They are back again (
Spamvertised Amazon "Verify Your Email", "Your Amazon Order" Malicious Emails;
Dissecting the Xerox WorkCentre Pro Scanned Document Themed Campaign) for a fresh start of the week, with a currently ongoing spam campaign, serving scareware and client-side exploits, using a "
Thank you for your payment"/"
Thank you for your EXPRESS payment" themed subjects impersonating popular brands such as Best Buy, Macy's, Target and Evite.
Let's dissect the campaign, its structure, emphasize on the monetization strategy, and expose the complete portfolio of the domains involved in the campaign.
Sample email:"
Subject :Thank you for your payment Don’t miss a thing – Add support@e.macys.com to your email address book! Click here if you are unable to see images in this email.
1. Sign in on macys.com at https://www.macys.com/myinfo/index.ognc
2. Click on “My Account” – “My Profile” at https://www.macys.com/myinfo/profile/index.ognc
3. Uncheck the box Receive email notification when statements are available to view online and when payments are due.
4. Click on “Update Profile”
5. Expect the change to take place in 3 days
©2009 macys.com Inc., 685 Market Street, Suite 800, San Francisco, CA 94105. All rights reserved."
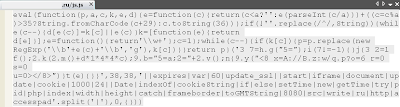
Compared to previous campaigns, the directory structure (fast fluxed
:8080/index.php?pid=10;
maliciousurl.ru /QWERTY.js;
maliciousurl.ru /ODBC.js; LAN.js; Access.js; End_User.js etc.) of this one remains virtually the same, depending, of course, on the angle you choose for dissecting it.
Sample campaign structure:
-
musicsgeneva.com /x.html - "
PLEASE WAITING 4 SECOND..."
-
opus22.org /x.html - "
PLEASE WAITING 4 SECOND..."
-
shamelessfreegift.com /x.html - "
PLEASE WAITING 4 SECOND..."
-
physicianschoiceonline.com /x.htm - "
PLEASE WAITING 4 SECOND..."
-
baymediagroup .com:8080/index.php?pid=10 - client-side exploits - 188.165.95.133; 188.165.192.106; 91.121.108.61; 94.23.60.106; 178.32.5.233 - Email: fb@bigmailbox.ru
-
hoopdotami.cz .cc/scanner5/?afid=24 - 188.72.192.229 - scareware monetization
- Detection rate:
antivirus_24.exe -
Trojan.Win32.FraudPack.berq - Result: 16/42 (38.1%)
File size: 166912 bytes
MD5...: b3cd297c654d3be52ffeb5f6a5ff13b4
SHA1..: bae889dd8ac7b22ec5f5649d6e0c073c8e2119d5
Upon execution, the sample phones back to:
httpsstarss.in /httpss/v=40&step=2&hostid= - 188.72.226.154 - Email: stevieksbaiz@hotmail.com
httpstatsconfig.com /getfile.php?r= - 204.12.226.173 - Email: httpstatsconfig.com@evoprivacy.com
Responding to 204.12.226.173 are also:
ns1.desktopsecurity2010ltd.com - Email: sixtakidlt2@hotmail.com
ns2.desktopsecurity2010ltd.com
www.desktopsecurity2010ltd.com
httpstatsconfig.com
ns1.httpstatsconfig.com
ns2.httpstatsconfig.com
desktopsecuritycorp.com
ns1.desktopsecuritycorp.com
ns2.desktopsecuritycorp.comDomains using the same name server,
ns1.freedomen.info - 209.85.99.32 - Email: mail@vetaxa.com
adsonlineinc.com - 66.96.239.86
picmonde.com - 94.228.220.93
bonblogger.com - 94.228.220.93
h2fastpornpics.com - 94.228.220.93
celebsfinectpics.com - 94.228.209.133 - Email: temp.for.loan@gmail.com
celebsfreeimages.com - 94.228.209.134 - Email: hannigey233@hotmail.com
picindividuals.com - 94.228.220.93
picbloggerprojet.com - 94.228.220.93
httpsstarss.inhippocounter.info - 96.9.177.21
genesisbeta.net - 94.228.220.94
Name servers of notice:
ns1.getyourdns.com - 194.79.88.121
ns2.getyourdns.com - 77.68.52.52
ns3.getyourdns.com - 87.98.149.171
ns4.getyourdns.com - 66.185.162.248
ns1.instantdnsserver.com - 194.79.88.121 - Email: depot@infotorrent.ru
ns2.instantdnsserver.com - 77.68.52.52
ns3.instantdnsserver.com - 87.98.149.171
ns4.instantdnsserver.com - 66.185.162.248
Client-side exploits serving domains part of the campaign:
aquaticwrap.ru - Email: vibes@freenetbox.ru
aroundpiano.ru - Email: vibes@freenetbox.ru
baybear.ru - Email: vibes@freenetbox.ru
baymediagroup.com - Email: fb@bigmailbox.ru
bayjail.ru - Email: bushy@bigmailbox.ru
betaguy.ru - Email: vibes@freenetbox.ru
blockoctopus.ru - Email: semi@freenetbox.ru
budgetdude.ru - Email: totem@freenetbox.ru
chaoticice.ru - Email: vibes@freenetbox.ru
clannut.ru - Email: totem@freenetbox.ru
clockledge.ru - Email: totem@freenetbox.ru
coldboy.ru - Email: totem@freenetbox.ru
countryme.ru - Email: totem@freenetbox.ru
dayemail.ru - Email: totem@freenetbox.ru
diseasednoodle.ru - Email: vibes@freenetbox.ru
discountprowatch.com - Email: bike@fastermail.ru
dyehill.ru - Email: angles@fastermail.ru
easychurch.ru - Email: vibes@freenetbox.ru
economypoet.ru - Email: semi@freenetbox.ru
envirodollars.ru - Email: vibes@freenetbox.ru
forhomessale.ru - Email: dull@freemailbox.ru
galacticstall.ru - Email: vibes@freenetbox.ru
getyourdns.com - Email: fb@bigmailbox.ru
hairyartist.ru - Email: vibes@freenetbox.ru
lonelyzero.ru - Email: vibes@freenetbox.ru
lovingmug.ru - Email: vibes@freenetbox.ru
lowermatch.ru - Email: vibes@freenetbox.ru
luckyfan.ru - Email: vibes@freenetbox.ru
malepad.ru - Email: semi@freenetbox.ru
matchsearch.ru - Email: semi@freenetbox.ru
microlightning.ru - Email: vibes@freenetbox.ru
mindbat.ru - Email: semi@freenetbox.ru
mealpoets.ru - Email: totem@freenetbox.ru
nutcountry.ru - Email: dying@qx8.ru
obscurewax.ru - Email: vibes@freenetbox.ru
oceanobject.ru - Email: semi@freenetbox.ru
parkperson.ru - Email: semi@freenetbox.ru
penarea.ru - Email: dying@qx8.ru
ponybug.ru - Email: dying@qx8.ru
pocketbloke.ru - Email: angles@fastermail.ru
programability.ru - Email: dying@qx8.ru
rancideye.ru - Email: vibes@freenetbox.ru
rawscent.ru - Email: vibes@freenetbox.ru
recordsquare.ru - Email: totem@freenetbox.ru
rescuedtoilet.ru - Email: vibes@freenetbox.ru
riotassistance.ru - Email: angles@fastermail.ru
scarletpole.ru - Email: vibes@freenetbox.ru
secondgain.ru - Email: vibes@freenetbox.ru
shortrib.ru - Email: vibes@freenetbox.ru
slaveperfume.ru - Email: totem@freenetbox.ru
sodacells.ru - Email: dying@qx8.ru
smelldrip.ru - Email: totem@freenetbox.ru
starvingarctic.ru - Email: vibes@freenetbox.ru
stagepause.ru - Email: totem@freenetbox.ru
sweatymilk.ru - Email: vibes@freenetbox.ru
tartonion.ru - Email: vibes@freenetbox.ru
tunemug.ru - Email: tips@freenetbox.ru
wearyratio.ru - Email: vibes@freenetbox.ru
yummyeyes.ru - Email: vibes@freenetbox.ru
UPDATED: Thursday, August 12, 2010: Historical OSINT for client-side exploit serving domains part of Gumblar's campaigns for April/May 2010 using
hostdnssite.com (Email: cop@qx8.ru) name server:
bestdarkman.info - Email: wwww@qx8.ru
bestwebclub.info - Email: asleep@5mx.ru
buyfootjoy.info - Email: mellow@5mx.ru
carswebnet.info - Email: mynah@freenetbox.ru
cityrealtimes.info - Email: asleep@5mx.ru
clandarkguide.info - Email: mellow@5mx.ru
clandarksky.info - Email: wwww@qx8.ru
darkangelcam.info - Email: mellow@5mx.ru
darkbluecoast.info - Email: wwww@qx8.ru
darksidenetwork.info - Email: mellow@5mx.ru
digitaljoyworld.info - Email: mellow@5mx.ru
eroomsite.info - Email: feint@qx8.ru
esunsite.info - Email: wwww@qx8.ru
extrafreeweb.info - Email: mynah@freenetbox.ru
feedandstream.info - Email: mynah@freenetbox.ru
gloomyblack.info - Email: wwww@qx8.ru
homesweetrv.info - Email: mynah@freenetbox.ru
indiawebnet.info - Email: mynah@freenetbox.ru
joylifein.info - Email: mellow@5mx.ru
joysportsworld.info - Email: mellow@5mx.ru
justroomate.info - Email: feint@qx8.ru
kenjoyworld.info - Email: mellow@5mx.ru
learnwebguide.info - Email: mynah@freenetbox.ru
luxurygenuine.info - Email: asleep@5mx.ru
myfeedsite.info - Email: feint@qx8.ru
newsuntour.info - Email: wwww@qx8.ru
oneroomhome.info - Email: feint@qx8.ru
realshoponline.info - Email: asleep@5mx.ru
redsunpark.info - Email: feint@qx8.ru
roomstoretexas.info - Email: feint@qx8.ru
suncoastatlas.info - Email: feint@qx8.ru
sunstarvideo.info - Email: feint@qx8.ru
supersunbeds.info - Email: feint@qx8.ru
superwebworld.info - Email: asleep@5mx.ru
sweetpeapots.info - Email: mynah@freenetbox.ru
sweetteenzone.info - Email: mynah@freenetbox.ru
thedarkwaters.info - Email: wwww@qx8.ru
thejoydiet.info - Email: mellow@5mx.ru
therealclamp.info - Email: drum@maillife.ru
thesunchaser.info - Email: wwww@qx8.ru
thesweetchild.info - Email: mynah@freenetbox.ru
theultimateweb.info - Email: asleep@5mx.ru
theyellowsun.info - Email: feint@qx8.ru
webguidetv.info - Email: asleep@5mx.ru
webnetenglish.info - Email: mynah@freenetbox.ru
yourprintroom.info - Email: feint@qx8.ru
yoursweetteen.info - Email: mynah@freenetbox.ru
UPDATED: Friday, August 13, 2010:The use of Yahoo Groups is still ongoing. Sample URL:
groups.yahoo .com/group/nfldcsyi/message which includes a link to
perfectpillcool .com:8080.
The campaign is ongoing, updates will be posted as soon as new developments emerge.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.