_Uniform Traffic Tickets
Spamvertised attachments - Ticket-728-2011.zip; Ticket-064-211.zip; Ticket-728-2011.zip
Detection rates:
Ticket.exe - Gen:Trojan.Heur.FU.bqW@aK9ebrii - Detection rate: 37/43 (86.0%)
MD5 : 6361d4a40485345c18473f3c6b4b6609
SHA1 : 50b09bb2e0044aa139a84c2e445a56f01d70c185
SHA256: ca67a14bfed2a7bc2ac8be9c01cb17d5da12b75320b4bad4fe8d8a6759ad9725
Ticket1.exe - Trojan-Downloader.Win32.Small.ccxz - Detection rate: 36/44 (81.8%)
MD5 : e2a2d67b8a52ae655f92779bec296676
SHA1 : ed3df72b4e073ffba7174ebc8cb77b2b7d012cbf
SHA256: 50b104c5f8314327e03b01e7f7c2535d8de7cd9f73f8e16d1364c7fd021a90cc
Upon execution the samples phone back to:
sdkjgndfjnf.ru/pusk3.exe - 91.220.0.55 (responding to the same IP is also survey-providers.info) - AS51630 - Email: admin@sdkjgndfjnf.ru
rattsillis.com/ftp/g.php - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
rattsillis.com/pusk3.exe - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
DNS emulation of ns1.lemanbrostm.info reveals two domains belidiskalom.com - 178.208.76.175 - Email: admin@belidiskalom.com and lemanbrostm.info - Email: coz@yahoo.com using the same name server.
Known MD5 modifications for pusk3.exe at rattsillis.com:
c6dab856705b5dfd09b2adbe10701b05
f167213c6a79f2313995e80a8ac29939
f4764cce5c3795b1d63a299a5329d2e2
dae9e7653573478a6b41a62f7cb99c12
69c983c9dfaf37e346004c9aaf54a3d0
d875b8e32a231405c7fa96b810e9b361
628270c6e44b0fa21ef8e87c6bc36f57
9b69dabd876e967bcd2eb85465175e3b
0434c084dba8626df980c7974d5728e1
Related binaries and associated MD5 modifications:
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
rattsillis.com/pusk.exe - MD5: 55d8e25bc373a98c5c29284c989953ab; 368c86556e827d898f043a4d5f378fa0; 7411d0d29db91f2625ee36d438eb6ac4; 3ea4e9fd297b3058ebbb360c1581aaac;
rattsillis.com/pusk2.exe - MD5: dae9e7653573478a6b41a62f7cb99c12; b73705c097c9be9779730d801ad098e0; d7952c1e77d7bb250cdfa88e157fb5a8
Known MD5 modifications for pusk3.exe at sdkjgndfjnf.ru: 8672f021e7705b6a8132b7dfc21617cf
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8; ebf7278a7239378e7d70d426779962ce
sdkjgndfjnf.ru/pusk2.exe - MD5: d9e36e25a3181f574fd5d520cb501d3a
sdkjgndfjnf.ru/pusk.exe - MD5: fce04f7681283207d585561ed91e77b4
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8
Detection rate for blood.exe:
blood.exe - Trojan-Spy.Win32.Zbot - 25/44 (56.8%)
MD5 : 577cf0b7ca3d5bcbe35764024f241fa8
SHA1 : 30f542a44d06d9125cdfbdd38d79de778e4c0791
SHA256: 1741ef5d24641ee99b5d78a68109162bebc714c3d19abc37e3d4472f3dcd6f18
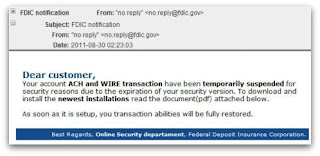
_FDIC Notification
Spamvertised attachments: FDIC_Document.zip
Detection rate:FDIC_Document.exe - Gen:Trojan.Heur.FU.bqW@a45Fklbi - 35/44 (79.5%)
| MD5 : 7b5a271c58c6bb18d79cd48353127ff6 |
| SHA1 : 6526b6097df42f93bee25d7ea73f95d2fcc24d3a |
| SHA256: a09165c71a8dd2a1338b2bd0c92ae07495041ae15592e3432bd50600e6ef2af0 |
Upon execution phones back to:
rattsillis.com/ftp/g.php
rattsillis.com/blood.exe
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
What's particularly interesting is the fact that both campaigns have been launched by the same cybercriminal, with the same C&C - rattsillis.com also seen in the spamvertised ACH Payment Canceled campaign.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.