In the overwhelming sea of information, access to timely, insightful and independent open-source intelligence (OSINT) analyses is crucial for maintaining the necessary situational awareness to stay on the top of emerging security threats. This blog covers trends and fads, tactics and strategies, intersecting with third-party research, speculations and real-time CYBERINT assessments, all packed with sarcastic attitude
Monday, May 09, 2011
Don't Play Poker on an Infected Table - Part Five
A currently spamvertised campaign is enticing end users into downloading a fraudulent online gambling application KingSpinEN.exe. The campaign is part of last month's Don't Play Poker on an Infected Table - Part Four series.
Detection rate:
KingSpinEN.exe - W32/Casino.F.gen!Eldorado - Result:16/43 (37.2%)
MD5 : ead8156a838842bc8463995a91eee08b
SHA1 : 239594a514c461c63dc8da69b08b9b63baaf2579
SHA256: 491c291eaed67268d14a36470e5d6f6d4ed829055fe4a2897ac5f050b50a2e36
Upon execution phones back to:
- download.thepalacegroupgaming.com /tracking.aspx?ul=en&casino=spinpalace&banner_tag=a20337&uuid=%7b9F9E0585-9340-45C0-9EC7-46FBE5E7127F%7d&state=100
- spinpalace.mgsmup.com /mupp/spinpalace/spinpalace_install.cab
- spinpalace.mgsmup.com /mupp/spinpalace/spinpalace.cab
- download.thepalacegroupgaming.com /tracking.aspx?ul=en&casino=spinpalace&banner_tag=a20337&uuid=%7b9F9E0585-9340-45C0-9EC7-46FBE5E7127F%7d&state=422
- marketing.valueactive.eu /VIP/animations/en/movies_en.htm
Portfolio of fraudulent online gambling domains part of the campaign. The majority are hosted within AS49130, ARNET-AS SC ArNet Connection SRL:
casino-elit-super.ru - 89.45.14.12
casinogoldsuper.ru - 89.45.14.12
casinokingsuper.ru - 89.45.14.12
casino-king-super.ru - 89.45.14.12
casinolabsuper.ru - 89.45.14.12
casino-lux-super.ru - 89.45.14.12
casinomultisuper.ru - 89.45.14.12
casinonetsuper.ru - 89.45.14.12
casino-net-super.ru - 89.45.14.12
casinonextvip.ru - 89.45.14.12
casino-online-super.ru - 90.182.175.234
casinopartysuper.ru - 90.182.175.234
casino-party-super.ru - 90.182.175.234
casinoplazasuper.ru - 90.182.175.234
1casinostarsuper.ru - 90.182.175.234
casinosuperelit.ru - 89.45.14.12
casino-super-elit.ru - 89.45.14.12
casinosuperking.ru - 89.45.14.12
casino-super-king.ru - 89.45.14.12
casinosupermulti.ru - 89.45.14.12
casinosupernet.ru - 89.45.14.12
casino-super-net.ru - 89.45.14.12
casino-super-online.ru - 90.182.175.234
casinosupervip.ru - 89.45.14.12
casino-super-vip.ru - 89.45.14.12
casinosuperweb.ru - 89.45.14.12
casino-super-web.ru - 89.45.14.12
casinosuperwin.ru - 89.45.14.12
casino-super-win.ru - 89.45.14.12
casinovipsuper.ru - 89.45.14.12
casino-vip-super.ru - 89.45.14.12
casino-win-super.ru - 89.45.14.12
cazino-cash-multi.ru - 89.45.14.12
3cazino-party-royal.ru - 89.45.14.12
cazinopartyweb.ru - 89.45.14.12
cazino-party-web.ru - 89.45.14.12
cazinopartywin.ru - 89.45.14.12
cazino-party-win.ru - 89.45.14.12
cazinoplazawin.ru - 89.45.14.12
cazinoplazaworld.ru - 89.45.14.12
cazino-plaza-world.ru - 89.45.14.12
cazinowinplaza.ru - 89.45.14.12
cazino-win-plaza.ru - 89.45.14.12
cazinoworldplaza.ru - 89.45.14.12
cazino-world-plaza.ru - 89.45.14.12
4elitcasinosuper.ru - 89.45.14.12
elit-casino-super.ru - 89.45.14.12
elitsupercasino.ru - 89.45.14.12
elit-super-casino.ru - 89.45.14.12
gamelabonline.ru - 78.46.105.205
gameonlinelab.ru - 78.46.105.205
game-party-royal.ru - 78.46.105.205
gamezlabonline.ru - 89.45.14.12
gamezmultilab.ru - 89.45.14.12
gamez-net-online.ru - 89.45.14.12
gamezonlinenet.ru - 89.45.14.12
gamez-party-royal.ru - 89.45.14.12
gamez-party-web.ru - 89.45.14.12
gamezpartywin.ru - 89.45.14.12
gamez-party-win.ru - 89.45.14.12
gamez-plaza-win.ru - 89.45.14.12
gamezplazaworld.ru - 89.45.14.12
gamez-plaza-world.ru - 89.45.14.12
gamez-vegas-web.ru - 89.45.14.12
gamezweblab.ru - 89.45.14.12
gamezwinplaza.ru - 89.45.14.12
gamez-win-plaza.ru - 89.45.14.12
gamezworldplaza.ru - 89.45.14.12
joker-gamez-web.ru - 89.45.14.12
kingcasinosuper.ru - 89.45.14.12
king-casino-super.ru - 89.45.14.12
kinggagnerr.net - 90.182.175.234
kingsupercasino.ru - 89.45.14.12
king-super-casino.ru - 89.45.14.12
lab-cazino-multi.ru - 89.45.14.12
lab-cazino-online.ru - 89.45.14.12
labgamezonline.ru - 89.45.14.12
lab-gamez-web.ru - 89.45.14.12
labonlinecazino.ru - 89.45.14.12
labonlinegame.ru - 78.46.105.205
labvegascazino.ru - 89.45.14.12
luxcasinosuper.ru - 89.45.14.12
luxnextcasino.ru - 89.45.14.12
lux-next-casino.ru - 89.45.14.12
multicasinosuper.ru - 89.45.14.12
multilabgame.ru - 78.46.105.205
multisupercasino.ru - 89.45.14.12
netcasinosuper.ru - 89.45.14.12
net-casino-super.ru - 89.45.14.12
netpartycazino.ru - 89.45.14.12
netsupercasino.ru - 89.45.14.12
net-super-casino.ru - 89.45.14.12
nextcasinovip.ru - 89.45.14.12
next-casino-vip.ru - 89.45.14.12
next-lux-casino.ru - 89.45.14.12
nextvipcasino.ru - 89.45.14.12
onlinecasinosuper.ru - 90.182.175.234
online-casino-super.ru - 90.182.175.234
online-cazino-lab.ru - 89.45.14.12
onlinegameznet.ru - 89.45.14.12
online-gamez-vip.ru - 89.45.14.12
onlinelabcazino.ru - 89.45.14.12
onlinesupercasino.ru - 90.182.175.234
online-super-casino.ru - 90.182.175.234
partycasinosuper.ru - 90.182.175.234
party-casino-web.ru - 78.46.105.205
partycazinonet.ru - 89.45.14.12
party-cazino-royal.ru - 89.45.14.12
partycazinoweb.ru - 89.45.14.12
partycazinowin.ru - 89.45.14.12
partygamezroyal.ru - 89.45.14.12
party-gamez-royal.ru - 89.45.14.12
partygamezwin.ru - 89.45.14.12
party-gamez-win.ru - 89.45.14.12
partynetcazino.ru - 89.45.14.12
party-royal-cazino.ru - 89.45.14.12
party-super-casino.ru - 89.45.14.12
partywebcasino.ru - 78.46.105.205
partywebcazino.ru - 89.45.14.12
partywincazino.ru - 89.45.14.12
party-win-cazino.ru - 89.45.14.12
play-multi-casino.ru - 89.45.14.12
plazacazinowin.ru - 89.45.14.12
plaza-cazino-win.ru - 89.45.14.12
plazacazinoworld.ru - 89.45.14.12
plaza-cazino-world.ru - 89.45.14.12
plaza-gamez-win.ru - 89.45.14.12
plazagamezworld.ru - 89.45.14.12
plaza-gamez-world.ru - 89.45.14.12
plazawincazino.ru - 89.45.14.12
plaza-win-cazino.ru - 89.45.14.12
plazaworldcazino.ru - 89.45.14.12
plaza-world-cazino.ru - 89.45.14.12
royal-party-cazino.ru - 89.45.14.12
star-casino-super.ru - 90.182.175.234
star-super-casino.ru - 90.182.175.234
super-casino-elit.ru - 89.45.14.12
supercasinoking.ru - 89.45.14.12
super-casino-king.ru - 89.45.14.12
supercasinolab.ru - 89.45.14.12
super-casino-land.ru - 90.182.175.234
supercasinomulti.ru - 89.45.14.12
supercasinonet.ru - 89.45.14.12
super-casino-net.ru - 89.45.14.12
supercasinoonline.ru - 90.182.175.234
super-casino-online.ru - 90.182.175.234
super-casino-star.ru - 90.182.175.234
supercasinovip.ru - 89.45.14.12
super-casino-vip.ru - 89.45.14.12
super-casino-web.ru - 89.45.14.12
super-casino-west.ru - 90.182.175.234
supercasinowin.ru - 89.45.14.12
super-casino-win.ru - 89.45.14.12
super-elit-casino.ru - 89.45.14.12
superkingcasino.ru - 89.45.14.12
super-king-casino.ru - 89.45.14.12
super-land-casino.ru - 90.182.175.234
super-multi-casino.ru - 89.45.14.12
supernetcasino.ru - 89.45.14.12
super-net-casino.ru - 89.45.14.12
superonlinecasino.ru - 90.182.175.234
super-online-casino.ru - 90.182.175.234
superpartycasino.ru - 90.182.175.234
super-party-casino.ru - 89.45.14.12
superstarcasino.ru - 90.182.175.234
super-star-casino.ru - 90.182.175.234
super-vip-casino.ru - 89.45.14.12
super-web-casino.ru - 89.45.14.12
super-west-casino.ru - 90.182.175.234
superwincasino.ru - 89.45.14.12
vegas-game-web.ru - 78.46.105.205
vegas-gamez-multi.ru - 89.45.14.12
vegasgamezweb.ru - 89.45.14.12
vipcasinosuper.ru - 89.45.14.12
vip-casino-super.ru - 89.45.14.12
vipnextcasino.ru - 89.45.14.12
vipsupercasino.ru - 89.45.14.12
vip-super-casino.ru - 89.45.14.12
web-casino-super.ru - 89.45.14.12
web-cazino-royal.ru - 89.45.14.12
webgamezroyal.ru - 89.45.14.12
webpartycazino.ru - 89.45.14.12
web-super-casino.ru - 89.45.14.12
west-super-casino.ru - 90.182.175.234
wincasinosuper.ru - 89.45.14.12
win-casino-super.ru - 89.45.14.12
win-cazino-plaza.ru - 89.45.14.12
win-gamez-plaza.ru - 89.45.14.12
winpartycazino.ru - 89.45.14.12
win-party-cazino.ru - 89.45.14.12
winplazacazino.ru - 89.45.14.12
win-plaza-cazino.ru - 89.45.14.12
winsupercasino.ru - 89.45.14.12
win-super-casino.ru - 89.45.14.12
worldcazinoplaza.ru - 89.45.14.12
world-cazino-plaza.ru - 89.45.14.12
worldgamezplaza.ru - 89.45.14.12
world-gamez-plaza.ru - 89.45.14.12
world-plaza-cazino.ru - 89.45.14.12
Monitoring of the campaign is ongoing.
Related posts:
Don't Play Poker on an Infected Table - Part Four
Don't Play Poker on an Infected Table - Part Three
Don't Play Poker on an Infected Table - Part Two
Don't Play Poker on an Infected Table
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Summarizing ZDNet's Zero Day Posts for April
The following is a brief summary of all of my posts at ZDNet's Zero Day for April. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
Recommended reading:
01. Spamvertised "Reqest Rejected" campaign leads to scareware
02. Spamvertised 'Facebook. Your password has been changed!' emails lead to malware
03. Malware Watch: 'Spam is sent from your FaceBook account'; Spamvertised malicious photos
04. Spamvertised Easter Greetings lead to malware
05. Netcraft survey indicates slow adoption of Extended Validation SSL certificates
06. 'You've got a postcard' emails lead to exploits and scareware
07. Fake antivirus for mobile platform spotted
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Thursday, April 28, 2011
Spamvertised "Successfull Order 977132" Leads to Scareware
A currently ongoing malware campaign is impersonating Bobijou Inc for malware-serving purposes.
Sample subject: "Successfull Order 977132"
Sample message: "Thank you for ordering from Bobijou Inc.This message is to inform you that your order has been received and is currently being processed.
Your order reference is 901802. You will need this in all correspondence. This receipt is NOT proof of purchase. We will send a printed invoice by mail to your billing address.
You have chosen to pay by credit card. Your card will be charged for the amount of 262.00 USD and “Bobijou Inc.” will appear next to the charge on your statement.You will receive a separate email confirming your order has been despatched.Your purchase and delivery information appears below in attached file.
Thanks again for shopping at Bobijou Inc."
Sample attachments: Order_details.zip
Detection rates:
Order details.exe - Trojan.FakeAV - Result: 24/40 (60.0%)
MD5 : 7c810cbb47c9f937b5f663b51ab7ee50
SHA1 : b4faf8c724727381abb11c44b71605ff6e65cbbf
SHA256: 0bda3bdcffdda0fee31fe35cfea2fb644ff8e549a0a83632faa19cd43e02b904
Upon execution phones back to :
kkojjors.net/f/g.php - 95.64.9.15 - Email: admin@firtryt.biz
variantov.com/pusk.exe - 94.63.149.26 - Email: admin@variantov.com
Detection rate for the scareware variant pusk.exe
pusk.exe - Suspicious.Cloud.5 - Result: 4/41 (9.8%)
MD5 : bbd466a67586003776e295eaf3d2976c
SHA1 : 6a8e1d84157c76b4c9238fc23d28686244f6650f
SHA256: ee008f9039534f062bd277860060461064e760bdaa90a36595b9780be54a5a05
Upon execution phones back to:
jyluzovunevu.com - 209.160.45.33 - Email: gray@fxmail.net
sesokiqufikeg.com - 209.160.45.34 - Email: gray@fxmail.net
qyqinisope.com - 64.46.38.207 - Email: gray@fxmail.net
hijocyragap.com - 64.46.38.81 - Email: robin@cutemail.org
puhigygapyhi.com - 64.46.38.81 - Email: gray@fxmail.net
zavewuzykubo.com - 64.46.38.80 - Email: robin@cutemail.org
fepigixypo.com - 64.46.38.29 - Email: pyre@cutemail.org
tozibapah.com - 76.73.16.182 - Email: lays@fxmail.net
qebinehuh.com - 76.73.14.182 - Email: lays@fxmail.net
gygipikalyn.com - 76.73.17.242 - Email: ss@cutemail.org
xygorinazecit.com - 76.73.17.70 - Email: ss@cutemail.org
walireqoxyxyt.com - 64.46.39.185 - Email: orbit@fxmail.net
moririnejuf.com - 64.46.39.184 - Email: purse@mail13.com
jydosucin.com - 64.46.39.200 - Email: arm@fxmail.net
libynozegokido.com - 64.46.39.186 - Email: orbit@fxmail.net
zidacofodafur.com - 64.46.39.212 - Email: gown@cutemail.org
fequxukovo.com - 67.196.15.136 - Email: arm@fxmail.net
gyxyqimacik.com - 67.196.15.138 - Email: purse@mail13.com
wizyvopyla.com - 67.196.15.137 - Email: arm@fxmail.net
gyricehagupy.com - 67.196.15.139 - Email: purse@mail13.com
punemipaqatyc.com - 67.196.15.141 - Email: ulcer@mailae.com
gehotigyry.com - 67.196.15.140 - Email: hp@mail13.com
vufekihoto.com - 67.196.15.105 - Email: arm@fxmail.net
huzomohidid.com - 67.196.15.104 - Email: arm@fxmail.net
posufejez.com - 67.196.15.107 - Email: purse@mail13.com
gewexyvunokyk.com - 67.196.15.106 - Email: purse@mail13.com
fowyqypacytucy.com - 209.160.45.32 - Email: soup@fastermail.ru
koduzuwobow.com - 209.160.45.130 - Email: pyre@cutemail.org
ciluvekypomow.com - 78.46.105.205 - Email: hips@cutemail.org
7hitaxodupi.com - 64.46.38.30
Monitoring of the campaign is ongoing.
Related posts:
Spamvertised "Reqest Rejected" Campaign Serving Scareware
Spamvertised DHL Notifications Scareware Campaign
Spamvertised Post Office Express Mail (USPS) Emails Serving Malware
Spamvertised United Parcel Service notifications serve malware
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
Sample subject: "Successfull Order 977132"
Sample message: "Thank you for ordering from Bobijou Inc.This message is to inform you that your order has been received and is currently being processed.
Your order reference is 901802. You will need this in all correspondence. This receipt is NOT proof of purchase. We will send a printed invoice by mail to your billing address.
You have chosen to pay by credit card. Your card will be charged for the amount of 262.00 USD and “Bobijou Inc.” will appear next to the charge on your statement.You will receive a separate email confirming your order has been despatched.Your purchase and delivery information appears below in attached file.
Thanks again for shopping at Bobijou Inc."
Sample attachments: Order_details.zip
Detection rates:
Order details.exe - Trojan.FakeAV - Result: 24/40 (60.0%)
MD5 : 7c810cbb47c9f937b5f663b51ab7ee50
SHA1 : b4faf8c724727381abb11c44b71605ff6e65cbbf
SHA256: 0bda3bdcffdda0fee31fe35cfea2fb644ff8e549a0a83632faa19cd43e02b904
Upon execution phones back to :
kkojjors.net/f/g.php - 95.64.9.15 - Email: admin@firtryt.biz
variantov.com/pusk.exe - 94.63.149.26 - Email: admin@variantov.com
Detection rate for the scareware variant pusk.exe
pusk.exe - Suspicious.Cloud.5 - Result: 4/41 (9.8%)
MD5 : bbd466a67586003776e295eaf3d2976c
SHA1 : 6a8e1d84157c76b4c9238fc23d28686244f6650f
SHA256: ee008f9039534f062bd277860060461064e760bdaa90a36595b9780be54a5a05
Upon execution phones back to:
jyluzovunevu.com - 209.160.45.33 - Email: gray@fxmail.net
sesokiqufikeg.com - 209.160.45.34 - Email: gray@fxmail.net
qyqinisope.com - 64.46.38.207 - Email: gray@fxmail.net
hijocyragap.com - 64.46.38.81 - Email: robin@cutemail.org
puhigygapyhi.com - 64.46.38.81 - Email: gray@fxmail.net
zavewuzykubo.com - 64.46.38.80 - Email: robin@cutemail.org
fepigixypo.com - 64.46.38.29 - Email: pyre@cutemail.org
tozibapah.com - 76.73.16.182 - Email: lays@fxmail.net
qebinehuh.com - 76.73.14.182 - Email: lays@fxmail.net
gygipikalyn.com - 76.73.17.242 - Email: ss@cutemail.org
xygorinazecit.com - 76.73.17.70 - Email: ss@cutemail.org
walireqoxyxyt.com - 64.46.39.185 - Email: orbit@fxmail.net
moririnejuf.com - 64.46.39.184 - Email: purse@mail13.com
jydosucin.com - 64.46.39.200 - Email: arm@fxmail.net
libynozegokido.com - 64.46.39.186 - Email: orbit@fxmail.net
zidacofodafur.com - 64.46.39.212 - Email: gown@cutemail.org
fequxukovo.com - 67.196.15.136 - Email: arm@fxmail.net
gyxyqimacik.com - 67.196.15.138 - Email: purse@mail13.com
wizyvopyla.com - 67.196.15.137 - Email: arm@fxmail.net
gyricehagupy.com - 67.196.15.139 - Email: purse@mail13.com
punemipaqatyc.com - 67.196.15.141 - Email: ulcer@mailae.com
gehotigyry.com - 67.196.15.140 - Email: hp@mail13.com
vufekihoto.com - 67.196.15.105 - Email: arm@fxmail.net
huzomohidid.com - 67.196.15.104 - Email: arm@fxmail.net
posufejez.com - 67.196.15.107 - Email: purse@mail13.com
gewexyvunokyk.com - 67.196.15.106 - Email: purse@mail13.com
fowyqypacytucy.com - 209.160.45.32 - Email: soup@fastermail.ru
koduzuwobow.com - 209.160.45.130 - Email: pyre@cutemail.org
ciluvekypomow.com - 78.46.105.205 - Email: hips@cutemail.org
7hitaxodupi.com - 64.46.38.30
Monitoring of the campaign is ongoing.
Related posts:
Spamvertised "Reqest Rejected" Campaign Serving Scareware
Spamvertised DHL Notifications Scareware Campaign
Spamvertised Post Office Express Mail (USPS) Emails Serving Malware
Spamvertised United Parcel Service notifications serve malware
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Tuesday, April 12, 2011
Spamvertised "Reqest Rejected" Campaign Serving Scareware
A currently spamvertised scareware-serving campaign is enticing end users into downloading and executing a malicious binary, which drops a scareware variant.
Sample subject: Reqest rejected
Sample message: "Dear Sirs, Thank you for your letter! Unfortunately we can not confirm your request! More information attached in document below. Thank you Best regards."
Sample attachments: EX-38463.pdf.zip; EX-38463.pdf.exe
Detection rate:
EX-38463.pdf.exe - TrojanDownloader:Win32/Chepvil.J - Result: 11/41 (26.8%)
MD5 : 5085794e6c283ebcfa3878805b9e7be7
SHA1 : 1fbd8d3b0a3479274d8f09543452bf724bcb245c
SHA256: c03711dbafae9b296daed8720f997d84caa5e5a5407a689926050a061d67b932
Upon execution downloads hdjfskh.net/ pusk.exe - 208.43.90.48 - Email: admin@firtryt.biz
Detection rate:
pusk.exe - FakeAlert-CN.gen.aa - Result: 13/42 (31.0%)
MD5 : a50a91176b5aeb96b8b77b99d587c485
SHA1 : c56b7ab2123dbd49902446ffcc0cf59d6a865857
SHA256: c912a975e3c2fc911d6550d86e8fd89dbd30e3d1e07d788b45aac0d6cf61e83c
Upon execution phones back to the following domains and ASs:
Phones back to : AS19875; AS8001; AS24940; AS32475; AS32097; AS19875
2bemojewedowigo.com - 78.46.105.205
bemolaqijicy.com - 99.198.114.206 - Email: vista@free-id.ru
celisesuho.com - 99.198.114.202 - Email: hush@bz3.ru
cixovatywo.com - 78.46.105.205 - Email: frenzy@ca4.ru
fytypoqywu.com - 64.46.38.94 - Email: fy4371215910301@domainidshield.com
gicyxepomer.com - 78.46.105.205 - Email: tabs@yourisp.ru
gopilezavyxiro.com - 78.46.105.205 - Email: hush@bz3.ru
hivanedak.com - 188.95.54.242 - Email: steps@ppmail.ru
hotilosire.com - 208.110.67.122 - Email: lathe@maillife.ru
jerakidukojoz.com - 78.46.105.205 - Email: wrap@cheapbox.ru
kupeqobujohaq.com - 64.46.38.145 - Email: soup@fastermail.ru
kytevaviqopoci.com - 78.46.105.205 - Email: fs@free-id.ru
pikilokykizanu.com - 65.254.54.77 - Email: dawn@free-id.ru
punajytapaci.com - 209.97.213.105 - Email: mire@maillife.ru
qisacugugu.com - 64.46.38.129 - Email: as@free-id.ru
qupajubica.com - 78.46.105.205 - Email: heard@bz3.ru
reruravobosila.com - 67.196.13.96 - Email: mon@ppmail.ru
rorodarof.com - 99.198.114.204 - Email: hush@bz3.ru
ruqydahec.com - 67.196.13.97 - Email: mon@ppmail.ru
sakafiduzipame.com - 78.46.105.205 - Email: build@ca4.ru
sykobodyducib.com - 208.110.67.102 - Email: lathe@maillife.ru
tetagyjaj.com - 78.46.105.205 - Email: kilt@bz3.ru
tibehewuk.com - 209.97.213.102 - Email: mon@ppmail.ru
tisatosyhimidy.com - 188.95.54.243 - Email: jan@free-id.ru
tyhiqymiwufuj.com - 208.110.67.121 - Email: dawn@free-id.ru
vakyditefo.com - 99.198.114.203 - Email: vista@free-id.ru
wamojafadezy.com - 78.46.105.205 - Email: acts@free-id.ru
wetotyger.com - 78.46.105.205 - Email: acts@free-id.ru
wixecyhobovy.com - 64.46.38.130 - Email: soup@fastermail.ru
wolycunanoqe.com - 72.9.233.98 - Email: lathe@maillife.ru
zajatimibuj.com - 208.110.67.119 - Email: bark@cheapbox.ru
zequcitamado.com - 99.198.114.205 - Email: vista@free-id.ru
punajytapaci.com/1017000412 - 209.97.213.105 - Email: mire@maillife.ru
tibehewuk.com/1017000412 - 209.97.213.102 - Email: mon@ppmail.ru
Monitoring of the campaign is ongoing.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Monday, April 11, 2011
Don't Play Poker on an Infected Table - Part Four
A currently spamvertised campaign is enticing users into downloading and executing a fraudulent online gambling application known as VegasVIP_setup.exe.
Detection rate:
VegasVIP_setup.exe - Win32/CazinoSilver - Result:16/42 (38.1%)
MD5 : 8680fa2868dd068f3c1d3995df105243
SHA1 : 4f3ecd72c223cf6e130377a3ecd9149232dc848b
SHA256: 68ded50bf7c9b7f6961e6334b25fdad5d2369e461051d5a9fa1f1ebaadeb1d0e
Upon execution, the sample phones back to:
www.onlinevegas.com/download/update.php?dl=0af374526b7b6eb6c54bf92cb1d1a236&status=10
The spammers are earning revenue by participating in the BestCasinoPartner.com Affiliate Program. More details:
"Turn Your Traffic Into BIG Monthly Cash! Join the BestCasinoPartner.com Affiliate Program and from the very start you will earn a HUGE 30% of ALL player GROSS losses EVERY month, no matter what your volume is! That’s ALL player GROSS losses for the life of your referred players, with No Loss Carry-Forward!
Refer an Affiliate: Get Even More. Earn 7% override on the Casino Gross Revenue payment made to the referred Affiliate for all players referred by your directly referred Affiliates - for the life of the player! Earn 5% override on the Casino Gross Revenue payment made from your Web masters’ referrals! AND…we even go One Step Further — a THIRD tier!
Here are the THREE levels that will earn you profits for the life EACH player:
- Tier 1: 7% override on the Casino Gross Revenue
- Tier 2: 5% override on the Casino Gross Revenue
- Tier 3: 3% override on the Casino Gross Revenue"
Participating affiliate domains are: OnlineVegas.com; GoCasino.com; CrazySlots.com and GrandVegas.com
Related fraudulent online gambling domains part of the campaign:
777fashionplays.ru
777playsfashion.ru
bankpremiumplays.ru
bank-premium-plays.ru
bestfortuneplays.ru
best-fortune-plays.ru
bestplaysfortune.ru
best-plays-fortune.ru
bingobonusplays.ru
bonus-bingo-plays.ru
bonusplaysbingo.ru
bonus-plays-bingo.ru
class-plays-world.ru
class-world-plays.ru
crazyplaysroulette.ru
crazy-plays-roulette.ru
crazyrouletteplays.ru
crazy-roulette-plays.ru
elit-grand-games.ru
elit-plays-king.ru
fashion-plays-vegas.ru
fashion-vegas-plays.ru
fiveplaysstar.ru
fortunebestplays.ru
fortune-best-plays.ru
fortuneplaysbest.ru
fortune-plays-best.ru
fortune-plays-land.ru
fortuneplaysparty.ru
fortune-plays-party.ru
games-elit-king.ru
games-king-elit.ru
gamespremiumbank.ru
jokerplaysvegas.ru
online-games-luxory.ru
palaceplayscrystal.ru
playsbankpremium.ru
plays-bank-premium.ru
playsbestfortune.ru
plays-best-fortune.ru
plays-bingo-bonus.ru
playsbonusbingo.ru
plays-bonus-bingo.ru
playsclassworld.ru
playscrazyroulette.ru
plays-crazy-roulette.ru
playscrystalpalace.ru
plays-crystal-palace.ru
playsfashion777.ru
playsfivestar.ru
playsfortunebest.ru
plays-fortune-party.ru
playsonlineextra.ru
plays-plaza-west.ru
playspremiumbank.ru
playsroulettecrazy.ru
plays-roulette-crazy.ru
plays-royal-classic.ru
plays-star-five.ru
playsvegasjoker.ru
playswestplaza.ru
plays-world-win.ru
plaza-plays-west.ru
plazawestplays.ru
plaza-west-plays.ru
premium-bank-plays.ru
premiumplaysbank.ru
roulette-crazy-plays.ru
starfiveplays.ru
star-five-plays.ru
starplaysfive.ru
vegas-fashion-plays.ru
vegasjokergames.ru
vegasjokerplays.ru
vegas-joker-plays.ru
vegas-plays-joker.ru
westplaysplaza.ru
west-plays-plaza.ru
westplazaplays.ru
west-plaza-plays.ru
win-plays-world.ru
winworldplays.ru
win-world-plays.ru
world-class-plays.ru
world-plays-class.ru
Related posts:
Don't Play Poker on an Infected Table - Part Three
Don't Play Poker on an Infected Table - Part Two
Don't Play Poker on an Infected Table
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Monday, April 04, 2011
Summarizing Zero Day's Posts for March
The following is a brief summary of all of my posts at ZDNet's Zero Day for March. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
Recommended reading:
- Dear ISP, it's time to quarantine your malware-infected customers
- Zombie PC Prevention Bill to make security software mandatory
02. Report: malicious PDF files becoming the attack vector of choice
03. Ashton Kutcher's Twitter account hacked
04. Google tops comparative review of malicious search results -- again
05. Report: 3 million malvertising impressions served per day
06. Dear ISP, it's time to quarantine your malware-infected customers
07. SpyEye gets new DDoS functionality
08. Spamvertised DHL notifications lead to malware
09. Spamvertised FedEx notifications lead to malware
10. Rustock botnet's operations disrupted
11. Malicious Japan quake spam leads to scareware
12. Spamvertised United Parcel Service notifications lead to malware
13. Researchers release details on 34 SCADA vulnerabilities
14. Zombie PC Prevention Bill to make security software mandatory
15. Spamvertised Post Office Express Mail (USPS) emails lead to malware
16. New GpCode ransomware encrypts files, demands $125 for decryption
17. Mass SQL injection attack leads to scareware
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Spamvertised DHL Notifications Scareware Campaign
Sample subjects: DHL notification #random number
Sample message: Dear customer! The parcel was send your home address. And it will arrice within 7 bussness day. More information and the tracking number are attached in document below. Thank you. 2011 DHL International GmbH. All rights reserverd.
Sample filenames: DHL_tracking.zip; doc.zip; dhl.zip
Detection rates:
dhl.exe - Backdoor:Win32/Hostil.gen!A - Result: 22/40 (55.0%)
MD5 : 87d778169ae14d934b92ce628b5cfde4
SHA1 : 20787fde3b7fde64cc3892c4df9a4eb2a2515830
SHA256: 6b54ff520fa6ff504f5f2f0c33af8b92424f0b538a760f4eb983d76007d3fe54
Downloads additional binary from puskovayaustanovka.ru/pusk2.exe - 46.161.20.66 - Email: admin@puskovayaustanovka.ru
pusk2.exe - Trojan.Fakealert.20509 - Result: 11/41 (26.8%)
MD5 : a9be091eedea947f8626d11042e0d9be
SHA1 : 9c1d399d47a6ef6081553a101ab48fca61859db4
SHA256: d4f5802a392c0851d5e19118d56cc8b578f1a07085aa5772cbdcf484608ed094
Upon execution phones back to the following domains:
kynugypenihyf.com - Email: v8@ca4.ru
cylakydugudi.com - Email: acts@free-id.ru
fevahanybyvu.com - Email: fs@free-id.ru
gicyxepomer.com - Email: tabs@yourisp.ru
bemojewedowigo.com - Email: fs@free-id.ru
sakafiduzipame.com - Email: build@ca4.ru
wetotyger.com - Email: acts@free-id.ru
kytevaviqopoci.com - Email: fs@free-id.ru
wamojafadezy.com - Email: kilt@bz3.ru
tetagyjaj.com - Email: kilt@bz3.ru
jerakidukojoz.com - Email: wrap@cheapbox.ru
cixovatywo.com - Email: frenzy@ca4.ru
jafybobik.com - Email: force@ca4.ru
nizokatahinery.com - Email: foxy@cheapbox.ru
cujicaraso.com - Email: beret@ca4.ru
zuzosahule.com - Email: only@free-id.ru
gokuzajylot.com - Email: silks@ca4.ru
jumonevetode.com - Email: silks@ca4.ru
dafatesomyz.com - Email: zq@bz3.ru
lukofymela.com - Email: silks@ca4.ru
jebuponip.com - Email: lost@free-id.ru
quxovasuced.com - Email: hp@ppmail.ru
laqoduhisegu.com - Email: shot@bz3.ru
xyseditacif.com - Email: hart@free-id.ru
wylyxaqunowy.com - Email: mows@bz3.ru
qepovexidysopy.com - Email: byob@yourisp.ru
bebecebyt.com - Email: mows@bz3.ru
dihemehypuq.com - Email: shot@bz3.ru
rumesexyzobuz.com - Email: dawn@bz3.ru
gopilezavyxiro.com - Email: hush@bz3.ru
hyvijinymut.com/1017000312 - 99.198.114.189 - returns OK
Domains are respoding to the following ASs: AS18866; AS32097:
quxovasuced.com - 69.50.209.139
laqoduhisegu.com - 69.50.209.140
wylyxaqunowy.com - 69.50.209.148
qepovexidysopy.com - 69.50.209.149
fevahanybyvu.com - 69.50.209.182
bemojewedowigo.com - 69.50.209.183
gicyxepomer.com - 69.50.209.184
sakafiduzipame.com - 69.50.209.185
wamojafadezy.com - 69.50.209.186
kytevaviqopoci.com - 69.50.209.188
jebuponip.com - 69.50.209.223
cylakydugudi.com - 69.50.209.224
wetotyger.com - 69.50.209.225
nizokatahinery.com - 69.197.161.202
cujicaraso.com - 69.197.161.203
kynugypenihyf.com - 69.197.161.204
jafybobik.com - 69.197.161.205
tetagyjaj.com - 99.198.114.98
jerakidukojoz.com - 99.198.114.99
gopilezavyxiro.com - 99.198.114.100
cixovatywo.com - 99.198.114.101
hyvijinymut.com - 99.198.114.189
zuzosahule.com - 204.12.223.170
jumonevetode.com - 204.12.223.171
dafatesomyz.com - 204.12.223.172
gokuzajylot.com - 204.12.223.173
lukofymela.com - 204.12.223.174
rumesexyzobuz.com - 204.12.223.186
xyseditacif.com - 204.12.223.187
dihemehypuq.com - 204.12.223.188
bebecebyt.com - 204.12.223.189
Monitoring of the campaign is ongoing.
Related posts:
Spamvertised Post Office Express Mail (USPS) Emails Serving Malware
Spamvertised United Parcel Service notifications serve malware
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Thursday, March 31, 2011
Dissecting the Massive SQL Injection Attack Serving Scareware
A currently ongoing massive SQL injection attack has affected hundreds of thousands of web pages across the Web, to ultimately monetize the campaign through a scareware affiliate program. Such massive SQL injection attempts are usually conducted using mass vulnerability scanning tools, with the help of search engines which have already crawled the vulnerable sites.
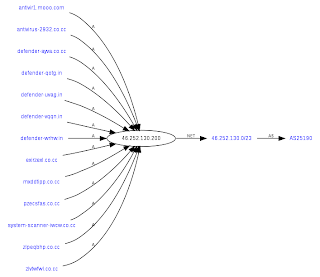
What's particularly interesting about this campaign, is the fact that the used domains are all responding to the same IPs, including the portfolios of scareware domains, which the cybercriminals naturally rotate on a periodic basis. Let's dissect the campaign, expose the domain portfolios and the entire campaign structure.
UPDATED: Related SQL injected URLs courtsesy of WebSense:
online-stats201.info/ur.php - Email: tik0066@gmail.com
stats-master111.info/ur.php - Email: tik0066@gmail.com
agasi-story.info/ur.php - 91.217.162.45 - Email: tik0066@gmail.com
general-st.info/ur.php - Email: tik0066@gmail.com
extra-service.info/ur.php - Email: tik0066@gmail.com
sol-stats.info/ur.php - Email: tik0066@gmail.com
google-stats49.info/ur.php - Email: tik0066@gmail.com
google-stats45.info/ur.php - Email: tik0066@gmail.com
google-stats50.info/ur.php - Email: tik0066@gmail.com
google-server43.info/ur.php - Email: tik0066@gmail.com
stats-master88.info/ur.php - Email: tik0066@gmail.com
eva-marine.info/ur.php - 109.236.81.28 - Email: tik0066@gmail.com
stats-master99.info/ur.php - Email: tik0066@gmail.com
tzv-stats.info/ur.php - Email: tik0066@gmail.com
milapop.com/ur.php - Email: jamesnorthone@hotmailbox.com
SQL injected URLs:
lizamoon.com/ur.php (67,500 results) - 91.220.35.151 (AS3721); 91.213.29.182 (AS51786); 95.64.9.18 (AS50244) - Email: jamesnorthone@hotmailbox.com
alexblane.com/ur.php (3,920 results) - Email: jamesnorthone@hotmailbox.com
alisa-carter.com/ur.php (220,000 results) - Email: jamesnorthone@hotmailbox.com
alexblane.com/ur.php (3,920 results) - Email: jamesnorthone@hotmailbox.com
t6ryt56.info/ur.php (18 results) - Email: support@ruler-domains.com
tadygus.com/ur.php (100 results) - Email: jamesnorthone@hotmailbox.com
worid-of-books.com/ur.php (334,000 results) - Email: tik0066@gmail.com
Upon successful redirection, the campaign attempts to load the scareware domains defender-nibea.in/scan1b/237 - 46.252.130.200 - Email: jimwei2969@gmail.com
Detection rate:
freesystemscan.exe - Trojan/Win32.FakeAV - Result: 9/ 41 (22.0%)
MD5 : 815d77f8fca509dde1abeafabed30b65
SHA1 : 1b3c35afb76c53cd9507fffee46fb58c29e72bc1
SHA256: cd902b92042435c2d70d4bf59acc2de8229bfc367626961f76c03f75dcd7e95c
Responding to 46.252.130.200 (AS25190; KIS-AS UAB "Kauno Interneto Sistemos") are also:
antivirus-1091.co.cc
antivirus-1574.co.cc
antivirus-2051.co.cc
antivirus-2525.co.cc
antivirus-2932.co.cc
antivirus-3654.co.cc
antivirus-3833.co.cc
antivirus-4063.co.cc
antivirus-418.co.cc
antivirus-4303.co.cc
antivirus-4749.co.cc
antivirus-495.co.cc
antivirus-5216.co.cc
antivirus-5676.co.cc
antivirus-5802.co.cc
antivirus-6437.co.cc
antivirus-6703.co.cc
antivirus-7081.co.cc
antivirus-713.co.cc
antivirus-728.co.cc
antivirus-7357.co.cc
antivirus-8072.co.cc
antivirus-9009.co.cc
antivirus-9638.co.cc
antivirus-9667.co.cc
defender-aabv.in - Email: leonflanagan7681@gmail.com
defender-aqeu.co.cc
defender-asng.co.cc
defender-atio.in - Email: terriduverger3239@gmail.com
defender-atxo.in - Email: celineiebba9266@gmail.com
defender-bcvs.in - Email: martinefinklea5375@gmail.com
defender-bwuy.co.cc
defender-cron.in - Email: lisasuresh9147@gmail.com
defender-ddbr.in - Email: selenajohansson9195@gmail.com
defender-dteo.in - Email: giovannaraggio5417@gmail.com
defender-eahy.co.cc
defender-eklq.in - Email: sebastiensheppard8680@gmail.com
defender-endl.in - Email: adamgaylard1113@gmail.com
defender-ewum.co.cc
defender-eyde.co.cc
defender-fmof.in - Email: kamillamartin1237@gmail.com
defender-fola.co.cc
defender-gnva.in - Email: ananddaher7294@gmail.com
defender-grlt.in - Email: anthonygaylard9887@gmail.com
defender-hipw.in - Email: angiejohansen9730@gmail.com
defender-hjlk.in - Email: jennwrayford2124@gmail.com
defender-hmfu.in - Email: lynnbone8026@gmail.com
defender-hsug.in - Email: moniquetkarnopp3596@gmail.com
defender-htlu.in - Email: jerihamann4163@gmail.com
defender-iibk.co.cc
defender-iies.co.cc
defender-iksl.in - Email: amarasanders9974@gmail.com
defender-isde.co.cc
defender-iyrc.co.cc
defender-jgnl.in - Email: caseyalzen3316@gmail.com
defender-jihv.co.cc
defender-keod.in - Email: khashayarbirss4814@gmail.com
defender-kuts.in - Email: rogerfrancis3322@gmail.com
defender-kwwh.in - Email: tobyboisseau6505@gmail.com
defender-kzwu.co.cc
defender-labm.in - Email: gregorybradford1520@gmail.com
defender-lcoh.in - Email: timothythomas6924@gmail.com
defender-nhei.co.cc
defender-nrpr.in - Email: burtonalba8156@gmail.com
defender-ojbr.in - Email: fucknielsen8675@gmail.com
defender-osbi.in - Email: fidelslattum2159@gmail.com
defender-pakc.in - Email: sabrinawheelock7642@gmail.com
defender-ppdw.in - Email: divinakempton5670@gmail.com
defender-qfdx.in - Email: hokyeongyancey6369@gmail.com
defender-qotg.in - Email: franchescaili9704@gmail.com
defender-qpwo.in - Email: carlaadams@gmail.com
defender-qsko.co.cc
defender-qumf.in - Email: carlaadams@gmail.com
defender-rlag.in - Email: carmichaelmail@gmail.com
defender-rrin.in - Email: kevincharoenset5321@gmail.com
defender-thga.in - Email: youngantonio6055@gmail.com
defender-ueuv.co.cc
defender-uqko.in - Email: christinakaaikati5574@gmail.com
defender-vflq.in - Email: terriacuna2081@gmail.com
defender-vlmj.in - Email: lauriefreeman9930@gmail.com
defender-vqqn.in - Email: chrisjames4421@gmail.com
defender-vxgh.in - Email: griseldavelez5369@gmail.com
defender-wkiw.in - Email: otisvaladez7778@gmail.com
defender-wqga.in - Email: christodoulosglidden8856@gmail.com
defender-wrhw.in - Email: bradsuresh1406@gmail.com
defender-wtln.co.cc
defender-xcre.in - Email: pavelmayer4891@gmail.com
defender-xnnx.in - Email: pavelmayer4891@gmail.com
defender-ykym.co.cc
movie-iirg.in - Email: misslynn8546@gmail.com
movie-pblv.in - Email: judgewright4021@gmail.com
movies-live-tube-jeyq.co.cc
movie-tkhk.in - Email: terrymeally1288@gmail.com
movie-tube-beym.co.cc
movie-tube-juie.co.cc
movie-ueep.in - Email: celinekevin6179@gmail.com
movieway2011.com - Email: contact@privacyprotect.org
movie-xbtb.in - Email: sanfordross9242@gmail.com
movie-xxnl.in - Email: ianbalitsaris3201@gmail.com
softway2011.com - Email: contact@privacyprotect.org
system-scanner-boep.co.cc
system-scanner-eill.co.cc
system-scanner-eopa.co.cc
system-scanner-ewqq.co.cc
system-scanner-iaap.co.cc
system-scanner-ieyx.co.cc
system-scanner-lcyo.co.cc
system-scanner-ouny.co.cc
system-scanner-oypx.co.cc
system-scanner-qeap.co.cc
system-scanner-racv.co.cc
system-scanner-ryes.co.cc
system-scanner-tzii.co.cc
system-scanner-uemo.co.cc
system-scanner-uotu.co.cc
system-scanner-uyxt.co.cc
system-scanner-vpoo.co.cc
system-scanner-xtoi.co.cc
system-scanner-yoyx.co.cc
system-scanner-ytut.co.cc
Rotated scareware domains involved in the campaign, responding to 84.123.115.228 (AS6739; ONO-AS Cableuropa - ONO):
defender-thga.in - Email: youngantonio6055@gmail.com
defender-wqga.in - Email: christodoulosglidden8856@gmail.com
defender-gnva.in - Email: ananddaher7294@gmail.com
defender-rlob.in - Email: vasikaranfreudenburg2690@gmail.com
defender-abcc.in - Email: rubysmart5057@gmail.com
defender-pakc.in - Email: sabrinawheelock7642@gmail.com
defender-keod.in - Email: khashayarbirss4814@gmail.com
defender-xcre.in - Email: pavelmayer4891@gmail.com
defender-qumf.in - Email: rachelalba1891@gmail.com
defender-fmof.in - Email: kamillamartin1237@gmail.com
defender-uvag.in - Email: espenkeck7682@gmail.com
defender-hsug.in - Email: moniquetkarnopp3596@gmail.com
defender-vxgh.in - Email: griseldavelez5369@gmail.com
defender-lcoh.in - Email: timothythomas6924@gmail.com
defender-kwwh.in - Email: tobyboisseau6505@gmail.com
defender-osbi.in - Email: fidelslattum2159@gmail.com
defender-wbui.in - Email: carlosbuntschu1238@gmail.com
defender-vlmj.in - Email: lauriefreeman9930@gmail.com
defender-hjlk.in - Email: lauriefreeman9930@gmail.com
defender-endl.in - Email: adamgaylard1113@gmail.com
defender-jgnl.in - Email: caseyalzen3316@gmail.com
defender-iksl.in - Email: marasanders9974@gmail.com
defender-labm.in - Email: gregorybradford1520@gmail.com
defender-rrin.in - Email: kevincharoenset5321@gmail.com
defender-sxin.in - Email: taloupavlinovich7166@gmail.com
defender-cron.in - Email: lisasuresh9147@gmail.com
defender-vqqn.in - Email: chrisjames4421@gmail.com
defender-dteo.in - Email: giovannaraggio5417@gmail.com
defender-uqko.in - Email: christinakaaikati5574@gmail.com
defender-qpwo.in - Email: carlaadams@gmail.com
defender-atxo.in - Email: celineiebba9266@gmail.com
defender-rlfp.in - Email: latanyamuscatell9507@gmail.com
defender-vflq.in - Email: terriacuna2081@gmail.com
defender-eklq.in - Email: sebastiensheppard8680@gmail.com
defender-ddbr.in - Email: selenajohansson9195@gmail.com
defender-ojbr.in - Email: fucknielsen8675@gmail.com
defender-drnr.in - Email: sumanvcasquez2008@gmail.com
defender-nrpr.in - Email: burtonalba8156@gmail.com
defender-kuts.in - Email: rogerfrancis3322@gmail.com
defender-bcvs.in - Email: martinefinklea5375@gmail.com
defender-grlt.in - Email: anthonygaylard9887@gmail.com
defender-hmfu.in - Email: lynnbone8026@gmail.com
defender-htlu.in - Email: jerihamann4163@gmail.com
defender-aabv.in - Email: leonflanagan7681@gmail.com
defender-ppdw.in - Email: divinakempton5670@gmail.com
defender-wrhw.in - Email: bradsuresh1406@gmail.com
defender-wkiw.in - Email: otisvaladez7778@gmail.com
defender-hipw.in - Email: angiejohansen9730@gmail.com
defender-qfdx.in - Email: hokyeongyancey6369@gmail.com
defender-xnnx.in - Email: sylviawulff2140@gmail.com
defender-xkox.in - Email: ryanmartin7607@gmail.com
The scareware domains have been registered using automatically registered email accounts at Gmail, as a precaution in an attempt to make it harder to expose the campaign by using a single email only.
Monitoring of the campaign is ongoing.
Related posts:
- SQL Injection Through Search Engines Reconnaissance
- Massive SQL Injections Through Search Engine's Reconnaissance - Part Two
- Massive SQL Injection Attacks - the Chinese Way
- Cybercriminals SQL Inject Cybercrime-friendly Proxies Service
- GoDaddy's Mass WordPress Blogs Compromise Serving Scareware
- Dissecting the WordPress Blogs Compromise at Network Solutions
- Yet Another Massive SQL Injection Spotted in the Wild
- Smells Like a Copycat SQL Injection In the Wild
- Fast-Fluxing SQL Injection Attacks
- Obfuscating Fast-fluxed SQL Injected Domains
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Dissecting the Massive SQL Injection Attack Serving Scareware
A currently ongoing massive SQL injection attack has affected hundreds of thousands of web pages across the Web, to ultimately monetize the campaign through a scareware affiliate program. Such massive SQL injection attempts are usually conducted using mass vulnerability scanning tools, with the help of search engines which have already crawled the vulnerable sites.
What's particularly interesting about this campaign, is the fact that the used domains are all responding to the same IPs, including the portfolios of scareware domains, which the cybercriminals naturally rotate on a periodic basis. Let's dissect the campaign, expose the domain portfolios and the entire campaign structure.
UPDATED: Related SQL injected URLs courtsesy of WebSense:
online-stats201.info/ur.php - Email: tik0066@gmail.com
stats-master111.info/ur.php - Email: tik0066@gmail.com
agasi-story.info/ur.php - 91.217.162.45 - Email: tik0066@gmail.com
general-st.info/ur.php - Email: tik0066@gmail.com
extra-service.info/ur.php - Email: tik0066@gmail.com
sol-stats.info/ur.php - Email: tik0066@gmail.com
google-stats49.info/ur.php - Email: tik0066@gmail.com
google-stats45.info/ur.php - Email: tik0066@gmail.com
google-stats50.info/ur.php - Email: tik0066@gmail.com
google-server43.info/ur.php - Email: tik0066@gmail.com
stats-master88.info/ur.php - Email: tik0066@gmail.com
eva-marine.info/ur.php - 109.236.81.28 - Email: tik0066@gmail.com
stats-master99.info/ur.php - Email: tik0066@gmail.com
tzv-stats.info/ur.php - Email: tik0066@gmail.com
milapop.com/ur.php - Email: jamesnorthone@hotmailbox.com
SQL injected URLs:
lizamoon.com/ur.php (67,500 results) - 91.220.35.151 (AS3721); 91.213.29.182 (AS51786); 95.64.9.18 (AS50244) - Email: jamesnorthone@hotmailbox.com
alexblane.com/ur.php (3,920 results) - Email: jamesnorthone@hotmailbox.com
alisa-carter.com/ur.php (220,000 results) - Email: jamesnorthone@hotmailbox.com
alexblane.com/ur.php (3,920 results) - Email: jamesnorthone@hotmailbox.com
t6ryt56.info/ur.php (18 results) - Email: support@ruler-domains.com
tadygus.com/ur.php (100 results) - Email: jamesnorthone@hotmailbox.com
worid-of-books.com/ur.php (334,000 results) - Email: tik0066@gmail.com
Upon successful redirection, the campaign attempts to load the scareware domains defender-nibea.in/scan1b/237 - 46.252.130.200 - Email: jimwei2969@gmail.com
Detection rate:
freesystemscan.exe - Trojan/Win32.FakeAV - Result: 9/ 41 (22.0%)
MD5 : 815d77f8fca509dde1abeafabed30b65
SHA1 : 1b3c35afb76c53cd9507fffee46fb58c29e72bc1
SHA256: cd902b92042435c2d70d4bf59acc2de8229bfc367626961f76c03f75dcd7e95c
antivirus-1091.co.cc
antivirus-1574.co.cc
antivirus-2051.co.cc
antivirus-2525.co.cc
antivirus-2932.co.cc
antivirus-3654.co.cc
antivirus-3833.co.cc
antivirus-4063.co.cc
antivirus-418.co.cc
antivirus-4303.co.cc
antivirus-4749.co.cc
antivirus-495.co.cc
antivirus-5216.co.cc
antivirus-5676.co.cc
antivirus-5802.co.cc
antivirus-6437.co.cc
antivirus-6703.co.cc
antivirus-7081.co.cc
antivirus-713.co.cc
antivirus-728.co.cc
antivirus-7357.co.cc
antivirus-8072.co.cc
antivirus-9009.co.cc
antivirus-9638.co.cc
antivirus-9667.co.cc
defender-aabv.in - Email: leonflanagan7681@gmail.com
defender-aqeu.co.cc
defender-asng.co.cc
defender-atio.in - Email: terriduverger3239@gmail.com
defender-atxo.in - Email: celineiebba9266@gmail.com
defender-bcvs.in - Email: martinefinklea5375@gmail.com
defender-bwuy.co.cc
defender-cron.in - Email: lisasuresh9147@gmail.com
defender-ddbr.in - Email: selenajohansson9195@gmail.com
defender-dteo.in - Email: giovannaraggio5417@gmail.com
defender-eahy.co.cc
defender-eklq.in - Email: sebastiensheppard8680@gmail.com
defender-endl.in - Email: adamgaylard1113@gmail.com
defender-ewum.co.cc
defender-eyde.co.cc
defender-fmof.in - Email: kamillamartin1237@gmail.com
defender-fola.co.cc
defender-gnva.in - Email: ananddaher7294@gmail.com
defender-grlt.in - Email: anthonygaylard9887@gmail.com
defender-hipw.in - Email: angiejohansen9730@gmail.com
defender-hjlk.in - Email: jennwrayford2124@gmail.com
defender-hmfu.in - Email: lynnbone8026@gmail.com
defender-hsug.in - Email: moniquetkarnopp3596@gmail.com
defender-htlu.in - Email: jerihamann4163@gmail.com
defender-iibk.co.cc
defender-iies.co.cc
defender-iksl.in - Email: amarasanders9974@gmail.com
defender-isde.co.cc
defender-iyrc.co.cc
defender-jgnl.in - Email: caseyalzen3316@gmail.com
defender-jihv.co.cc
defender-keod.in - Email: khashayarbirss4814@gmail.com
defender-kuts.in - Email: rogerfrancis3322@gmail.com
defender-kwwh.in - Email: tobyboisseau6505@gmail.com
defender-kzwu.co.cc
defender-labm.in - Email: gregorybradford1520@gmail.com
defender-lcoh.in - Email: timothythomas6924@gmail.com
defender-nhei.co.cc
defender-nrpr.in - Email: burtonalba8156@gmail.com
defender-ojbr.in - Email: fucknielsen8675@gmail.com
defender-osbi.in - Email: fidelslattum2159@gmail.com
defender-pakc.in - Email: sabrinawheelock7642@gmail.com
defender-ppdw.in - Email: divinakempton5670@gmail.com
defender-qfdx.in - Email: hokyeongyancey6369@gmail.com
defender-qotg.in - Email: franchescaili9704@gmail.com
defender-qpwo.in - Email: carlaadams@gmail.com
defender-qsko.co.cc
defender-qumf.in - Email: carlaadams@gmail.com
defender-rlag.in - Email: carmichaelmail@gmail.com
defender-rrin.in - Email: kevincharoenset5321@gmail.com
defender-thga.in - Email: youngantonio6055@gmail.com
defender-ueuv.co.cc
defender-uqko.in - Email: christinakaaikati5574@gmail.com
defender-vflq.in - Email: terriacuna2081@gmail.com
defender-vlmj.in - Email: lauriefreeman9930@gmail.com
defender-vqqn.in - Email: chrisjames4421@gmail.com
defender-vxgh.in - Email: griseldavelez5369@gmail.com
defender-wkiw.in - Email: otisvaladez7778@gmail.com
defender-wqga.in - Email: christodoulosglidden8856@gmail.com
defender-wrhw.in - Email: bradsuresh1406@gmail.com
defender-wtln.co.cc
defender-xcre.in - Email: pavelmayer4891@gmail.com
defender-xnnx.in - Email: pavelmayer4891@gmail.com
defender-ykym.co.cc
movie-iirg.in - Email: misslynn8546@gmail.com
movie-pblv.in - Email: judgewright4021@gmail.com
movies-live-tube-jeyq.co.cc
movie-tkhk.in - Email: terrymeally1288@gmail.com
movie-tube-beym.co.cc
movie-tube-juie.co.cc
movie-ueep.in - Email: celinekevin6179@gmail.com
movieway2011.com - Email: contact@privacyprotect.org
movie-xbtb.in - Email: sanfordross9242@gmail.com
movie-xxnl.in - Email: ianbalitsaris3201@gmail.com
softway2011.com - Email: contact@privacyprotect.org
system-scanner-boep.co.cc
system-scanner-eill.co.cc
system-scanner-eopa.co.cc
system-scanner-ewqq.co.cc
system-scanner-iaap.co.cc
system-scanner-ieyx.co.cc
system-scanner-lcyo.co.cc
system-scanner-ouny.co.cc
system-scanner-oypx.co.cc
system-scanner-qeap.co.cc
system-scanner-racv.co.cc
system-scanner-ryes.co.cc
system-scanner-tzii.co.cc
system-scanner-uemo.co.cc
system-scanner-uotu.co.cc
system-scanner-uyxt.co.cc
system-scanner-vpoo.co.cc
system-scanner-xtoi.co.cc
system-scanner-yoyx.co.cc
system-scanner-ytut.co.cc
Rotated scareware domains involved in the campaign, responding to 84.123.115.228 (AS6739; ONO-AS Cableuropa - ONO):
defender-thga.in - Email: youngantonio6055@gmail.com
defender-wqga.in - Email: christodoulosglidden8856@gmail.com
defender-gnva.in - Email: ananddaher7294@gmail.com
defender-rlob.in - Email: vasikaranfreudenburg2690@gmail.com
defender-abcc.in - Email: rubysmart5057@gmail.com
defender-pakc.in - Email: sabrinawheelock7642@gmail.com
defender-keod.in - Email: khashayarbirss4814@gmail.com
defender-xcre.in - Email: pavelmayer4891@gmail.com
defender-qumf.in - Email: rachelalba1891@gmail.com
defender-fmof.in - Email: kamillamartin1237@gmail.com
defender-uvag.in - Email: espenkeck7682@gmail.com
defender-hsug.in - Email: moniquetkarnopp3596@gmail.com
defender-vxgh.in - Email: griseldavelez5369@gmail.com
defender-lcoh.in - Email: timothythomas6924@gmail.com
defender-kwwh.in - Email: tobyboisseau6505@gmail.com
defender-osbi.in - Email: fidelslattum2159@gmail.com
defender-wbui.in - Email: carlosbuntschu1238@gmail.com
defender-vlmj.in - Email: lauriefreeman9930@gmail.com
defender-hjlk.in - Email: lauriefreeman9930@gmail.com
defender-endl.in - Email: adamgaylard1113@gmail.com
defender-jgnl.in - Email: caseyalzen3316@gmail.com
defender-iksl.in - Email: marasanders9974@gmail.com
defender-labm.in - Email: gregorybradford1520@gmail.com
defender-rrin.in - Email: kevincharoenset5321@gmail.com
defender-sxin.in - Email: taloupavlinovich7166@gmail.com
defender-cron.in - Email: lisasuresh9147@gmail.com
defender-vqqn.in - Email: chrisjames4421@gmail.com
defender-dteo.in - Email: giovannaraggio5417@gmail.com
defender-uqko.in - Email: christinakaaikati5574@gmail.com
defender-qpwo.in - Email: carlaadams@gmail.com
defender-atxo.in - Email: celineiebba9266@gmail.com
defender-rlfp.in - Email: latanyamuscatell9507@gmail.com
defender-vflq.in - Email: terriacuna2081@gmail.com
defender-eklq.in - Email: sebastiensheppard8680@gmail.com
defender-ddbr.in - Email: selenajohansson9195@gmail.com
defender-ojbr.in - Email: fucknielsen8675@gmail.com
defender-drnr.in - Email: sumanvcasquez2008@gmail.com
defender-nrpr.in - Email: burtonalba8156@gmail.com
defender-kuts.in - Email: rogerfrancis3322@gmail.com
defender-bcvs.in - Email: martinefinklea5375@gmail.com
defender-grlt.in - Email: anthonygaylard9887@gmail.com
defender-hmfu.in - Email: lynnbone8026@gmail.com
defender-htlu.in - Email: jerihamann4163@gmail.com
defender-aabv.in - Email: leonflanagan7681@gmail.com
defender-ppdw.in - Email: divinakempton5670@gmail.com
defender-wrhw.in - Email: bradsuresh1406@gmail.com
defender-wkiw.in - Email: otisvaladez7778@gmail.com
defender-hipw.in - Email: angiejohansen9730@gmail.com
defender-qfdx.in - Email: hokyeongyancey6369@gmail.com
defender-xnnx.in - Email: sylviawulff2140@gmail.com
defender-xkox.in - Email: ryanmartin7607@gmail.com
The scareware domains have been registered using automatically registered email accounts at Gmail, as a precaution in an attempt to make it harder to expose the campaign by using a single email only.
Monitoring of the campaign is ongoing.
Related posts:
- SQL Injection Through Search Engines Reconnaissance
- Massive SQL Injections Through Search Engine's Reconnaissance - Part Two
- Massive SQL Injection Attacks - the Chinese Way
- Cybercriminals SQL Inject Cybercrime-friendly Proxies Service
- GoDaddy's Mass WordPress Blogs Compromise Serving Scareware
- Dissecting the WordPress Blogs Compromise at Network Solutions
- Yet Another Massive SQL Injection Spotted in the Wild
- Smells Like a Copycat SQL Injection In the Wild
- Fast-Fluxing SQL Injection Attacks
- Obfuscating Fast-fluxed SQL Injected Domains
Tags:
Blackhat SEO,
Cybercrime,
Fake Security Software,
Hacking,
Information Security,
Scareware,
Search Engine Optimization,
Security,
SQL Injection
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Friday, March 25, 2011
Spamvertised Post Office Express Mail (USPS) Emails Serving Malware
A currently spamvertised malware campaign is impersonating the USPS for malware-serving purposes.
Sample subject: Post Express Information. Your package is available for pick up. NR[random number]
Sample attachment: Post_Express_Label_ID_[random number].zip; Post_Express_Label.exe
Sample message:
Dear client, Email notice number.[random number]. Your package has been returned to the Post Express office. The reason of the return is "Error in the delivery address" Important message! Attached to the letter mailing label contains the details of the package delivery. You have to print mailing label, and come in the Post Express office in order to receive the packages! Thank you for using our services. Post Express Support.
Detection rate:
Post_Express_Label.exe - Medium Risk Malware Dropper - Result: 1/ 41 (2.4%)
MD5 : 3c05dd68ee0bfb9b290b9c034f836833
SHA1 : 8a1a00da04c96c8e67b9921652de60463118ea9f
SHA256: 57d58165c79158a42c3e45670aa4176aaae393f371188f91d0ac46022bd3e7c0
Upon execution phones back to:
mialepromo.ru/7Pe8ORoIxs/document.doc
mialepromo.ru/7Pe8ORoIxs/load.php?file=0
mialepromo.ru/7Pe8ORoIxs/load.php?file=1
mialepromo.ru/7Pe8ORoIxs/load.php?file=2
mialepromo.ru/7Pe8ORoIxs/load.php?file=3
mialepromo.ru/7Pe8ORoIxs/load.php?file=4
mialepromo.ru/7Pe8ORoIxs/load.php?file=5
mialepromo.ru/7Pe8ORoIxs/load.php?file=6
mialepromo.ru/7Pe8ORoIxs/load.php?file=7
mialepromo.ru/7Pe8ORoIxs/load.php?file=8
mialepromo.ru/7Pe8ORoIxs/load.php?file=9
mialepromo.ru/7Pe8ORoIxs/load.php?file=uploader
mialepromo.ru/7Pe8ORoIxs/load.php?file=grabbers
mialepromo.ru - 89.208.149.204 (AS12695); 109.94.220.51 (AS47860); 109.94.220.50 (AS47860); 91.199.75.77 (AS44301) 178.17.164.131 (AS43289) 193.22.81.104 (AS28920) - Email: salam@ica.org
Monitoring of the campaign is ongoing.
Related posts:
Spamvertised United Parcel Service notifications serve malware
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
This post has been reproduced from Dancho Danchev's blog.
Sample subject: Post Express Information. Your package is available for pick up. NR[random number]
Sample attachment: Post_Express_Label_ID_[random number].zip; Post_Express_Label.exe
Sample message:
Dear client, Email notice number.[random number]. Your package has been returned to the Post Express office. The reason of the return is "Error in the delivery address" Important message! Attached to the letter mailing label contains the details of the package delivery. You have to print mailing label, and come in the Post Express office in order to receive the packages! Thank you for using our services. Post Express Support.
Detection rate:
Post_Express_Label.exe - Medium Risk Malware Dropper - Result: 1/ 41 (2.4%)
MD5 : 3c05dd68ee0bfb9b290b9c034f836833
SHA1 : 8a1a00da04c96c8e67b9921652de60463118ea9f
SHA256: 57d58165c79158a42c3e45670aa4176aaae393f371188f91d0ac46022bd3e7c0
Upon execution phones back to:
mialepromo.ru/7Pe8ORoIxs/document.doc
mialepromo.ru/7Pe8ORoIxs/load.php?file=0
mialepromo.ru/7Pe8ORoIxs/load.php?file=1
mialepromo.ru/7Pe8ORoIxs/load.php?file=2
mialepromo.ru/7Pe8ORoIxs/load.php?file=3
mialepromo.ru/7Pe8ORoIxs/load.php?file=4
mialepromo.ru/7Pe8ORoIxs/load.php?file=5
mialepromo.ru/7Pe8ORoIxs/load.php?file=6
mialepromo.ru/7Pe8ORoIxs/load.php?file=7
mialepromo.ru/7Pe8ORoIxs/load.php?file=8
mialepromo.ru/7Pe8ORoIxs/load.php?file=9
mialepromo.ru/7Pe8ORoIxs/load.php?file=uploader
mialepromo.ru/7Pe8ORoIxs/load.php?file=grabbers
mialepromo.ru - 89.208.149.204 (AS12695); 109.94.220.51 (AS47860); 109.94.220.50 (AS47860); 91.199.75.77 (AS44301) 178.17.164.131 (AS43289) 193.22.81.104 (AS28920) - Email: salam@ica.org
Monitoring of the campaign is ongoing.
Related posts:
Spamvertised United Parcel Service notifications serve malware
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Wednesday, March 23, 2011
Spamvertised United Parcel Service notifications serve malware
A currently ongoing spam campaign is impersonating UPS for malware-serving purposes.
Sample subject: United Parcel Service notification
Sample attachments: UPSnotify.rar; UPSnotify.exe; UnitedParcelServicedocument.exe
Sample message: Dear customer.
The parcel was sent your home address. And it will arrive within 7 business day. More information and the tracking number are attached in document below. Thank you. © 1994-2011 United Parcel Service of America, Inc.
Detection rates:
UnitedParcelServicedocument.exe - Mal/Bredo-K - Result: 7/ 41 (17.1%)
MD5 : b60e95b42106989bc39e175efcc031db
SHA1 : 0fb63dff83db643c9ee42efe617bdd539a5ffb8f
SHA256: 65f14438c3154a74767131a427fbdc50c28a6cbcdcf47f3d418b92c4c168696a
UPS notify.exe - Mal/Bredo-K - Result: 17/ 40 (42.5%)
MD5 : cc040e69121bc19f23ef4a32dbb8a80e
SHA1 : da65b7b277540b88918076949a28e8307ad7e41a
SHA256: ef5f76e1b20c2083469fbe7e4de4ec9c06689ee105274b1a79c9cadbd23d54ae
Upon execution downloads additional binaries from:
193.105.121.33/lol2.exe
193.105.121.33/pod.exe
193.105.121.33/spm.exe
Responding to 193.105.121.33 are undeardarling.com - Email: admin@undearhappydear.com and undearhappydear.com - Email: admin@undearhappydear.com
Detection rates:
lol2.exe - Trojan.FakeAV!gen39- Result: 14/ 43 (32.6%)
MD5 : 747431a2a4a29f1bfc136e674af99ad0
SHA1 : 8349fc3f5f299d0ca6473e748276ec2b50019330
SHA256: 6009e7f5cbc55e6acb060d9fb33a39a978168a32a0a8c6a24f201106056cc0db
pod.exe - Backdoor.Win32.Gbot!IK - Result: 33/ 42 (78.6%)
MD5 : f403afdbe4c4c859c8ab018a7ded694c
SHA1 : 1915a46cbb43fcaf8da90af95856d7524b24f129
SHA256: eddfff99df316669191be0b61a5ae06ee811bbd27110111e69cbd212881fa494
Upon execution phones back to:
healthylifenow.com - 208.109.223.193 - Email: HEALTHYLIFENOW.COM@domainsbyproxy.com
bigbeerclubonline.com - Email: contact@privacyprotect.org
zonetf.com - 96.9.169.85 - Email: janeob@126.com
spm.exe - W32.Pilleuz - 10/ 42 (23.8%)
MD5 : de55498b9f9195f1733df62c7026cf5f
SHA1 : 5520c1220cdd03a64f9b782c2393697ebab154b9
SHA256: dc2a797e5be968f9d36d4510988fa242c042a3e315fb50a3f9325cae6a1d779d
Upon execution phones back to:
ponel.biz - 46.4.62.17 - Email: web_raskrutka@pochta.ru
itisformebaby.biz - 46.4.10.7; 88.198.46.151; 178.63.63.208 - Email: web_raskrutka@pochta.ru
gmail.com
yahoo.com
hotmail.com
As speculated, cybercriminals have started feeding legitimate sites into their C&C communication patterns in an attempt to undermine community efforts aimed at tracking their malicious activities.
Related posts:
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
This post has been reproduced from Dancho Danchev's blog.
Sample subject: United Parcel Service notification
Sample attachments: UPSnotify.rar; UPSnotify.exe; UnitedParcelServicedocument.exe
Sample message: Dear customer.
The parcel was sent your home address. And it will arrive within 7 business day. More information and the tracking number are attached in document below. Thank you. © 1994-2011 United Parcel Service of America, Inc.
Detection rates:
UnitedParcelServicedocument.exe - Mal/Bredo-K - Result: 7/ 41 (17.1%)
MD5 : b60e95b42106989bc39e175efcc031db
SHA1 : 0fb63dff83db643c9ee42efe617bdd539a5ffb8f
SHA256: 65f14438c3154a74767131a427fbdc50c28a6cbcdcf47f3d418b92c4c168696a
UPS notify.exe - Mal/Bredo-K - Result: 17/ 40 (42.5%)
MD5 : cc040e69121bc19f23ef4a32dbb8a80e
SHA1 : da65b7b277540b88918076949a28e8307ad7e41a
SHA256: ef5f76e1b20c2083469fbe7e4de4ec9c06689ee105274b1a79c9cadbd23d54ae
Upon execution downloads additional binaries from:
193.105.121.33/lol2.exe
193.105.121.33/pod.exe
193.105.121.33/spm.exe
Responding to 193.105.121.33 are undeardarling.com - Email: admin@undearhappydear.com and undearhappydear.com - Email: admin@undearhappydear.com
Detection rates:
lol2.exe - Trojan.FakeAV!gen39- Result: 14/ 43 (32.6%)
MD5 : 747431a2a4a29f1bfc136e674af99ad0
SHA1 : 8349fc3f5f299d0ca6473e748276ec2b50019330
SHA256: 6009e7f5cbc55e6acb060d9fb33a39a978168a32a0a8c6a24f201106056cc0db
pod.exe - Backdoor.Win32.Gbot!IK - Result: 33/ 42 (78.6%)
MD5 : f403afdbe4c4c859c8ab018a7ded694c
SHA1 : 1915a46cbb43fcaf8da90af95856d7524b24f129
SHA256: eddfff99df316669191be0b61a5ae06ee811bbd27110111e69cbd212881fa494
Upon execution phones back to:
healthylifenow.com - 208.109.223.193 - Email: HEALTHYLIFENOW.COM@domainsbyproxy.com
bigbeerclubonline.com - Email: contact@privacyprotect.org
zonetf.com - 96.9.169.85 - Email: janeob@126.com
spm.exe - W32.Pilleuz - 10/ 42 (23.8%)
MD5 : de55498b9f9195f1733df62c7026cf5f
SHA1 : 5520c1220cdd03a64f9b782c2393697ebab154b9
SHA256: dc2a797e5be968f9d36d4510988fa242c042a3e315fb50a3f9325cae6a1d779d
Upon execution phones back to:
ponel.biz - 46.4.62.17 - Email: web_raskrutka@pochta.ru
itisformebaby.biz - 46.4.10.7; 88.198.46.151; 178.63.63.208 - Email: web_raskrutka@pochta.ru
gmail.com
yahoo.com
hotmail.com
As speculated, cybercriminals have started feeding legitimate sites into their C&C communication patterns in an attempt to undermine community efforts aimed at tracking their malicious activities.
Related posts:
Spamvertised FedEx Notifications Spread Malware
Spamvertised DHL Notification Malware Campaign
More Spamvertised DHL Notifications Spread Malware
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Wednesday, March 16, 2011
Compromised Universities Leads to Fraudulent Pharmaceutical Ads
Continuing the "Compromised University Leads to Fraudulent Pharmaceutical Ads"; "Compromised University Leads to Fraudulent Google Brand-jacked Pharmaceutical Ads" series, in this post we'll discuss two more compromised web servers of educational institutions leading to pharmaceutical ads. Affected Universities are:
Rutgets Energy Institute:
ruei.rutgers.edu/documents/chin.php?adv=cialis20-mg
ruei.rutgers.edu/documents/chin.php?adv=viagra-ratings
ruei.rutgers.edu/documents/chin.php?adv=viagra-999
ruei.rutgers.edu/documents/chin.php?adv=viagra-expired
ruei.rutgers.edu/documents/chin.php?adv=viagra-kako-se
Uploaded redirectors:
ruei.rutgers.edu/documents/chin.php
ruei.rutgers.edu/documents/roar.php
ruei.rutgers.edu/documents/ost.php
Computer Music Center at Columbia University
music.columbia.edu/cmc/pills/index.php?adv=how-to-try-viagra
music.columbia.edu/cmc/pills/index.php?adv=damaskviagra
music.columbia.edu/cmc/pills/index.php?adv=brandlevitra
music.columbia.edu/cmc/pills/index.php?adv=vegetalviagra
music.columbia.edu/cmc/pills/index.php?adv=vviagra
The sampled URLs redirect to the following fraudulent pharmaceutical sites:
pillsedonline.com - 93.170.104.53 - Email: stavros1929@hotmail.com; stavroscomodromos@yahoo.com
buyperfecthealth.com - 93.170.104.53 - Email: stavros1929@hotmail.com
safedrugstock.com - 93.170.104.53 - Email: stavros1929@hotmail.com
securedrugstock.com - 93.170.104.53 - Email: stavros1929@hotmail.com
europharmas.com - 93.170.104.53 - Email: glockner546@hotmail.com
requestpills.com - 93.170.104.53 - Email: stavros1929@hotmail.com; stavroscomodromos@yahoo.com
online-doc.us - 93.170.104.53 - Email: cool_gamer90@mail.ru
pills4sex.eu - 93.170.104.53
securetablets.com - 93.170.104.53 - Email: stavros1929@hotmail.com
alledtablets.com - 93.170.104.53 - Email: stavros1929@hotmail.com; stavroscomodromos@yahoo.com
canadian-refills.com - 178.239.60.214 - Email: privacy-829911@domainprivacygroup.com
Cybercriminals continue purchasing web shells/and stolen FTP credentials to high page rank-ed web sites such as educational institutions. Monitoring of their operations will continue.
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Spamvertised FedEx Notifications Spread Malware
A currently ongoing spamvertised campaign is brand-jacking FedEx for malware serving purposes.
Sample attachments: FedEx letter.zip; FedEx letter.exe
Sample subject: FedEx notification #random number
Sample message: Dear customer. The parcel was sent your home address. And it will arrive within 7 business day. More information and the tracking number are attached in document below.
Thank you.
© FedEx 1995-2011
Detection rate: FedEx letter.exe - Trojan.FakeAV - Result: 24/ 43 (55.8%)
MD5 : 90bef5dff5809682249813fd63b67da4
SHA1 : 2418c01a30a19a2d76b693474a852092e3de4a32
SHA256: a38848786528d235b51fed3adf20050f5c1906d066e0282311b8bce37d8163a0
Phones back to AS30890 (EVOLVA Evolva Telecom s.r.l.)
94.63.244.56/lol2.exe
94.63.244.56/pod.exe
with 94.63.244.56/allftp.txt; 94.63.244.56/ftp/db_grab.txt hosting the sniffed FTP credentials.
Responding to 94.63.244.56 are d34ghqarfrgad.com and erherg34gsafwe.com, phone back URLs which we've seen from last week's spamvertised DHL Notifications campaigns, with the use of the IP best described as a desperate attempt to maintain a C&C infrastructure:
This post has been reproduced from Dancho Danchev's blog.
Sample attachments: FedEx letter.zip; FedEx letter.exe
Sample subject: FedEx notification #random number
Sample message: Dear customer. The parcel was sent your home address. And it will arrive within 7 business day. More information and the tracking number are attached in document below.
Thank you.
© FedEx 1995-2011
Detection rate: FedEx letter.exe - Trojan.FakeAV - Result: 24/ 43 (55.8%)
MD5 : 90bef5dff5809682249813fd63b67da4
SHA1 : 2418c01a30a19a2d76b693474a852092e3de4a32
SHA256: a38848786528d235b51fed3adf20050f5c1906d066e0282311b8bce37d8163a0
Phones back to AS30890 (EVOLVA Evolva Telecom s.r.l.)
94.63.244.56/lol2.exe
94.63.244.56/pod.exe
with 94.63.244.56/allftp.txt; 94.63.244.56/ftp/db_grab.txt hosting the sniffed FTP credentials.
Responding to 94.63.244.56 are d34ghqarfrgad.com and erherg34gsafwe.com, phone back URLs which we've seen from last week's spamvertised DHL Notifications campaigns, with the use of the IP best described as a desperate attempt to maintain a C&C infrastructure:
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Friday, March 11, 2011
More Spamvertised DHL Notifications Spread Malware
Yesterday's campaign is still ongoing, with new MD5's in the wild. Here are the details.
Sample subjects: DHL notification #random number
Sample message: Dear customer! The parcel was send your home address. And it will arrice within 7 bussness day. More information and the tracking number are attached in document below. Thank you. 2011 DHL International GmbH. All rights reserverd.
Sample filenames: DHL_tracking.zip; doc.zip
doc.exe - Trojan-Spy.SpyEy!IK - Result: 18/ 43 (41.9%)
MD5: 83db662187dd7cd58fc4a368ea27775d
SHA1 : 4edb2d95c0570a36f6cb992e55111cdd7c3eda69
SHA256: 99f1e003bbf1025b0bbe257ece65d1704852fd1ba48e6cc79bd39cde6e6d14c3
DHL_tracking.exe - Win-Trojan/Spyeyes.45568 - Result: 29/ 43 (67.4%)
MD5 : 81fc09b014617bce59f678374b486512
SHA1 : 3d92a768f58b2900b98c9f97ce2753d27a4749ae
SHA256: 24b23bf7ebd03bf5feb0c637ea1e64661e27c78c66684dd49f074af2b2505bb7
Upon execution phones back to:
adobe.com/geo/productid.php
elsoplongt.com/rk`,jopbh/qwq - Email: redaccion@elsoplongt.com
accuratefiles.com/rk`,jopbh/qwq
lulango.com/rk`,jopbh/qwq - Email: lulango@gmail.com
erherg34gsafwe.com/xgate.php - AS49469, Email: admin@erherg34gsafwe.com
- erherg34gsafwe.com/ftp/base.bin
- erherg34gsafwe.com/ftp/ftpplug2.dll
- erherg34gsafwe.com/ftp/base.bin
Domains responding to:
192.150.16.117
72.41.115.170
74.117.180.216
87.106.193.21
94.63.244.56
Additional malicious activity within AS49469 (SA-NOVA-TELECOM-GRUP-SRL Sa Nova Telecom Grup SRL, courtesy of the ZeusTracker and the SpyEye Tracker:
bigupdate.ru - Email: admin@hotupdaters.ru
bigupdatings.ru - Email: admin@bigupdatings.ru
bigupdater.ru - Email: admin@bigupdater.ru
bigupdates.ru - Email: admin@istuplenie.ru
bigupdating.ru - Email: admin@bigupdating.ru
bigupdaters.ru - Email: admin@bigupdaters.ru
94.63.244.30
metamphcrystal.com - Email: admin@metamphcrystal.com
Related malware-serving domains within AS49469, SA-NOVA-TELECOM-GRUP-SRL Sa Nova Telecom Grup SRL
xppclapgirl.com - 89.114.9.33
natnatraoi.com - 12.211.117.127 - Email: barbarasorber@yahoo.com
d34ghqarfrgad.com - 94.63.244.56 - Email: admin@d34ghqarfrgad.com
g3u4g.net - 89.114.9.33 - Email: G3U4G.NET@domainservice.com
suhi4hr.net - 89.114.9.60 - Email: SUHI4HR.NET@domainservice.com
mialedot.ru - 94.63.244.44 - Email: abuse@mialedot.ru
blackmemoso.com - Email: grasp@yourisp.ru
This post has been reproduced from Dancho Danchev's blog.
Sample subjects: DHL notification #random number
Sample message: Dear customer! The parcel was send your home address. And it will arrice within 7 bussness day. More information and the tracking number are attached in document below. Thank you. 2011 DHL International GmbH. All rights reserverd.
Sample filenames: DHL_tracking.zip; doc.zip
doc.exe - Trojan-Spy.SpyEy!IK - Result: 18/ 43 (41.9%)
MD5: 83db662187dd7cd58fc4a368ea27775d
SHA1 : 4edb2d95c0570a36f6cb992e55111cdd7c3eda69
SHA256: 99f1e003bbf1025b0bbe257ece65d1704852fd1ba48e6cc79bd39cde6e6d14c3
DHL_tracking.exe - Win-Trojan/Spyeyes.45568 - Result: 29/ 43 (67.4%)
MD5 : 81fc09b014617bce59f678374b486512
SHA1 : 3d92a768f58b2900b98c9f97ce2753d27a4749ae
SHA256: 24b23bf7ebd03bf5feb0c637ea1e64661e27c78c66684dd49f074af2b2505bb7
Upon execution phones back to:
adobe.com/geo/productid.php
elsoplongt.com/rk`,jopbh/qwq - Email: redaccion@elsoplongt.com
accuratefiles.com/rk`,jopbh/qwq
lulango.com/rk`,jopbh/qwq - Email: lulango@gmail.com
erherg34gsafwe.com/xgate.php - AS49469, Email: admin@erherg34gsafwe.com
- erherg34gsafwe.com/ftp/base.bin
- erherg34gsafwe.com/ftp/ftpplug2.dll
- erherg34gsafwe.com/ftp/base.bin
Domains responding to:
192.150.16.117
72.41.115.170
74.117.180.216
87.106.193.21
94.63.244.56
Additional malicious activity within AS49469 (SA-NOVA-TELECOM-GRUP-SRL Sa Nova Telecom Grup SRL, courtesy of the ZeusTracker and the SpyEye Tracker:
bigupdate.ru - Email: admin@hotupdaters.ru
bigupdatings.ru - Email: admin@bigupdatings.ru
bigupdater.ru - Email: admin@bigupdater.ru
bigupdates.ru - Email: admin@istuplenie.ru
bigupdating.ru - Email: admin@bigupdating.ru
bigupdaters.ru - Email: admin@bigupdaters.ru
94.63.244.30
metamphcrystal.com - Email: admin@metamphcrystal.com
Related malware-serving domains within AS49469, SA-NOVA-TELECOM-GRUP-SRL Sa Nova Telecom Grup SRL
xppclapgirl.com - 89.114.9.33
natnatraoi.com - 12.211.117.127 - Email: barbarasorber@yahoo.com
d34ghqarfrgad.com - 94.63.244.56 - Email: admin@d34ghqarfrgad.com
g3u4g.net - 89.114.9.33 - Email: G3U4G.NET@domainservice.com
suhi4hr.net - 89.114.9.60 - Email: SUHI4HR.NET@domainservice.com
mialedot.ru - 94.63.244.44 - Email: abuse@mialedot.ru
blackmemoso.com - Email: grasp@yourisp.ru
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Subscribe to:
Posts (Atom)