
vine77725@india.com
noceanm@india.com
Ceri133@india.com
esmeraldaencryption@mail.ru
secure5555@msgsafe.io
alphasupport@onionmail.org
SuportOwl@mail2tor.com
kamikizu@onionmail.org
Frank.Sinatra1010@protonmail.com
ICanDecryptYourFiles@cock.li
private-key@foxmail.com
rupp@protonmail.ch
nBackuppc1@protonmail.com
Catsexy@protonmail.com
iizomer@aol.com
decryptgroup@india.com
Backuppc@yandex.com
onimransom@protonmail.com
moloch_helpdesk@protonmail.ch
paydra@cock.li
datarestore@iran.ir
ProjectJoke@aol.com
decodeme666@tutanota.com
nfile1@protonmail.com
ngorentos@firemail.cc
Last_centurion@aol.com
Secure2017@tuta.io
Panzergen552@india.com
grepmord@protonmail.com
ndecoder83540@protonmail.com
vorjdsa@mail.ru
blablacar@airmail.cc
stoneland@firemail.cc
dec_helper@dremno.com
Crptlomand@india.com
dc.dcrypt@mailfence.com
qqxxxxxqq@protonmail.com
nMayth24@tutanota.com
Mail@qbmail.biz
jj.greemsy@mailfence.com
SuzuMcpherson@protonmail.com
nJamesGouldiHip@yahoo.com
Cobra_Locker2.0@protonmail.com
nbeijingS20@cock.li
anon4113@protonmail.com
netakaykakvse@cock.li
inganebieradze@yahoo.com
Bestdecoding@cock.li
g8k4w@india.com
locker@bitmessage.ch
youneedhelp@mail2tor.com
codemanager@fastmail.fm
help@tutanota.com
Sitaram108@india.com
admin@stelsdatas.com
repairdb@seznam.cz
cyberunion@tuta.io.cu
safronov123@tuta.io
Encrypt4u@tutanota.com
unblocked@email.su
rikkibarker@torbox3uiot6wchz.onion
Helps@tutanota.com
Trojan.CottleAkela@protonmail.com
mailnitrom@airmail.cc
ThomasRaymond@protonmail.com
BaYuCheng@yeah.net
help_havaneza@bastardi.net
poeasws@protonmail.com
dfs20@keemail.me
hiddentear@protonmail.com
AbbsChevis@protonmail.com
supportfiless24@protonmail.ch
crypt32@mail.ru
ocode@gmail.com
Malakot@protonmail.com
alexjer554@india.com
onimransom@cock.li
ninfovip@airmail.cc
chinarecoverycompany@cock.li
backfile99@protonmail.com
admin@fentex.net
hebem@tuta.io
savebase@aol.com
python2.7.exe.coder007@protonmail.com
GoldenSunMola@aol.com
Wecanhelp@protonmail.com
your_last_chance@thesecure.biz
roterbro@secmail.pro
decripted@cock.li
contatoarquivoszip@private-mail.com
kamira99@tutanota.com
Helper023@cock.li
Decrypthelp@qq.com
nTara72@1753.com
nAdamBrown89@criptext.com
Makdonalds@india.com
Heinz@oath.com
getyourdata@protonmail.com
oduvansh@aol.com
nikolateslaproton@protonmail.com
kvlly@protonmail.ch
pewpew@TuTa.io
nmiddleman2020@tutanota.com
sos@ausi.com
mary.weston@protonmail.com
horseleader@xmpp.jp
supdecrypt@foxmail.com
unlckr@protonmail.com
filesrestore@tutanota.com
aliseoanal@gmail.com
cryptomavens@eclipso.eu
nFridaFarko@aol.com
pewpew@Protonmail.com
chines34@protonmail.ch
BM-2cT4ifo6SY9QW7gPUJ4EvfeBrJM5jWR4TQ@bitmessage.ch
decryptionfiles@protonmail.com
Xbotcode@gmail.com
filelm@yandex.com
bichkova@cock.li
nAlanRed@criptext.com
BlackMajor@protonmail.com
nAlanRed@tutanota.com
nmerosa@firemail.cc
Wisperado@india.com
safronov@cock.li
ivanmalahov@protonmail.com
achtung_admin@protonmail.com
badhach@aol.com
po2977@protonmail.com
repairdatadochelp@airmail.cc
cuba_support@exploit.im
omygosh@cock.li
prosoft@tutanota.com
bizarrio@pay4me.in
rans_contact@xmpp.jp
Dec_youfile1986@mailfence.com
voice2024forjb@protonniail.com
Ipcrestore@outlook.com
crypthub@tuta.io
officialintuitsoftware@gmail.com
mrbroock@msgsafe.io
Tessa88@exploit.im
lasvegasincel@cocl.li
alexwind46@yahoo.com
alexjer554@gmx.com
Ryabinina.Lina@gmail.com
tuvieja@yopmail.com
support@sysmail.ch
siliconegun@tutanota.com
grupposupp@airmail.cc
IjuqodiSunovib98@o2.pl
bracode17@gmail.com
ransomware@sj.ms
wyattpettigrew8922555@mail.com
cybergroup1@aol.com
baal0625@goat.si
Try2Cry@Indea.info
dfvdv@tutanota.com
Merosa@india.com
backuppc@protonmail.com
Cryptmanager@protonmail.com
haraam@alayam24.net
rdpconnect@protonmail.com
vm1iqzi@aol.com
filesharper@420blaze.it
AlanRed88@protionmail.com
evopro@protonmail.com
GeorjeHalique@protonmail.com
owerhacker@hotmail.com
vendetta553@protonmail.com
auuahk@yandex.com
wmanxtere@privatemail.com
Mayth24@tutanota.com
FilesRecoverEN@Gmail.com
ndecryption@bitmessage.ch
trupm@protonmail.com
mudinuton@gmail.com
artemy75@tutanota.com
meowcorp2022@proton.me
Stopencrypt@qq.com
santino3046@tutanota.de
symetrikk@protonmail.com
nordfox@tutanota.com
PhanthavongsaNeveyah@protonmail.com
hyakunoonigayoru@yahoo.co.jp
file1@keemail.me
suppfirecrypt@qq.com
BaYeCheng@yeah.net
DE_coDER@mail2tor.com
mylifeisfear@cock.li
sieldedamorger@dnmx.org
datahelp@iran.ir
albert9957@protonmail.com
doctor666@cock.li
archive2014.rar.SN-6633475505259148-kiaracript@gmail.com
LeJetepreY0@cock.li
crab1917@protonmail.com
oceannew_vb@protonmail.com
death@cumallover.me
mccredieschlembach@aol.com
keypass@india.com
Citrteam@aol.com
ScorpionEncryption@protonmail.com
Doctor@freelinuxmail.org
Ssimpotashka@gmail.com
nprojectjoke@india.com
Deanna62@5595.com
mikrotik@tutamail.com
Yourencrypter@protonmail.ch
zetterlow@tutanota.com
Sleepme134@gmail.com
FridaFarko@aol.com
montserrat501@airmail.cc
decode00002@gmail.com
undogdianact1986@aol.com
korvin0amber@cock.li
wog@onionmail.info
khalate@tutanota.com
datastor2021@gmail.com
mydataback@aol.com
Bitlocker@foxmail.com
gamigin0612@tutanota.com
support@qbmail.biz
bingo@opensourcemail.org
styver.goodman@aol.com
decrypterdr@cyberfear.com
wtfsupport@airmail.cc
getfilesback013@cock.li
ziz777@india.com
AsuxidOruraep1999@o2.pl
horsedealer@xmpp.jp
alix1011@protonmail.com
hccapx@protonmail.com
unransom@me.com
omnisystems@airmail.cc
blackingdom@gszmail.com
sohigh@jabb.im
mkgoro@india.com
numlock@riseup.net
decryptxxx@protonmail.co
estemaniii@airmail.cc
zorab28@protonmail.com
wlojul@secmail.pro
sociopatii@yahoo.com
dekrypt666@onionmail.org
File2@openmailbox.org
nobad@tutamail.com
bronmerkberpa1976@protonmail.com
filemgr@tutanota.com
Xieth8ie@secmail.pro
torchwood@66.ru
sebekgrime@tutanota.com
DeathSpicy@tutanota.com
file1@openmailbox.org
jessymail26@aol.com
habibi.habibi3@aol.com
Raa-consult1@keemail.me
paycrypt@india.com
Sherminator.help@tutanota.com
helpDjvut@firemail.cc
filekerk@tutanota.com
Swordf1sh@tutanota.com
nvengisto@india.com
ayaan321308@gmail.com
xilttbg@tutanota.com
price.decoding@tutanota.com
paymeme@india.com
geraashurakovv@mail.ru
viper1990@safe-mail.net
nCitrteam@criptext.com
hhaaxxhhaaxx@tuta.io
mr.Ipcap@aol.com
AlanRed@tutanota.com
MasterLuBu@tutanota.com
Tbr66@protonmail.com
muhends@mail.ua
transcript@india.com
datarestorehelp@firemail.cc
quakeway@mail.ru
nBatHelp@india.com
soft.russian@secmail.pro
clifieb@tutanota.com
Cyberwars@qq.com
nAlanRed88@protionmail.com
X280@protonmail.com
buydecryptor@aol.com
Supermagnet@india.com
andresaha82@gmail.com
ondersteuntys@airmail.cc
Lukyan.Sazonov26@gmail.com
gizm0@cock.li
wallyredd@aol.com
Citrteam@criptext.com
triplock@tutanota.com
47rpar-Mail-redem.mikhail17662@gmail.com
rusoftfond@protonmail.com
Adolfo70@5348.com
help244@ya.ru
-kiaracript@gmail.com
nBackuppc@yandex.com
decryptoperator@qq.com
3442516480@qq.com
blackworld@cock.li
horsia@airmail.cc
JanayshaKennin95@mail.com
SupportOdveta@protonmail.com
WildMouse@cock.li
omg-help-me@openmailbox.org
Empty003@protonmail.com
decrypt_.files@mailfence.com
rep_stosd@tuta.io
decodehelp@cock.li
n2.Hariliuios@tutanota.com
Crypt@qbmail.biz
sec222555@gmail.com
rook@onionmail.org
meldung@bsi-bund.org
backuppc1@protonmail.com
nJamesBaker78@criptext.com
Exte1@msgden.net
maddogteam@airmail.cc
backdata.company@aol.com
gangua@torbox3uiot6wchz.onion
Sc0rpio0@tutanota.com
BM-2cTSTDcCD5cNqQ5Ugx4US7momFtBynwdgJ@bitmessage.ch
b4ckuppc2@yandex.com
petersburgrecover@protonmail.com
krastoken@gmail.com
crazykillerusakk@hotmail.com
Ux3oe7ae@secmail.pro
nvengisto@firemail.cc
combo@tutanota.de
cashdashsentme@protonmail.com
btc.com@protonmail.ch
nhelpdjvu@india.com
aztecdecryptor@mailfence.com
adren.kutospov.97@tutanota.com
help73@tutanota.com
F-data@protonmail.com
crab7765@gmx.de
uroo7ohM@secmail.pro
ironsupport@onionmail.org
Decrypt@msgsafe.io
Raptorfiles@yahooweb.co
brcodes16@gmail.com
day_0@aol.com
nsilasw9pa@yahoo.co.uk
Grizzlymail@qq.com
smartrecav@tutanota.com
heineken@tuta.io
cryptoplant@protonmail.com
decryptcrazy@gmail.com
helpdjvu@firemail.cc
vendetta553@india.com
SafeGman@tutanota.com
setestco@protonmail.com
Cobra_Locker@protonmail.com
empty01@techmail.info
getmydata@india.com
blackcilla@cock.li
ngorentos@bitmessage.ch
helpyou2helpyou@cock.li
Recover@8chan.co
secureserver-eu@protonmail.com
encryptadm@criptext.com
8472host@mail.fr
Dsupport@protonmail.com
restoredatahelp@firemail.cc
Sambolero@tutanoa.com
05250lock@tutamail.com
clevercrypt@aol.com
hannesschubert0@gmail.com
Bioawards@gjessmail.com
Decoder_master@india.com
robert.swat@qip.ru
575913661@qq.com
nnaviteam@airmail.cc
johnstang@zoho.eu
jokeroo@protonmail.com
gizm0@tutanota.com
fileig@gtechie.com
silver@decryption.biz.bi
incognitoman@protonmail.com
gomersimpson@keemail.me
blind@cock.li
bruuuuz@yahoo.com
dizelmon@danwin1210.me
abu.khan@india.com
kokoklock@cock.li
blackheel@protonmail.com
loggitore1984@cock.li
mediatorforyou@mail.fr
StuardRitchi@tutanota.com
ny0000@yandex.com
restoring_sup@computer4u.com
michael.adler@swsemarketing.ca
support@decrypt-files.info
fudx@lycos.com
myphoto.jpg.Encrypted_Roblox@mail.com
backdata@cock.li
codyprince92@mail.com
nAdamBrown89@tutanota.com
WannaReneval@goat.si
123@tutanota.com
ap0calypse@india.com
youhaveonechance@cock.li
SafeGman@protonmail.com
recovery1@writeme.com
keepcredit015@protonmail.com
npdfhelp@firemail.cc
legion.developers72@gmail.com
Bitcoinpay@india.com
666lilium666@gmail.com
berserk666@cock.li
trfgklmbvzx@aol.com
databankasi@mail.ru
oktropys@protonmail.com
Decrypt@criptext.com
bkpdata@msgsafe.io
moisha_pt@mailfence.com
TheZenis@Tutanota.com
GruzinRussian@aol.com
ciaprepoulep1977@aol.com
g8k4u@keenail.me
help_911_support@rambler.ru
goodmen@countermail.com
beryukov.mikuil@gmail.com
smartfiles9@yandex.com
Decrptoffice@gmail.com
cryptopatronum@protonmail.com
Filegorilla1388@protonmail.com
Centurion_Legion@aol.com
jessymail26@tuta.io
3335799@protonmail.com
noceanm@engineer.com
decryption@bitmessage.ch
Guardware@india.com
paybit@aol.com
file1@protonmail.com
mishacat@secmail.pro
FileEngineering@mailfence.com
key-support@protonmail.com
paymifordecrypt@protonmail.ch
amazonspurrot1363@gmail.com
soft.russian@protonmail.com
decrypttos@cock.li
lambing.watson@gail.com
datasafe@airmail.cc
vine77725@gmx.de
eR8iech5@danwin1210.me
hildalolilovesyou@airmail.cc
cyber.duskfly@protonmail.com
restoring_reserve@india.com
perdrolan@cock.li
neural.net@tuta.io
davidblaine@mail2world.com
gangflsbang@protonmail.ch
tox@sigaint.org
crydhellsek@gmail.com
kreker@india.com
Savepanda@india.com
wewillhelp@airmail.cc
heetsdecoding@cock.li
foxnitro@aol.com
nhappyness@keemail.me
fox2278@india.com
lion7872@protonmail.com
FobosAmerika@protonmail.ch
mydataback@cock.li
Mespinoza980@protonmail.com
stritinge@gmail.com
iohw634@gmail.com
Phobos.encrypt@qq.co
dec_helper@aol.com
Hiddenhelp@cock.li
big_decryptor@aol.com
Seven_legion@aol.com
ny0000@tuta.io
nCitrteam@tutanota.com
help@decrypt-files.in
decryptgroup@xmpp.jp
satco@tutanota.com
lindsherrod@taholo.co
Blackmax@tutanota.com
Donaldtrump@rapidteamail.com
12334@gmail.com
Wannadecryption@gmail.com
nBlaine98@8771.com
jerjis@tuta.io
Recoverfile@protonmail.com
helpadmin2@cock.li
bot_elite@proton.me
heronpiston@ctemplar.com
UnlockAlexKingman@protonmail.com
William_Kidd_2019@protonmail.com
velasquez.joeli@aol.com
back7@protonmail.ch
cosanostra19@protonmail.com
callmegoat@protonmail.com
spaxl425@aol.com
Hairullah@inbox.lv
justdoit@onionmail.org
kirova-l@wibor5.ru
YpilokOmoadae1994@o2.pl
dataforward@bk.ru
haizenberg@aol.com
tiwa1986@mail.ru
lisasu@elude.in
johndoe@weekendwarrior55.com
pausa@bitmessage.ch
Backdata@zimbabwe.su
noktropys@protonmail.com
Murzik@jabber.mipt.ru
QyavauZehyco1994@o2.pl
ashton8040@msgsafe.io
decryptxxx@protonmail.com
antispam@cyberservices.com
CRIPTON@protonmail.com
Decryptutility@protonmail.com
Payfornature@india.com
tuzadiea@msgsafe.io
Ivan_gargurevich@yahoo.com
Basecrypt@aol.com
Smith1@mailfence.com
Empty02@yahooweb.co
support@p-security.li
prosschiff@gmail.com
burcr@protonmail.com
taargo@olszyn.com
anonimus.mr@yahoo.com
projectjoke@india.com
Usacode@aol.com
info@botontok.uk
beijing520@aol.com
admin@cuba-supp.com
carecaxyz@pm.me
Legioner_seven@aol.com
nExte3@reddithub.com
cammora19@protonmail.com
nhelpdjvu@firemail.cc
Toni.morrison13@tutanota.com.com
belingmor@cock.li
badbusiness@tutanota.de
nrepairdb@seznam.cz
bhacks740@gmail.com
scrabber@mail.ru
worcservice@protonmail.ch
clubnika@cock.li
windows.update@moscowmail.com
dc.dcrypt@tutanota.com
21btc@cock.li
deszyfrator.deszyfr@yandex.ru
sifremicoz@protonmail.com
zipper@email.tg
Rabbit2002@pm.me
nmanager@mailtemp.ch
Backdatacompany@aol.com
c0v1d19@job4u.com
johny2recoveryusa@protonmail.com
Mammon-decrypt@protonmail.com
datareesstore@tutanota.com
allback@tutanota.com
senha120@onionmail.org
batary5588@gmx.com
emrahhalitoglu754@gmail.com
Panama777@tutanota.com
garrantydecrypt@airmail.cc
restoremanager@firemail.cc
avastvirusinfo@yandex.com
zxqwopnm@tutanota.com
stoppiracy@email.su
fahydremu1981@protonmail.com
coinmoney@cock.li
maktoob786@takfir24.net
rsupp@protonmail.ch
Trojan.Bitcharity@protonmail.com.com
nationalsiense@protonmail.com
pabluk700@protonmail.ch
2020@cock.li
tellyouthepass@protonmail.com
patern32@protonmail.com
filerecov3ry@keemail.me
starpex@riseup.net
JoniCarter@protonmail.com
OttoZimmerman@protonmail.ch
projectblack@criptext.com
Howtodecrypt@elude.in
vovabol@inbox.lv
recoverfile@mail2tor.com
Applehelp@caramail.com
file.decrypt@yahoo.com
decryptyourdata@qq.com
djek77d@aol.com
thyrexsuck@cock.li
kurosaki_ichigo@tutanota.com
Orgasm@india.com
codescodes18@gmail.com
datastore2018@mail.ru
Anonymous1@metronet.hr
king.ouroboros@protonmail.com
lnq@protonmail.com
encrypt2020@cock.li
noreply@blogger.com
lokeradmin@cock.li
nswordofsakura@india.com
traher@dr.com
bigbosshorse@ctemplar.com
Happydayz@india.com
cl_crypt@aol.com
blackcilla@qq.com
TomLee240@aol.com
asmodey3301@protonmail.com
buratino@cock.li
johnborn@cock.li
cristmas@india.com
Ahmad26@2336.com
decryptgarranty@airmail.cc
nhelpyou2helpyou@cock.li
cryptsvc@mail.ru
middleman2020@tutanota.com
haraam@takfir24.net
George_Bush@derpymail.org
cryptlocker@tutanota.com
powerhacker03@hotmail.com
sp00f3rsupp0rt@protonmail.com
Salesrestoresoftware@firemail.cc
lioghaly@india.com
RestoreData@airmail.cc
sindragosa@bigmir.net
reserve34@firemail.cc
homersimpson777@mail.fr
coinsman22@cock.li
haunexuwofwuf@protonmail.com
Bitcharity@protonmail.com.com
getcrypt@cock.li
eed8Aeta@danwin1210.me
securityRook@onionmail.org
hinduism0720@tutanota.com
newhelper@protonmail.ch
abramova.l@wibor5.ru
tset@gmail.com
OFFTITAN@cock.li
Fetmyfilesback@airmail.cc
satco@Cock.li
pizdasobaki@protonmail.com
Mr.TeslaBrain@gmail.com
rexplo8sdh1ba6ta18lacue8v9@gmail.com
resoutnowfewminutes@airmail.cc
doctor777@mail.fr
sportdieago@secmail.pro
rtddecrypt@aol.com
Soportevoid@tutanota.com
y.volkova@i-jazz.ru
naes-ni@tuta.io
kkeessnnkkaa@cock.li
borov@foxmail.com
ncryptbit2.0@protonmail.com
gladius_rectus@aol.com
x_mister@aol.com
cryptomadbusiness@protonmail.com
RemotePChelper@protonmail.com
av666@weekendwarrior55.com
loplup@cock.li
Drugvokrug727@india.com
bigphatballss@proton.me
jacklee73@mail.ua
njohny3@mailfence.com
foxnitro@protonmail.com
dr.web24@aol.com
sammer_winter@aol.com
nsavefiles@india.com
barracudahelp@protonmail.com
honestman0023@protonmail.com
viiplusloader@protonmail.com
fastrecovery@airmail.cc
castor-troy-restore@protonmail.com
naviteam@airmail.cc
helpmanager@firemail.cc
maliko@inbox.lv
grandums@gmail.com
crypt302@gmx.com
Goodjob24@foxmail.com
decryptorx@cock.li
irvesely17@onionmail.org
g8k4w@mail.ee
Admincrypt@protonmail.com
nfilelm@yandex.com
french101@india.com
dawndec001@protonmail.com
btckeys@aol.com
fairexchange@qq.com
Enigma1crypt@aol.com
ndecoder83540@cock.li
reverso@qq.com
data_safe@mail.com
AdamBrown89@protonmail.com
freefoams@protonmail.com
GoldenSunMola@cyberfear.com
nstoneland@firemail.cc
noallpossible@cock.li
Bitdefender2020@cock.li
encoderdecryption@gmail.com
nichegolichnogo@airmail.cc
nsupport@sysmail.ch
abat2019@cock.li
decryp7@foxmail.com
aajyjnn64htaosrk@sharklasers.com
supportonl@cock.li
uncrypt2022@outlook.com
abat2019@aol.com
asdqwer123@cock.li
microsoftxyber@hackindex.com
recoverydata52@protonmail.com
RomanchukEyla@protonmail.com
allhelp16@gmail.com
Helpcrypt1@tutanota.com
tuyuljahat@hotmail.com
cryptolifeguard@cock.li
naviteam@aol.com
meowcorp2022@aol.com
dr.help100@mailfence.com
reasonablehelp@outlook.com
lwei@malwarebytes.com
paycrypt@aol.com
happydataowner@firemail.cc
harmagedon0707@airmail.cc
-paycrypt@aol.com
Nomoneynohoney@india.com
under_amur@protonmail.ch
nDeanna62@5595.com
Dcr@cumallover.me
alexwind46@aol.com
momsbestfriend@protonmail.com
9ea6e85bd12b@tutanota.com
VladimirScherbinin1991@gmail.com
openpgp@foxmail.com
nordfox@aol.com
aihlp24@tuta.io
itstome@cock.li
octopusdoc@airmail.cc
Files2020@mailfence.com
anna_stepanova@aol.com
axitrun@cock.li
160505@tt3j2x4k5ycaa5zt.onion
4reserve@tuta.io
pskovmama@secmail.pro
unlock0101@protonmail.com
nyougame@protonmail.ch
pol.aris@opentrash.com
ncobainOransom@cock.li
nsupport@bestyourmail.ch
deltatechit@protonmail.com
lovelife@xabber.org
letitbedecryptedzi@gmail.com
yougame@protonmail.ch
rapid.file@tuta.io
leenapidx@snakebite.com
piterpen02@keemail.me
charmant@firemail.cc
flsunlocker@yahoo.com
Trojan.estemaniii@airmail.cc
bereznikdown@firemail.cc
khiwosang@gmail.com
unlockdata@foxmail.com
panda7499@india.com
ursa2277@india.com
Trojan.Merosa@india.com
Matrix9643@yahoo.com
2.Hariliuios@tutanota.com
pouranesd@cliptik.net
some@mail.ru
pilotpilot088@gmail.com
djang0unchain3d@protonmail.com
Helpassistant2120@mail.fr
helpforyou@firemail.cc
rdpmanager@airmail.cc
SafeGman@protonmail.co
datarecovery@airmail.cc
painplain98@protonmail.com
gentilpascal@bitmessage.ch
Vitaly.Yermakov@protonmail.com
allback@cock.li
file1m@yandex.com
redboot@memeware.net
Phobos.encrypt@qq.com
2020@outlook.com
1_kill_yourself_1@protonmail.com
Asuxid0ruraep1999@o2.pl
helpmanager@mail.ch
davidblainemagique@gmail.com
ghjujy@tuta.io
nblower@firemail.cc
moloch_helpdesk@tutanota.com
UneGarc0n1@cock.li
Santa_helper@protonmail.com
ostashkinpp@gmail.com
Cryfixfoo@qq.com
Pdfhelp@india.com
spystar1@onionmail.com
databack2@protonmail.com
Mk_cyrox@aol.com
Thedon78@mail.com
Decryptoffice@tuta.io
QicifomuEjijika@o2.pl
datebatut@pochta.com
recoverydata98@protonmail.com
oceanm@engineer.com
A654763764@qq.com
b4ckuppc1@yandex.com
nAhmad26@2336.com
xp10.ransom@gmail.com
helper@bitmessage.ch
paydecryption@qq.com
filesreturn247@protonmail.com
abramova@sabona.ru
Mr.TeslaBrain@protonmail.com
faremar@cock.li
selenadymond@gmail.com
intercobros@protonmail.com
fabianwosar@inbox.ru
restoredjvu@india.com
trunhelp@yandex.ru
mcrypt2019@yandex.com
debri@keemail.me
JamesBaker78@tutanota.com
comodosec@india.com
Blackdragon43@yahoo.com
gold84@cock.li
data1992@protonmail.com
supl0@oath.com
nphrasitliter1981@protonmail.com
nsupl0@post.com
return.data@qq.com
3475857701@qq.com
badbeeteam@mail.cc
unblocked@tuta.io
cryptservice@jabber.ua
bichkova@secmail.pro
BCPFILE17@tutanota.com
masterlrestore@cock.li
muhendis@mail.ua
bbqb@protonmail.com
decryption@qbmail.biz
null_ptr@tutanota.de
n0405000330@inbox.ru
legalrestore@airmail.cc
CouwetIzotofo@o2.pl
Mayth24@aol.com
Decrypter@msgsafe.io
godecrypt@onionmail.org
MayarChenot@protonmail.com
incantofiles@india.com
goodmen@cock.li
viethckr@yandex.com
SafeGman@firemail.cc
nservicedigilogos@protonmail.com
mr.leen@protonmail.com
FilesRecoverFR@Onionmail.org
Repairme2017@keemail.me
doctorhelp2120@cock.li
filesreturn247@gmx.de
random_anonymous@gmail.com
skynet45@cock.li
helpnetin@protonmail.com
VovanAndLexus@cock.li
jokeroo@exploit.im
file1n@yandex.com
FileRec69@mailfence.com
adminsysloker@airmail.cc
1rest0re@protonmail.com
helpmeonce@mail.ru
helprestoremanager@airmail.cc
bobwhite@cock.li
Lavandos@dr.com
support@robsmithmba.com
nmediatorforyou@mail.fr
incongnitoman@protonmail.com
flower.harris@tutanota.com
Buydecrypt@qq.com
brcodes17@gmail.com
Starbax@tutanota.com
help@inboxhub.net
decrypt.russ@protonmail.com
mykeyhelp@protonmail.com
black.mirror@qq.com
mewellwisher@protonmail.ch
btc.fresh01@gmail.com
Sc0rpio@mailfence.com
Suppteam01@india.com
6ix9@asia.com
nChina.Helper@india.com
7399@sigaint.org
nkhalate@tutanota.com
Zagrec@protonmail.com
new_wave@tuta.io
supporthelp@airmail.cc
BM-2cUPRnXJRuFYKcDUCLugjrCPY58nrvHrAV@bitmessage.ch
AdminOwl@bitmessage.de
05250lock@tut.com
Cocoslim98@gmail.com
name4v@keemail.me
tset2@gmail.com
merosadecryption@gmail.com
infokey24@india.com
schusterboss@cock.li
paradisecity@cock.li
Wbgroup022@gmail.com
File.decrypt@onionmail.org
bitcoins12@tutanota.com
g.kulahmet@secmail.pro
k.nishant@itorizin.in
ix@hotmail.com
nrecoverydata@india.com
nginxhole@tutanota.com
firmadatalari@mail.ru
vapeefiles@aol.com
lechiffre@mailchuck.com
nBM-2cXonzj9ovn5qdX2MrwMK4j3qCquXBKo4h@bitmessage.ch
nhelpshadow@india.com
restoresales@airmail.cc
ZaszyfrowanePliki@ZaszyfrowanePliki.us
cmdroot@airmail.cc
info@morris2uk.com
desktopman228@india.com
Billy11@4302.com
ursa2277@yahoo.com
sherlokcock@cock.li
fast_decrypt_and_protect@tutanota.com
files640@gmail.com
szem@tutanota.com
Funox@ya.ru
needhelp@disroot.org
padredelicato@cock.li
Bnd54@mail2tor.com
support4you@protonmail.com
RobSmithMba@protonmail.com
iron@techmail.info
hto2018@yandex.ru
keypass@bitmessage.ch
kesoma32@horsefucker.org
savefiles@india.co
reverso@cock.li
fox2278@gmx.de
w3qupe@tuta.io
abka1001@gmail.com
stopfilesrestore@bitmessage.ch
dekode@qq.com
belgorod8712kozos@dnmx.org
backuppc1@dr.com
de.picocode@gmail.com
repairdb@mail.fr
managersmaers@tutanota.com
Zeman@tutanota.de
mosteros@firemail.cc
clubnika@elude.in
FileEngineering@elude.in
Systemdown@india.com
help24decrypt@qq.com
anton_ivan_8989@mail.ru
TomLee24@tuta.io
siniyzabor@protonmail.com
soetrisno.bachir@kein.go.id
Dercypt@protonmail.com
Noreply@kpnmail.eu
Sw0rdf1sh@cock.li
bufalo@firemail.cc
bkp@cock.li
JohnPennegZZ@aol.com
healforyou@cock.li
loybranunun1975@protonmail.com
LR_FWS_H2M_ET@protonmail.ch
d3g1d5@gmail.com
secres@gmx.de
divo21mir@cock.li
52pojie_mail@protonmail.com
kuk1@tuta.io
Look1213@protonmail.com
gervasiy.menyaev@gmail.com
ICanFixYourFiles@tutanota.com
security11220@gmail.com
JeanRenoAParis@protonmail.com
chinarecoverycompany@airmail.cc
Unlockmeplease@cock.li
chily65@proton.me
yeahdesync@airmail.cc
kronstar21@gmail.com
de_cryption@tuta.io
blockage@tormail.org
LindaHunter474@gmail.com
nhelpmanager@mail.ch
decryptor911@airmail.cc
artemy75@protonmail.com
dmo9o4zB@protonmail.com
wilhelmkox@tutanota.com
fedelsupportagent@cock.li
paydear@aol.com
lafoievologjanin123@tutanota.com
anony.killers@protonmail.com
CyberSCCP@protonmail.com
Info@fugunator.de
Logan8833@aol.com
nMayth24@protonmail.com
tuhafcoderus@protonmail.com
wayneevenson@protonmail.com
filel@keemail.me
Bit_decrypt@protonmail.com
Pumarestore@india.com
aq811@tutoanota.com
rtddecrypt@airmail.cc
fonix@tuta.io
plague17@riseup.net
lewisswaffield.a@aol.com
logical.disk@yandex.com
unlockme123@protonmail.com
vauvau@cock.li
crypthelp@qq.com
carnovaleimpres@dnmx.org
synack@secmail.pro
answer@pcworld.com
berne.fiddell@aol.com
Rcru64@cock.lu
lovelife@cumallover.me
tools1990m@gmail.com
aoneder@mail.ru
jonskuper578@protonmail.com
Payransom@qq.com
Trojan.QyavauZehyco1994@o2.pl
decryptmefinger@gmail.com
backuppc@tuta.io
nAskHeIp@tutanota.com
decrypt_.files@cyberfear.com
paymeme@cock.li
nomoreletters@protonmail.ch
nHelpassistant2120@mail.fr
helpdjvu@india.com
Batman_good@aol.com
crypt31@proton.me
nginxhole@gjessmail.com
blower@india.com
Grizzly@airmail.cc
email-iizomer@aol.com
aam_sysadmin@protonmail.com
technopc@tutanota.com
maxidecrypt@protonmail.com
execute@protonmail.com
datadecryption@countermail.com
crab1917@gmx.de
hepl1112@aol.com
datarest0re@xmpp.jp
koxic@protonmail.com
master1restore@cock.li
nmanager@time2mail.ch
decrypt@files.mn
french101@protonmail.ch
email1_info@cryptedfiles.biz
maill_helpme@protonmail.com
rx99@cock.li
Trojan.Win64.CottleAkela@protonmail.com
nenter_software@aol.com
abc@countermail.com
mishacat@cock.li
ndec_helper@aol.com
HanzOttoschmidt@protonmail.com
logiteam@protonmail.com
decryptex@airmail.cc
Myfiles.sir@gmail.com
crossroads2371@protonmail.ch
ucos2@elude.in
CottleAkela@protonmail.com
nullforwarding@qualityservice.com
Veracrypt@india.com
jbomani@protonmail.com
nmode@tutanota.com
motox2016@mail2tor.com
xiaoba_666@163.com
cryptservice@inbox.ru
nBilly20@4425.com
infovip@airmail.cc
document2.txt.SN-6862051502902366-kiaracript@gmail.com
error-crypt@protonmail.com
ops@mailc.net
AdamBrown89@tutanota.com
Partytime123@default.rs
infocrypt@india.com
Love.server@mail.ru
Buddy@criptext.com
carnovaleimpres@cock.li
backtonormal@foxmail.com
no.xm@protonmail.ch
rikyrank113@protonmail.com
beijing520@cock.li
onionhunter@onionmail.org
decrsup@cock.li
juniorwanme@tutanota.com
nsupportsys@airmail.cc
ht2707@email.vccs.edu
jimmtheworm@dicksinmyan.us
nhelprestore@firemail.cc
xser@tutanota.com
decoder83540@protonmail.com
karapooz@secmail.pro
Mayth24@protonmail.com
trueransom@mail2tor.com
systemsupport@memeware.net
Devicerestore@india.com
vpsimf@gmail.com
dorispackman@tuta.io
Billwong73@yahoo.com
Blaine98@8771.com
cryptlive@aol.com
payoff@bigmir.net
zip@email.tg
robocript@gmx.us
cobain_ransom@protonmail.com
hildaseriesnetflix125@horsefucker.org
fantomd12@yandex.ru
rapidka@cock.li
brianmaps@gmail.com
decrypting@tormail.org
Xtredboy@protonmail.com
nnydataback@aol.com
yourfiles1@cock.li
manager@mailtemp.ch
datadecryption@bitmessage.ch
goodencrypt88@gmail.com
back_me@foxmail.com
Decryptionsupport911@airmail.cc
helpasia16@gmail.com
datarc89@cyberfear.com
nhealforyou@cock.li
Melme@india.com
doctor666@mail.fr
nomnisystems@airmail.cc
Grand_car@aol.com
BM-2cVCMjYXg5ZwLi2t6mETUeQYhMNDmbfFA2@bitmessage.ch
warthunder089@tutanota.de
nsupport@robsmithmba.com
datadecryption@india.com
nunlckr@protonmail.com
supportonl@airmail.cc
AdamBrown89@criptext.com
Keyfiles@cock.li
supportsys@airmail.cc
nfilekerk@tutanota.com
recoverymydata@protonmail.com
bitlockerlock.unlock@gmail.com
ShadowofDeath@elude.in
H0lyGh0st@mail2tor.com
Admin@decryption.biz
jonskuper578@india.com
mr.crypt@aol.com
Helpsdec@tutanota.com
fa5d9dfc@gwisin4yznpdtzq424i3la6oqy5evublod4zbhddzuxcnr34kgfokwad.onion
agent5305@firemail.cc
blackbyte@onionmail.org
devilguy666@protonmail.com
leesb@coscokorea.com
Supportfriend@india.com
vcredist.bmp.coder007@protonmail.com
unixc47@gmail.com
uff1a52pojie_mail@protonmail.com
nanonimus.mr@yahoo.com
Hellstaff@india.com
brovsky@aol.com
Bitcoinrush@imail.com
Trojan.Win32.QyavauZehyco1994@o2.pl
krupalupium@india.com
helpteam@mail.ch
NetGanster@protonmail.com
archive2010.zip.SN-6633475505259148-kiaracript@gmail.com
helpadmin2@protonmail.com
imBoristheBlade@protonmail.com
nordfox@protonmail.com
badbeeteam@cock.li
xzet@tutanota.com
4lok3r@protonmail.com
Siddhiup2@india.com
mr.dec@protonmail.com
SecurCyber@yahoo.com
decrypt@techie.com
returndb@seznam.cz
nBackuppc@protonmail.com
MilesFlannagan@protonmail.com
Restore@protonmail.ch
bigboss@thesecure.biz
Trojan.crypted_luedtkis@feudtory.com
DutyuEnugev89@o2.pl
restorefiles@protonmail.ch
supportdoctor@protonmail.com
Killback@protonmail.com
SupportOdveta@elude.in
pol.aris@tutanota.com
ferast@firemail.cc
Sample Protonmail email address accounts known to have been involved in various ransomware themed campaigns include:
Brilliancebk@protonmail.com
nCyberwars@protonmail.com
pentaxyz777@protonmail.com
hacker_decryption@protonmail.ch
iknowyouandiseeyou@protonmail.ch
recoverydata99@protonmail.com
Bossi_tosi@protonmail.com
FreeWizard9@protonmail.com
Blitzkriegpc@protonmail.com
05250lock@protonmail.com
westlan@protonmail.ch
geniusid@protonmail.ch
flower.harris@protonmail.com
t310ea89b4347@protonmail.com
phrasitliter1981@protonmail.com
technopc@protonmail.com
nCobra_Locker@protonmail.com
montserrat501@protonmail.com
BTCBREWERY@protonmail.com
spaxl425@protonmail.com
petrov441@protonmail.com
fmhir@protonmail.com
nrecoverymydata@protonmail.com
tomascry@protonmail.com
filedownload2020@protonmail.com
Deccoder431@protonmail.com
nRobSmithMba@protonmail.com
Lizardbkup@protonmail.com
ncrab1917@protonmail.com
Recuperadados@protonmail.com
ncrypto7892@protonmail.com
TimisoaraHackerTeam@protonmail.com
DecrypterSupport@protonmail.com
RECOVERUNKNOWN@protonmail.com
vashmail@protonmail.com
geneve020@protonmail.com
recfiles@protonmail.com
n0301192293@protonmail.com
doctorSune@protonmail.com
crypto7892@protonmail.com
dogeremembersss@protonmail.ch
nEmpty003@protonmail.com
EMAIL@protonmail.com
fixprotectvvv@protonmail.com
johnsonwhate@protonmail.com
decodeodveta@protonmail.com
j0ra@protonmail.com
myphoto.jpg.nefartanulo@protonmail.com
andrey.taranov@protonmail.com
rescuerr@protonmail.com
Cyberwars@protonmail.com
ncrab7765@protonmail.com
china_jm@protonmail.ch
m4xroothackerteam@protonmail.com
loggitore1984@protonmail.com
Corpseworm@protonmail.com
dec.service@protonmail.com
dcyptfils@protonmail.ch
lxhlp@protonmail.com
quiddoss@protonmail.com
nefartanulo@protonmail.com
youneedmail@protonmail.com
kfrvokr@protonmail.ch
help73@protonmail.com
softs98@protonmail.com
Recoverybat@protonmail.com
aid.keepcalm@protonmail.com
SayanWalsworth96@protonmail.com
universe1@protonmail.ch
alexwind46@protonmail.com
uff1aitunes_decrypt@protonmail.com
burgeer@protonmail.ch
nExte2@protonmail.com
JinMaglaya@protonmail.com
recover85@protonmail.com
Trojan.Win64.Bitcharity@protonmail.com.com
n0x69x@protonmail.com
blackgoldl23@protonmail.com
BatHelp@protonmail.com
ndecoder-help@protonmail.com
nnomoreletters@protonmail.ch
fun63s@protonmail.com
bsprj1020@protonmail.com
decrypt25@protonmail.com
recovery.company@protonmail.com
fileisafe@protonmail.com
nguifullchartil1970@protonmail.com
gluttonBD@protonmail.com
cryptomavens@protonmail.com
decoder-help@protonmail.com
panda7499@protonmail.com
mailnitrom@protonmail.ch
newneo1312@protonmail.com
hlpp@protonmail.ch
Tizer77234@protonmail.com
cryptgh0st@protonmail.com
egalytyy@protonmail.com
cryptbit2.0@protonmail.com
decrypt01.cq@protonmail.com
telegramfirefox2029@protonmail.com
servicedigilogos@protonmail.com
Nowayout@protonmail.com
niggapoopool23@protonmail.com
DharmaParrack@protonmail.com
naes-ni@protonmail.com
Datarest0re@protonmail.com
eula.2052.txt.coder007@protonmail.com
nFridaFarko@protonmail.com
Honeylock@protonmail.com
flapalinta1950@protonmail.com
Exte2@protonmail.com
pulpy@protonmail.ch
wwxxxxxww@protonmail.com
crab7765@protonmail.com
bitsupportz@protonmail.com
ex_parvis@protonmail.com
AskHeIp@protonmail.com
getthefiles2@protonmail.ch
a11back@protonmail.ch
windat@protonmail.com
g.kulahmet@protonmail.com
nmiddleman2020@protonmail.com
rep_stosd@protonmail.com
newhelper24@protonmail.ch
python.exe.coder007@protonmail.com
btc_bitts@protonmail.com
nAdamBrown89@protonmail.com
DecryptFox@protonmail.com
AdvancedBackup@protonmail.com
vine77725@protonmail.com
reservedecryption@protonmail.com
Filedecryptor@protonmail.com
itunes_decrypt@protonmail.com
xaodecrypt@protonmail.com
fox2278@protonmail.com
duskeer@protonmail.com
Leviathan13@protonmail.com
jackgreen13@protonmail.com
blackroot54@protonmail.com
support_blackkingdom2@protonmail.com
happy_sysadmin@protonmail.ch
Steven77xx@protonmail.com
aes-ni@protonmail.com
batary5588@protonmail.com
omegax0@protonmail.com
stephanie.jones2024@protonmail.com
excuses@protonmail.com
flowerboard@protonmail.com
khalate@protonmail.com
mammon0503@protonmail.com
ncammora19@protonmail.com
JamesBaker78@protonmail.com
garryweber@protonmail.ch
datahelper@protonmail.com
anoncrack@protonmail.com
geneve010@protonmail.com
bondbond1@protonmail.com
r3vo@protonmail.com
s1an1er111@protonmail.com
shellexec@protonmail.com
datareturn@protonmail.com
neladovin1975@protonmail.com
pentros30@protonmail.com
iracomp2@protonmail.ch
decryptmystuff@protonmail.com
fairman0023@protonmail.com
python2.exe.coder007@protonmail.com
servicedeskpay@protonmail.com
bitkick@protonmail.com
yoursalvations@protonmail.ch
fixfiles@protonmail.ch
vote2024forjb@protonmail.com
guifullchartil1970@protonmail.com
eladovin1975@protonmail.com
helpteam38@protonmail.com
mantiticvi1976@protonmail.com
BackFileHelp@protonmail.com
pianist6@protonmail.com
decrypteasy@protonmail.cc
0301192293@protonmail.com
brian.r.goodwin@protonmail.com
nJamesBaker78@protonmail.com
recover_24_7@protonmail.com
FridaFarko@protonmail.com
lafoievologjanin123@protonmail.com
grupposupp@protonmail.ch
fileb@protonmail.com
decryptfilekhoda@protonmail.com
bugbugo@protonmail.com
jj@protonmail.ch
money.doc.coder007@protonmail.com
ccryptor@protonmail.com
mattpear@protonmail.com
databang2020@protonmail.com
getscoin2@protonmail.com
ndogeremembersss@protonmail.ch
che808@protonmail.com
mrddnet_support@protonmail.ch
anticrypto@protonmail.com
TagFile_S.txt.coder007@protonmail.com
lolitahelp@protonmail.com
middleman2020@protonmail.com
xersami@protonmail.com
InfiniteDecryptor@protonmail.com
FlamingoRans@protonmail.com
ooosferaplus@protonmail.com
crypto_wannacash@protonmail.com
dresdent@protonmail.com
nfahydremu1981@protonmail.com
kts2018@protonmail.com
ndatahelper@protonmail.com
SchreiberEleonora@protonmail.com
salutem@protonmail.com
mstr.hack@protonmail.com
Decryptions@protonmail.com
getscoin3@protonmail.com
iracomp4@protonmail.ch
0x69x@protonmail.com
the.dodger@protonmail.com
install.exe.coder007@protonmail.com
robocript@protonmail.ch
ReftuOne@protonmail.com
iamfath3r@protonmail.com
rozlok@protonmail.com
backinfo@protonmail.com
rebushelp@protonmail.com
Panzergen552@protonmail.com
Recoveryhelp2019@protonmail.com
cr1-silvergold1@protonmail.com
aztecdecrypt@protonmail.com
decrypt24@protonmail.com
Frank.Sinatra1010@protonmail.com
rupp@protonmail.ch
nBackuppc1@protonmail.com
Catsexy@protonmail.com
onimransom@protonmail.com
moloch_helpdesk@protonmail.ch
nfile1@protonmail.com
grepmord@protonmail.com
ndecoder83540@protonmail.com
qqxxxxxqq@protonmail.com
SuzuMcpherson@protonmail.com
Cobra_Locker2.0@protonmail.com
anon4113@protonmail.com
Trojan.CottleAkela@protonmail.com
ThomasRaymond@protonmail.com
poeasws@protonmail.com
hiddentear@protonmail.com
AbbsChevis@protonmail.com
supportfiless24@protonmail.ch
Malakot@protonmail.com
backfile99@protonmail.com
python2.7.exe.coder007@protonmail.com
Wecanhelp@protonmail.com
getyourdata@protonmail.com
nikolateslaproton@protonmail.com
kvlly@protonmail.ch
mary.weston@protonmail.com
unlckr@protonmail.com
chines34@protonmail.ch
decryptionfiles@protonmail.com
BlackMajor@protonmail.com
ivanmalahov@protonmail.com
achtung_admin@protonmail.com
po2977@protonmail.com
backuppc@protonmail.com
Cryptmanager@protonmail.com
rdpconnect@protonmail.com
evopro@protonmail.com
GeorjeHalique@protonmail.com
vendetta553@protonmail.com
trupm@protonmail.com
symetrikk@protonmail.com
PhanthavongsaNeveyah@protonmail.com
albert9957@protonmail.com
crab1917@protonmail.com
oceannew_vb@protonmail.com
ScorpionEncryption@protonmail.com
Yourencrypter@protonmail.ch
alix1011@protonmail.com
hccapx@protonmail.com
decryptxxx@protonmail.co
zorab28@protonmail.com
bronmerkberpa1976@protonmail.com
Tbr66@protonmail.com
X280@protonmail.com
rusoftfond@protonmail.com
SupportOdveta@protonmail.com
Empty003@protonmail.com
backuppc1@protonmail.com
petersburgrecover@protonmail.com
cashdashsentme@protonmail.com
btc.com@protonmail.ch
F-data@protonmail.com
cryptoplant@protonmail.com
setestco@protonmail.com
Cobra_Locker@protonmail.com
secureserver-eu@protonmail.com
Dsupport@protonmail.com
jokeroo@protonmail.com
incognitoman@protonmail.com
blackheel@protonmail.com
SafeGman@protonmail.com
keepcredit015@protonmail.com
oktropys@protonmail.com
cryptopatronum@protonmail.com
Filegorilla1388@protonmail.com
3335799@protonmail.com
file1@protonmail.com
key-support@protonmail.com
paymifordecrypt@protonmail.ch
soft.russian@protonmail.com
cyber.duskfly@protonmail.com
gangflsbang@protonmail.ch
lion7872@protonmail.com
FobosAmerika@protonmail.ch
Mespinoza980@protonmail.com
Recoverfile@protonmail.com
UnlockAlexKingman@protonmail.com
William_Kidd_2019@protonmail.com
back7@protonmail.ch
cosanostra19@protonmail.com
callmegoat@protonmail.com
noktropys@protonmail.com
decryptxxx@protonmail.com
CRIPTON@protonmail.com
Decryptutility@protonmail.com
burcr@protonmail.com
cammora19@protonmail.com
worcservice@protonmail.ch
sifremicoz@protonmail.com
johny2recoveryusa@protonmail.com
Mammon-decrypt@protonmail.com
fahydremu1981@protonmail.com
rsupp@protonmail.ch
Trojan.Bitcharity@protonmail.com.com
nationalsiense@protonmail.com
pabluk700@protonmail.ch
tellyouthepass@protonmail.com
patern32@protonmail.com
JoniCarter@protonmail.com
OttoZimmerman@protonmail.ch
king.ouroboros@protonmail.com
lnq@protonmail.com
asmodey3301@protonmail.com
sp00f3rsupp0rt@protonmail.com
haunexuwofwuf@protonmail.com
Bitcharity@protonmail.com.com
newhelper@protonmail.ch
pizdasobaki@protonmail.com
ncryptbit2.0@protonmail.com
cryptomadbusiness@protonmail.com
RemotePChelper@protonmail.com
foxnitro@protonmail.com
barracudahelp@protonmail.com
honestman0023@protonmail.com
viiplusloader@protonmail.com
castor-troy-restore@protonmail.com
Admincrypt@protonmail.com
dawndec001@protonmail.com
AdamBrown89@protonmail.com
freefoams@protonmail.com
recoverydata52@protonmail.com
RomanchukEyla@protonmail.com
under_amur@protonmail.ch
momsbestfriend@protonmail.com
unlock0101@protonmail.com
nyougame@protonmail.ch
deltatechit@protonmail.com
yougame@protonmail.ch
djang0unchain3d@protonmail.com
SafeGman@protonmail.co
painplain98@protonmail.com
Vitaly.Yermakov@protonmail.com
1_kill_yourself_1@protonmail.com
Santa_helper@protonmail.com
databack2@protonmail.com
recoverydata98@protonmail.com
filesreturn247@protonmail.com
Mr.TeslaBrain@protonmail.com
intercobros@protonmail.com
data1992@protonmail.com
nphrasitliter1981@protonmail.com
bbqb@protonmail.com
MayarChenot@protonmail.com
nservicedigilogos@protonmail.com
mr.leen@protonmail.com
helpnetin@protonmail.com
1rest0re@protonmail.com
incongnitoman@protonmail.com
decrypt.russ@protonmail.com
mykeyhelp@protonmail.com
mewellwisher@protonmail.ch
Zagrec@protonmail.com
support4you@protonmail.com
RobSmithMba@protonmail.com
siniyzabor@protonmail.com
Dercypt@protonmail.com
loybranunun1975@protonmail.com
LR_FWS_H2M_ET@protonmail.ch
52pojie_mail@protonmail.com
Look1213@protonmail.com
JeanRenoAParis@protonmail.com
artemy75@protonmail.com
dmo9o4zB@protonmail.com
anony.killers@protonmail.com
CyberSCCP@protonmail.com
nMayth24@protonmail.com
tuhafcoderus@protonmail.com
wayneevenson@protonmail.com
Bit_decrypt@protonmail.com
unlockme123@protonmail.com
jonskuper578@protonmail.com
nomoreletters@protonmail.ch
aam_sysadmin@protonmail.com
maxidecrypt@protonmail.com
execute@protonmail.com
koxic@protonmail.com
french101@protonmail.ch
maill_helpme@protonmail.com
Trojan.Win64.CottleAkela@protonmail.com
HanzOttoschmidt@protonmail.com
logiteam@protonmail.com
crossroads2371@protonmail.ch
CottleAkela@protonmail.com
jbomani@protonmail.com
error-crypt@protonmail.com
no.xm@protonmail.ch
rikyrank113@protonmail.com
decoder83540@protonmail.com
Mayth24@protonmail.com
cobain_ransom@protonmail.com
Xtredboy@protonmail.com
nunlckr@protonmail.com
recoverymydata@protonmail.com
devilguy666@protonmail.com
vcredist.bmp.coder007@protonmail.com
uff1a52pojie_mail@protonmail.com
NetGanster@protonmail.com
helpadmin2@protonmail.com
imBoristheBlade@protonmail.com
nordfox@protonmail.com
4lok3r@protonmail.com
mr.dec@protonmail.com
nBackuppc@protonmail.com
MilesFlannagan@protonmail.com
Restore@protonmail.ch
restorefiles@protonmail.ch
supportdoctor@protonmail.com
Killback@protonmail.com
Sample Tutanota personal email address accounts known to have been involved in various ransomware themed campaigns include:
dokulus@tutanota.com
legalrestore@tutanota.com
alexbanan@tuta.io
remotePChelper@tutanota.com
f1220@tuta.io
cryptget@tutanota.com
recoryfile@tutanota.com
hallome@tutanota.com
hitsbtc@tuta.io
sill@tuta.io
black.world@tuta.io
nBioawards@tutanota.com
berserk666@tutanota.com
decrfile@tutanota.com
mr.dec@tutanota.com
loggitore1984@tuta.io
mailnitrom@tutanota.com
Bioawards@tutanota.com
neftet@tutanota.com
hildaseriesnetflix125@tutanota.com
gorkmork@tutanota.de
monster666@tuta.io
goldmind@tuta.io
fileisafe@tuta.io
Decrpt@tutanota.com
Trojan.Win64.AiDcrypt@tutanota.com
Light_Yagami@tuta.io
developer.110@tutanota.com
coding_434@tutanota.com
frankhans@tuta.io
darkwaiderr@tutanota.com
johnsmith987654@tutanota.com
Files2021@tutanota.com
AiDcrypt@tutanota.com
Decisivekey@tutanota.com
aes-ni@tuta.io
sendr@tutanota.com
biggsurprise@tutanota.com
Zizz@tutanota.de
Merd@tutanota.com
garrymagic@tutanota.com
jakie.nunes@tutanota.com
n3tw0rm@tuta.io
skgrhk2018me@tutanota.com
jacdecr@tuta.io
pecunia0318@tutanota.com
pabpabtab@tuta.io
getacrypt@tuta.io
HydaHelp1@tutanota.com
FilesHelp@tutanota.com
alphareserve@tuta.io
systems@tutanota.com
4lok3r@tutanota.com
axitrun2@tutanota.com
johnsonwhate@tutanota.com
decodedecode@tutanota.com
beryl.mclennan@tutanota.de
Stevensons@tuta.io
nJamesBaker78@tutanota.com
yuzhou13@tutanota.com
grethen@tuta.io
foxnitro@tutanota.com
retrnyoufiles@tutanota.com
InkognitoMan@tutamail.com
colambia@tutanota.com
mmm_reborn@tutamail.com
FlamingoRans@tutamail.com
internationalassistance@tutanota.com
klowershit1835@tutanota.com
cavefat@tuta.io
jerjis@tutamail.com
blacknord@tutanota.com
pixell@tutanota.com.ph
helperx@tuta.io
Blmmind@tuta.io
care_nlm@tutamail.cc
Averia@tuta.io
adolfhackler@tutanota.com
AskHeIp@tutanota.com
chily@tuta.io
antichrist666@tutamail.com
neuro.net@tuta.io
vassago_0203@tutanota.com
zery@tuta.io
raziotix@tuta.io
darkencryptor@tutanota.com
Patagonoa92@tutanota.com
Trojan.AiDcrypt@tutanota.com
cricket@tutanota.com
fixallfiles@tuta.io
Citrteam@tutanota.com
coinsman@tutanota.com
y0000@tuta.io
Decfile431@tutanota.com
kurosaki_ichigo@tutanota.co
randomlocker@tuta.io
mirey@tutanota.com
ochennado@tutanota.com
decspeed@tutanota.com
jborn@tuta.io
keyforyou@tuta.io
host2021@tutanota.com
marjut65@tutanota.com
FileEngineering@tutanota.com
mr.hacker@tutanota.com
psychopath7@tutanota.com
gizmo12@tutanota.com
codiv2021@tutanota.com
HappyNewYear2021@tutanota.com
yourfiles1@tutanota.com
dou876sh@tuta.io
ndecodedecode@tutanota.com
nmanagersmaers@tutanota.com
grdoks@tutanota.com
Szems@tutanota.com
EpsilonCrypt@tutanota.com
zfile@tuta.io
bad_dev@tuta.io
iamcanhelpyou@tuta.io
WSS911@tutanota.com
RestorFile@tutanota.com
Desparo@tuta.io
dr.nemo@tutanota.com
skgrhk2018@tutanota.com
decodeme666@tutanota.com
Secure2017@tuta.io
nMayth24@tutanota.com
help@tutanota.com
cyberunion@tuta.io.cu
safronov123@tuta.io
Encrypt4u@tutanota.com
Helps@tutanota.com
hebem@tuta.io
kamira99@tutanota.com
nmiddleman2020@tutanota.com
filesrestore@tutanota.com
nAlanRed@tutanota.com
prosoft@tutanota.com
crypthub@tuta.io
siliconegun@tutanota.com
dfvdv@tutanota.com
Mayth24@tutanota.com
artemy75@tutanota.com
santino3046@tutanota.de
nordfox@tutanota.com
mikrotik@tutamail.com
zetterlow@tutanota.com
khalate@tutanota.com
gamigin0612@tutanota.com
nobad@tutamail.com
filemgr@tutanota.com
sebekgrime@tutanota.com
DeathSpicy@tutanota.com
Sherminator.help@tutanota.com
filekerk@tutanota.com
Swordf1sh@tutanota.com
xilttbg@tutanota.com
price.decoding@tutanota.com
hhaaxxhhaaxx@tuta.io
AlanRed@tutanota.com
MasterLuBu@tutanota.com
clifieb@tutanota.com
triplock@tutanota.com
rep_stosd@tuta.io
n2.Hariliuios@tutanota.com
Sc0rpio0@tutanota.com
combo@tutanota.de
adren.kutospov.97@tutanota.com
help73@tutanota.com
smartrecav@tutanota.com
heineken@tuta.io
SafeGman@tutanota.com
Sambolero@tutanoa.com
05250lock@tutamail.com
gizm0@tutanota.com
StuardRitchi@tutanota.com
nAdamBrown89@tutanota.com
123@tutanota.com
jessymail26@tuta.io
neural.net@tuta.io
ny0000@tuta.io
nCitrteam@tutanota.com
satco@tutanota.com
Blackmax@tutanota.com
jerjis@tuta.io
Toni.morrison13@tutanota.com.com
badbusiness@tutanota.de
dc.dcrypt@tutanota.com
datareesstore@tutanota.com
allback@tutanota.com
Panama777@tutanota.com
zxqwopnm@tutanota.com
kurosaki_ichigo@tutanota.com
middleman2020@tutanota.com
cryptlocker@tutanota.com
hinduism0720@tutanota.com
Soportevoid@tutanota.com
naes-ni@tuta.io
Helpcrypt1@tutanota.com
9ea6e85bd12b@tutanota.com
aihlp24@tuta.io
4reserve@tuta.io
rapid.file@tuta.io
2.Hariliuios@tutanota.com
ghjujy@tuta.io
moloch_helpdesk@tutanota.com
Decryptoffice@tuta.io
JamesBaker78@tutanota.com
unblocked@tuta.io
BCPFILE17@tutanota.com
null_ptr@tutanota.de
flower.harris@tutanota.com
Starbax@tutanota.com
nkhalate@tutanota.com
new_wave@tuta.io
bitcoins12@tutanota.com
nginxhole@tutanota.com
fast_decrypt_and_protect@tutanota.com
szem@tutanota.com
w3qupe@tuta.io
managersmaers@tutanota.com
Zeman@tutanota.de
TomLee24@tuta.io
kuk1@tuta.io
ICanFixYourFiles@tutanota.com
de_cryption@tuta.io
wilhelmkox@tutanota.com
lafoievologjanin123@tutanota.com
fonix@tuta.io
backuppc@tuta.io
nAskHeIp@tutanota.com
technopc@tutanota.com
nmode@tutanota.com
AdamBrown89@tutanota.com
juniorwanme@tutanota.com
xser@tutanota.com
dorispackman@tuta.io
warthunder089@tutanota.de
nfilekerk@tutanota.com
Helpsdec@tutanota.com
xzet@tutanota.com
pol.aris@tutanota.com
Stay tuned!
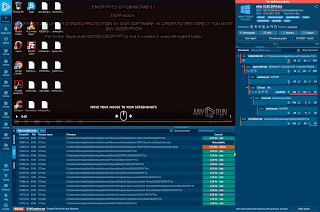



.jpg)


































