I've just stumbled across a pretty decent and massive phishing domains farm that using Google's for the purpose of hosting and distributing the rogue and malicious content.
In this post I'll provide actionable intelligence on the infrastructure behind it including to discuss in-depth the TTPs (Tactics Techniques and Procedures) of the cybercriminals behind it.
Sample rogue and malicious URL known to have participated in the campaign:
hxxp://js-82wha8sw738.web.app/sc/css.css
Sample malicious and rogue responding IPs known to have participated in the campaign:
199.36.158.100
151.101.1.195
151.101.65.195
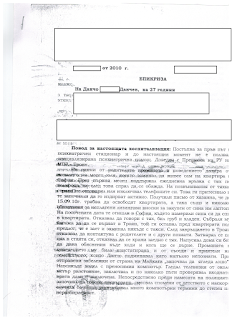
Sample screenshots of the rogue and malicious phishing domains known to have been involved in the campaign:
Sample rogue and malicious phishing domain portfolio known to have participated in the campaign:
0000.firebaseapp.com
02a8.web.app
11spielmacherbeta.firebaseapp.com
131023.firebaseapp.com
144110.firebaseapp.com
1493735036650.firebaseapp.com
164200.firebaseapp.com
177010.firebaseapp.com
177610.firebaseapp.com
17cc7.firebaseapp.com
212820.firebaseapp.com
abmay-d9b3b.web.app
abmay2-4abdf.web.app
adamlouie-c87d1.firebaseapp.com
adda-fenase.web.app
admininstatiles-5e702.firebaseapp.com
ads-restricted-id.web.app
aglae-f0665.firebaseapp.com
ahwma-de0bf.web.app
airbnb-70aba.firebaseapp.com
ajarwebsite-7d033.firebaseapp.com
all-scanner-cdf80.web.app
amao-dc021.web.app
ambitowebapp-2e394.firebaseapp.com
analytics-6a184.firebaseapp.com
angular2-hn.firebaseapp.com
angular7firestore-155e4.firebaseapp.com
aniapp-7ddc2.firebaseapp.com
anna-prone.web.app
api-project-723816548444.firebaseapp.com
appeal-form-fb-copyright102872.web.app
appeal-form-fb-copyright18258.web.app
appeal-form-fb-copyright187265.web.app
appeal-page-unpublish-1827589.web.app
appeal-page-unpublish1107276.web.app
appeal-page-unpublish118172861.web.app
appeal-page-unpublish18275.web.app
appeal-page-unpublish182758.web.app
appeal-page-unpublish1827586.web.app
appeal-page-unpublish182759.web.app
appeal-page-unpublish18278652.web.app
appeal-page-unpublish1827890.web.app
appeal-page-unpublish187-36ac4.web.app
appeal-page-unpublish18769.web.app
appemailhostingcha2.web.app
appy-760b5.firebaseapp.com
ararestaurant1.firebaseapp.com
arco-website-f9750.firebaseapp.com
aruba-postmaster-info.web.app
asmorx-1f6a2.web.app
asna-mod.web.app
ass-mote.web.app
asse-mofe.web.app
assets-0l61.firebaseapp.com
atarashii-atsui.web.app
au-ma-di.web.app
aude-mofe.web.app
audiscover-owawebapplications.web.app
auri-mo-da.web.app
auth-task1-m.web.app
auth20-outlook.web.app
authdemo-177a0.firebaseapp.com
authenticationuchu23.web.app
baffe-level.web.app
bandspace-console.web.app
baren-od.web.app
battle-22f22.firebaseapp.com
benali-acbe6.web.app
bestofjs-api-v1.firebaseapp.com
bi-1020101000x0.web.app
bigbt-aten.web.app
bingbrossvocalintel.web.app
bitbaink.web.app
bithunnb.web.app
bjqrasuoup.web.app
blockchain-assets-protection.web.app
blockchain-recovery-dda4d.web.app
bmazy2-0.web.app
bnp-verifi.web.app
boma-ren.firebaseapp.com
booking-hotesses-d7920.firebaseapp.com
bred-authentification-97-7.web.app
buten-dare.web.app
bzbikeruko.web.app
ca-regionale-department-a.web.app
cabs-ole.web.app
cadeau-par-plaisir.web.app
cale-mothe.web.app
camoam-d97a4.web.app
case-ofa.web.app
case100091254778.web.app
caseforpage100089481844.web.app
caseforpages100049151.web.app
caseforpages108412.web.app
caseforpages1885777.web.app
caseforpages1888888.web.app
caseforpages55222.web.app
caseforpages777422.web.app
caseforpages88174714.web.app
caten-opa.web.app
cau-quate.web.app
cen-kenase.web.app
cenle-one.web.app
centre-telephoneproinfo.web.app
chargement-service.web.app
chat-b2982.firebaseapp.com
chat-finpolo.firebaseapp.com
checkmailsawo5.web.app
checkmessagerievocalewebtel.web.app
checksweetmail6.web.app
cinhatena.web.app
cloud-space-auth-service.web.app
clouddoc-authorize.firebaseapp.com
club-note-vocale.web.app
code-mesme.web.app
cogne-menta.web.app
cojet-mole.web.app
cokade-made.firebaseapp.com
colimat-done.web.app
colo-mate.web.app
comasse-unade.web.app
come-measa.web.app
companyemailresync1.web.app
con-firma.firebaseapp.com
cones-dore.web.app
conh-ma.web.app
cop-ado.web.app
cope-ilna.web.app
cora-gas-me.web.app
cphost-7edd4.web.app
crawer-sur.web.app
credit-et-assurance07.web.app
cres-mate.web.app
crime-aune.web.app
crive-cible.web.app
csen-ted.web.app
d-validate.web.app
d3iioor0753gvdbfewypqb64.web.app
daisma-e7e6c.web.app
darrin-pendleton-j5286.web.app
dc4u-6e803.firebaseapp.com
decdo-chat2.firebaseapp.com
demachatendi36.web.app
demoitau-d3428.web.app
denabere-2c382.web.app
digital-book-9f870.firebaseapp.com
dmacenda.web.app
docsharex-authorize.firebaseapp.com
docuproject39-277-383-files.firebaseapp.com
dope-ufen.web.app
downloadfreeebookspdf-6e806.firebaseapp.com
downloadpdfreader-d7702.firebaseapp.com
drafty-43c88.firebaseapp.com
driveintuksouteast-falcaopla.web.app
dropdocument-c3829.web.app
dskdirect-5ba26.web.app
dw-website-fbc19.firebaseapp.com
eagle10.firebaseapp.com
ebookwngfgewarwle.web.app
edret-tropm.web.app
efetgreds.web.app
eins-done.web.app
eleven-bot-399b7.web.app
elimu-c1a38.firebaseapp.com
email-mweb-co-za-zimbra-1.firebaseapp.com
email-update-verify.web.app
email-verificationservices365.web.app
empacte-do.web.app
ems-obe.web.app
emsi-lobo.firebaseapp.com
end-losup.web.app
erfders-f6013.web.app
esote-mode.web.app
exness-mobile.web.app
explore-wetriansfering-web.web.app
exposedacne.web.app
f0ldgonn.firebaseapp.com
facebook-appeal1749902610052.web.app
facebook-appelcase32q1.web.app
facebookappeal-case10351001.web.app
facebookappealcase1884888444.web.app
facebookappealcase7174747444.web.app
facebookcase187444441.web.app
facebookcase188444.web.app
fares-one.web.app
fb-appeal-form-70f46.web.app
fb-appeal-form-791bd.web.app
fb-restricted-d12c2.web.app
fbappealform13111.web.app
fbforpages1848151.web.app
fbmail-case199418414.web.app
fbmail-pages100049194.web.app
fbpages-case10004915.web.app
fema-tode.web.app
fetfetaa-81119.web.app
fines-gining.web.app
firtserverunithpp.web.app
flape-man.web.app
flape-odade.web.app
fmvfhagpab.web.app
focus-online-news.web.app
fodes-mota.web.app
font-makeupe.web.app
foresta-mod.firebaseapp.com
foten-moda.web.app
francesbbv.web.app
freeebookspdf-9ab41.firebaseapp.com
freejobsnews-f8cb8.firebaseapp.com
freis-mode.web.app
gadjabadjala1.web.app
gare-train3.web.app
gene-marso.web.app
genie-alba.firebaseapp.com
girly-wallpaper-5b75f.web.app
godadyxs.web.app
gomas-12c01.web.app
gospel-living.web.app
goswapp-bsc.web.app
gotan-one.web.app
gotcha-67060.firebaseapp.com
grace-bijoux-14910.firebaseapp.com
green656dfbb5f31b1fe48c2391a6.web.app
gridsend-98f14.web.app
groupe-ca-authenticati-caisse.web.app
groupe-sa-accueil-autnenti.web.app
gweb-gc-gather-production.firebaseapp.com
gweb-miyagi.firebaseapp.com
hagenpau.web.app
histoire-clik.web.app
hiworksservicecenter.web.app
hon-macona.web.app
hounbvc-c7661.web.app
hsfkrkqogo.web.app
httpsaudiscover-owawebapplications.web.app
httpsdocument-download-902123.web.app
httpsfyregym-wetransfer.web.app
httpsjojo-wiza124.web.app
httpsjoovkuebea.web.app
httpsminxtex.firebaseapp.com
httpsprice-per-unit.firebaseapp.com
httpsprotectmimemimefrem.web.app
httpsworldvision-419f2.firebaseapp.com
hunin-one.web.app
hyle-fb82f.web.app
info-telephone-vocale.web.app
international-web-fb75a.web.app
isfane-osade.web.app
iydd-1b2d8.web.app
jams-jamz1234.web.app
jecta-f45df.firebaseapp.com
jentame-add.web.app
jes-mo-sad.web.app
jex-ulto.web.app
kaunte-mone.web.app
kebote-moda.web.app
kes-mole.web.app
kodrefse-nsf.web.app
l09162020-fixmailhelpdesk.web.app
laefhfdhkdsdv.web.app
lamaf-50e45.web.app
les-more.web.app
lg-roudcubeblack-access.web.app
lgeyfuusmg.web.app
licloud.web.app
licos-date.web.app
line-9ca1c.web.app
link-bb76d.web.app
lisen-ocun.web.app
live-support-82d11.firebaseapp.com
login-442v3f.web.app
loginfo-tkconf.web.app
lohsam-86765.web.app
lommsrecu3.firebaseapp.com
lono-jena.web.app
lote-masme.web.app
louams-62870.web.app
lthouse.web.app
m-cabanqueenligne-particuliers.web.app
m-orangebankenligne-id.web.app
m1technology.firebaseapp.com
maedz-5fdff.web.app
mail-8583e.web.app
mail-account-verify-f4723.web.app
mail-lcloud-com-account.web.app
mail-ovhcloud.web.app
mansan-4ca1c.web.app
may1110genstanbk.web.app
mbqbfhfmgr.web.app
memo-vocale-52636.web.app
mentipdf.web.app
mercadolibre-research.web.app
mms-sms-alert.firebaseapp.com
mo-aska-da.web.app
mobialmysyf.web.app
mobizzmperb.web.app
moce-add.web.app
moce-aude.web.app
molases-b652e.web.app
mon-tome.web.app
msgmessage-7f854.firebaseapp.com
mswordg.web.app
mta-round-cube.web.app
mxflexsub.web.app
my-bithumb.web.app
my-winbamk.web.app
mylogin-config.web.app
nale-ping.web.app
name-ocina.web.app
ne01u59l.firebaseapp.com
nera-mode.web.app
netw0rksolutions.web.app
newlink-c8a8f.web.app
njnapcdvzc.web.app
nopin-dod.web.app
nozed-uname.firebaseapp.com
ntzmttpmnttoepnlant.web.app
o-orangebank18-id.web.app
oaism-72827.web.app
ocaque-domen.firebaseapp.com
ocuso-aken.web.app
office-webmail-login-f0e3c.web.app
officeindex-file.web.app
officemailsharing-20cd3.web.app
offices-voicemail.web.app
oftenas-oweb.web.app
ojin-madij.web.app
olet-mado.web.app
omawo-14b8c.web.app
on-me-ro.firebaseapp.com
onee-a0488.web.app
oneone-19cd8.web.app
onga-moce.web.app
onlinepdfkwpmmkl.web.app
onsa-mode.web.app
orange-my-app.web.app
orangesmsprovocale.web.app
oras-moria.web.app
oroma-42f59.web.app
osale-mape.web.app
osaute-moca.web.app
others1-f7ce9.web.app
outline-auth-d7f99.web.app
outlookloffice365user09ngxsmd.web.app
outlookloffice365userp86aese6.web.app
outlooks-userserver.web.app
owa-signon-officeaccount.web.app
owablu84349439434.web.app
owserv220020.web.app
padma-3fbb8.web.app
page-appeal-unpublish1253631.web.app
pagebusiness-copyrightcase1256.web.app
pay-sera.web.app
phuongpndev.web.app
pokajca.web.app
poltunefrdonecodesms.web.app
popuyecash7.web.app
portail-messagerieorangesms.web.app
postmailservr-panel-centr.web.app
project2021c-42b13.firebaseapp.com
pry-ecommerce.web.app
put-media-lan.web.app
r-web-2a3a9.web.app
rbc-mainline.web.app
rbc-verifylogin5.web.app
rbclogin-line.web.app
readingwtagzdm.web.app
recording-c12f5.web.app
renard-trouillard.web.app
restore70174-coinbase-us.web.app
rjabldfrbg.web.app
romas-512bf.web.app
rooted-4da8a.web.app
rouncubemail.web.app
royalbill-a3y4.web.app
rufe-sun.web.app
saal-kejriwal.web.app
samda-3c88f.web.app
sarba-one.web.app
scorchvc.web.app
scorchvc.web.app0
serve-8e8dc.web.app
server-authentication-332e1.web.app
servercpanel-afa12.web.app
service-vocalesmsprotelfixe.web.app
sharebox-onedrive-file-f692f.web.app
side-esone.web.app
sim-ote.web.app
skype-online04171.web.app
slackchatv1.firebaseapp.com
snaptik.web.app
soci-molen.web.app
sode-mape.web.app
soden-olma.web.app
sofe-inchena.web.app
sofe-tane.web.app
solen-conda.web.app
somas-b88a0.web.app
sone-masa.web.app
sonta-maline.web.app
sore-modabe.web.app
soure-made.web.app
sparkassbank-de.web.app
srey-deocs.web.app
sroxma-ab2cc.web.app
sudo-mone.web.app
sugen-oda.web.app
sun-maupe.web.app
sunge-ode.firebaseapp.com
suone-bena.web.app
swiftshare-content-auth.web.app
tittot-a8505.web.app
tm-etiquetado.web.app
tome-done.web.app
totem1.web.app
totem2.web.app
tousou-posoto3.web.app
trdsmccdb7386cbf3ba0b0b8d.web.app
truein-264db.web.app
ugen-orabe.web.app
uiinlcuo37oed.web.app
un-foreste.web.app
unt-morelle.web.app
update-45190ca.web.app
user-45190ca21.web.app
userca-58ce4.web.app
usmin-moda.web.app
validate-clientrbc.web.app
vandameman4.web.app
verberuyer7.web.app
verif-loginrbc.web.app
verify-48181.web.app
verify-user-rbc.web.app
verifywell-85477.web.app
vkmqnvyfwd1111.web.app
vmta-mod.web.app
vocaleproidorange.web.app
votre-boitevocale-fixe.firebaseapp.com
wdfyxklmba.web.app
web-bf4.web.app
web-e1f6d.web.app
web874830-98375-90232.web.app
webmail-a2846.web.app
webmail-control-9efc7.web.app
wecluihfrf-76tygh.web.app
wedpfoaliculate-resmazm.web.app
westernfoodmaincourse.web.app
wetranslatetransfers-coxsola.firebaseapp.com
wetrnafers.web.app
whatsapp-clone-teamwork.firebaseapp.com
win-more-0x.web.app
winx-fbac0.web.app
wix-engage-visitors-prod-0.firebaseapp.com
wix-engage-visitors-prod-10.firebaseapp.com
wix-engage-visitors-prod-20.firebaseapp.com
wo0923536-902453-908563.web.app
wraxdne.web.app
www.firebaseapp.com
www.web.app
x0x0x10010-0100.web.app
x48652.web.app
xamua-7cb66.web.app
xcio-00000auth.web.app
xm01-18c1f.web.app
xn--87487387348739-16aa.web.app
xtpma4ep.firebaseapp.com
zoho-active.web.app
zoho-adminserv.web.app
zoho-mailservices.web.app
zoho-online.web.app
zoho-validationserv.web.app
zxtst-44902.firebaseapp.com
Stay tuned!