In the overwhelming sea of information, access to timely, insightful and independent open-source intelligence (OSINT) analyses is crucial for maintaining the necessary situational awareness to stay on the top of emerging security threats. This blog covers trends and fads, tactics and strategies, intersecting with third-party research, speculations and real-time CYBERINT assessments, all packed with sarcastic attitude
Tuesday, October 04, 2011
Summarizing ZDNet's Zero Day Posts for September
The following is a brief summary of all of my posts at ZDNet's Zero Day for September. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
01. Spamvertised 'Facebook notification' leads to exploits and malware
02. Google, Mozilla and Microsoft ban the DigiNotar Certificate Authority in their browsers
03. Microsoft themed ransomware variant spotted in the wild
04. 'Man in wheelchair falls down the elevator shaft' scam spreading on Facebook
05. New ransomware variant uses false child porn accusations
06. Russian Embassy in London hit by a DDoS attack
07. uTorrent.com hacked, serving scareware
08. Bank of Melbourne Twitter account hacked, spreading phishing links
09. Malicious spam campaigns proliferating
10. Spamvertised 'We are going to sue you' emails lead to malware
11. XSS bug in Skype for iPhone, iPad allows address book theft
12. Researcher releases details on 6 SCADA vulnerabilities
13. DIY botnet kit spotted in the wild
14. New Mac OS X trojan poses as malicious PDF file
15. Survey: 60 percent of users use the same password across more than one of their online accounts
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Wednesday, September 28, 2011
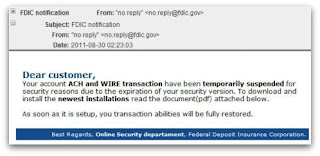
Spamvertised 'Uniform Traffic Ticket' and 'FDIC Notifications' Serving Malware - Historical OSINT
The following intelligence brief will summarize the findings from a brief analysis performed on two malware campaigns from August, namely, the spamvertised Uniform Traffic Tickets and the FDIC Notification.
_Uniform Traffic Tickets
Spamvertised attachments - Ticket-728-2011.zip; Ticket-064-211.zip; Ticket-728-2011.zip
Detection rates:
Ticket.exe - Gen:Trojan.Heur.FU.bqW@aK9ebrii - Detection rate: 37/43 (86.0%)
MD5 : 6361d4a40485345c18473f3c6b4b6609
SHA1 : 50b09bb2e0044aa139a84c2e445a56f01d70c185
SHA256: ca67a14bfed2a7bc2ac8be9c01cb17d5da12b75320b4bad4fe8d8a6759ad9725
Ticket1.exe - Trojan-Downloader.Win32.Small.ccxz - Detection rate: 36/44 (81.8%)
MD5 : e2a2d67b8a52ae655f92779bec296676
SHA1 : ed3df72b4e073ffba7174ebc8cb77b2b7d012cbf
SHA256: 50b104c5f8314327e03b01e7f7c2535d8de7cd9f73f8e16d1364c7fd021a90cc
Upon execution the samples phone back to:
sdkjgndfjnf.ru/pusk3.exe - 91.220.0.55 (responding to the same IP is also survey-providers.info) - AS51630 - Email: admin@sdkjgndfjnf.ru
rattsillis.com/ftp/g.php - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
rattsillis.com/pusk3.exe - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
DNS emulation of ns1.lemanbrostm.info reveals two domains belidiskalom.com - 178.208.76.175 - Email: admin@belidiskalom.com and lemanbrostm.info - Email: coz@yahoo.com using the same name server.
Known MD5 modifications for pusk3.exe at rattsillis.com:
c6dab856705b5dfd09b2adbe10701b05
f167213c6a79f2313995e80a8ac29939
f4764cce5c3795b1d63a299a5329d2e2
dae9e7653573478a6b41a62f7cb99c12
69c983c9dfaf37e346004c9aaf54a3d0
d875b8e32a231405c7fa96b810e9b361
628270c6e44b0fa21ef8e87c6bc36f57
9b69dabd876e967bcd2eb85465175e3b
0434c084dba8626df980c7974d5728e1
Related binaries and associated MD5 modifications:
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
rattsillis.com/pusk.exe - MD5: 55d8e25bc373a98c5c29284c989953ab; 368c86556e827d898f043a4d5f378fa0; 7411d0d29db91f2625ee36d438eb6ac4; 3ea4e9fd297b3058ebbb360c1581aaac;
rattsillis.com/pusk2.exe - MD5: dae9e7653573478a6b41a62f7cb99c12; b73705c097c9be9779730d801ad098e0; d7952c1e77d7bb250cdfa88e157fb5a8
Known MD5 modifications for pusk3.exe at sdkjgndfjnf.ru: 8672f021e7705b6a8132b7dfc21617cf
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8; ebf7278a7239378e7d70d426779962ce
sdkjgndfjnf.ru/pusk2.exe - MD5: d9e36e25a3181f574fd5d520cb501d3a
sdkjgndfjnf.ru/pusk.exe - MD5: fce04f7681283207d585561ed91e77b4
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8
Detection rate for blood.exe:
blood.exe - Trojan-Spy.Win32.Zbot - 25/44 (56.8%)
MD5 : 577cf0b7ca3d5bcbe35764024f241fa8
SHA1 : 30f542a44d06d9125cdfbdd38d79de778e4c0791
SHA256: 1741ef5d24641ee99b5d78a68109162bebc714c3d19abc37e3d4472f3dcd6f18
_FDIC Notification
Spamvertised attachments: FDIC_Document.zip
Detection rate:FDIC_Document.exe - Gen:Trojan.Heur.FU.bqW@a45Fklbi - 35/44 (79.5%)
Upon execution phones back to:
rattsillis.com/ftp/g.php
rattsillis.com/blood.exe
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
What's particularly interesting is the fact that both campaigns have been launched by the same cybercriminal, with the same C&C - rattsillis.com also seen in the spamvertised ACH Payment Canceled campaign.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
_Uniform Traffic Tickets
Spamvertised attachments - Ticket-728-2011.zip; Ticket-064-211.zip; Ticket-728-2011.zip
Detection rates:
Ticket.exe - Gen:Trojan.Heur.FU.bqW@aK9ebrii - Detection rate: 37/43 (86.0%)
MD5 : 6361d4a40485345c18473f3c6b4b6609
SHA1 : 50b09bb2e0044aa139a84c2e445a56f01d70c185
SHA256: ca67a14bfed2a7bc2ac8be9c01cb17d5da12b75320b4bad4fe8d8a6759ad9725
Ticket1.exe - Trojan-Downloader.Win32.Small.ccxz - Detection rate: 36/44 (81.8%)
MD5 : e2a2d67b8a52ae655f92779bec296676
SHA1 : ed3df72b4e073ffba7174ebc8cb77b2b7d012cbf
SHA256: 50b104c5f8314327e03b01e7f7c2535d8de7cd9f73f8e16d1364c7fd021a90cc
Upon execution the samples phone back to:
sdkjgndfjnf.ru/pusk3.exe - 91.220.0.55 (responding to the same IP is also survey-providers.info) - AS51630 - Email: admin@sdkjgndfjnf.ru
rattsillis.com/ftp/g.php - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
rattsillis.com/pusk3.exe - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
DNS emulation of ns1.lemanbrostm.info reveals two domains belidiskalom.com - 178.208.76.175 - Email: admin@belidiskalom.com and lemanbrostm.info - Email: coz@yahoo.com using the same name server.
Known MD5 modifications for pusk3.exe at rattsillis.com:
c6dab856705b5dfd09b2adbe10701b05
f167213c6a79f2313995e80a8ac29939
f4764cce5c3795b1d63a299a5329d2e2
dae9e7653573478a6b41a62f7cb99c12
69c983c9dfaf37e346004c9aaf54a3d0
d875b8e32a231405c7fa96b810e9b361
628270c6e44b0fa21ef8e87c6bc36f57
9b69dabd876e967bcd2eb85465175e3b
0434c084dba8626df980c7974d5728e1
Related binaries and associated MD5 modifications:
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
rattsillis.com/pusk.exe - MD5: 55d8e25bc373a98c5c29284c989953ab; 368c86556e827d898f043a4d5f378fa0; 7411d0d29db91f2625ee36d438eb6ac4; 3ea4e9fd297b3058ebbb360c1581aaac;
rattsillis.com/pusk2.exe - MD5: dae9e7653573478a6b41a62f7cb99c12; b73705c097c9be9779730d801ad098e0; d7952c1e77d7bb250cdfa88e157fb5a8
Known MD5 modifications for pusk3.exe at sdkjgndfjnf.ru: 8672f021e7705b6a8132b7dfc21617cf
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8; ebf7278a7239378e7d70d426779962ce
sdkjgndfjnf.ru/pusk2.exe - MD5: d9e36e25a3181f574fd5d520cb501d3a
sdkjgndfjnf.ru/pusk.exe - MD5: fce04f7681283207d585561ed91e77b4
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8
Detection rate for blood.exe:
blood.exe - Trojan-Spy.Win32.Zbot - 25/44 (56.8%)
MD5 : 577cf0b7ca3d5bcbe35764024f241fa8
SHA1 : 30f542a44d06d9125cdfbdd38d79de778e4c0791
SHA256: 1741ef5d24641ee99b5d78a68109162bebc714c3d19abc37e3d4472f3dcd6f18
_FDIC Notification
Spamvertised attachments: FDIC_Document.zip
Detection rate:FDIC_Document.exe - Gen:Trojan.Heur.FU.bqW@a45Fklbi - 35/44 (79.5%)
| MD5 : 7b5a271c58c6bb18d79cd48353127ff6 |
| SHA1 : 6526b6097df42f93bee25d7ea73f95d2fcc24d3a |
| SHA256: a09165c71a8dd2a1338b2bd0c92ae07495041ae15592e3432bd50600e6ef2af0 |
Upon execution phones back to:
rattsillis.com/ftp/g.php
rattsillis.com/blood.exe
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
What's particularly interesting is the fact that both campaigns have been launched by the same cybercriminal, with the same C&C - rattsillis.com also seen in the spamvertised ACH Payment Canceled campaign.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Spamvertised 'Uniform Traffic Ticket' and 'FDIC Notifications' Serving Malware - Historical OSINT
The following intelligence brief will summarize the findings from a brief analysis performed on two malware campaigns from August, namely, the spamvertised Uniform Traffic Tickets and the FDIC Notification.
_Uniform Traffic Tickets
Spamvertised attachments - Ticket-728-2011.zip; Ticket-064-211.zip; Ticket-728-2011.zip
Detection rates:
Ticket.exe - Gen:Trojan.Heur.FU.bqW@aK9ebrii - Detection rate: 37/43 (86.0%)
MD5 : 6361d4a40485345c18473f3c6b4b6609
SHA1 : 50b09bb2e0044aa139a84c2e445a56f01d70c185
SHA256: ca67a14bfed2a7bc2ac8be9c01cb17d5da12b75320b4bad4fe8d8a6759ad9725
Ticket1.exe - Trojan-Downloader.Win32.Small.ccxz - Detection rate: 36/44 (81.8%)
MD5 : e2a2d67b8a52ae655f92779bec296676
SHA1 : ed3df72b4e073ffba7174ebc8cb77b2b7d012cbf
SHA256: 50b104c5f8314327e03b01e7f7c2535d8de7cd9f73f8e16d1364c7fd021a90cc
Upon execution the samples phone back to:
sdkjgndfjnf.ru/pusk3.exe - 91.220.0.55 (responding to the same IP is also survey-providers.info) - AS51630 - Email: admin@sdkjgndfjnf.ru
rattsillis.com/ftp/g.php - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
rattsillis.com/pusk3.exe - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
DNS emulation of ns1.lemanbrostm.info reveals two domains belidiskalom.com - 178.208.76.175 - Email: admin@belidiskalom.com and lemanbrostm.info - Email: coz@yahoo.com using the same name server.
Known MD5 modifications for pusk3.exe at rattsillis.com:
c6dab856705b5dfd09b2adbe10701b05
f167213c6a79f2313995e80a8ac29939
f4764cce5c3795b1d63a299a5329d2e2
dae9e7653573478a6b41a62f7cb99c12
69c983c9dfaf37e346004c9aaf54a3d0
d875b8e32a231405c7fa96b810e9b361
628270c6e44b0fa21ef8e87c6bc36f57
9b69dabd876e967bcd2eb85465175e3b
0434c084dba8626df980c7974d5728e1
Related binaries and associated MD5 modifications:
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
rattsillis.com/pusk.exe - MD5: 55d8e25bc373a98c5c29284c989953ab; 368c86556e827d898f043a4d5f378fa0; 7411d0d29db91f2625ee36d438eb6ac4; 3ea4e9fd297b3058ebbb360c1581aaac;
rattsillis.com/pusk2.exe - MD5: dae9e7653573478a6b41a62f7cb99c12; b73705c097c9be9779730d801ad098e0; d7952c1e77d7bb250cdfa88e157fb5a8
Known MD5 modifications for pusk3.exe at sdkjgndfjnf.ru: 8672f021e7705b6a8132b7dfc21617cf
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8; ebf7278a7239378e7d70d426779962ce
sdkjgndfjnf.ru/pusk2.exe - MD5: d9e36e25a3181f574fd5d520cb501d3a
sdkjgndfjnf.ru/pusk.exe - MD5: fce04f7681283207d585561ed91e77b4
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8
Detection rate for blood.exe:
blood.exe - Trojan-Spy.Win32.Zbot - 25/44 (56.8%)
MD5 : 577cf0b7ca3d5bcbe35764024f241fa8
SHA1 : 30f542a44d06d9125cdfbdd38d79de778e4c0791
SHA256: 1741ef5d24641ee99b5d78a68109162bebc714c3d19abc37e3d4472f3dcd6f18
_FDIC Notification
Spamvertised attachments: FDIC_Document.zip
Detection rate:FDIC_Document.exe - Gen:Trojan.Heur.FU.bqW@a45Fklbi - 35/44 (79.5%)
Upon execution phones back to:
rattsillis.com/ftp/g.php
rattsillis.com/blood.exe
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
What's particularly interesting is the fact that both campaigns have been launched by the same cybercriminal, with the same C&C - rattsillis.com also seen in the spamvertised ACH Payment Canceled campaign.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
_Uniform Traffic Tickets
Spamvertised attachments - Ticket-728-2011.zip; Ticket-064-211.zip; Ticket-728-2011.zip
Detection rates:
Ticket.exe - Gen:Trojan.Heur.FU.bqW@aK9ebrii - Detection rate: 37/43 (86.0%)
MD5 : 6361d4a40485345c18473f3c6b4b6609
SHA1 : 50b09bb2e0044aa139a84c2e445a56f01d70c185
SHA256: ca67a14bfed2a7bc2ac8be9c01cb17d5da12b75320b4bad4fe8d8a6759ad9725
Ticket1.exe - Trojan-Downloader.Win32.Small.ccxz - Detection rate: 36/44 (81.8%)
MD5 : e2a2d67b8a52ae655f92779bec296676
SHA1 : ed3df72b4e073ffba7174ebc8cb77b2b7d012cbf
SHA256: 50b104c5f8314327e03b01e7f7c2535d8de7cd9f73f8e16d1364c7fd021a90cc
Upon execution the samples phone back to:
sdkjgndfjnf.ru/pusk3.exe - 91.220.0.55 (responding to the same IP is also survey-providers.info) - AS51630 - Email: admin@sdkjgndfjnf.ru
rattsillis.com/ftp/g.php - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
rattsillis.com/pusk3.exe - 195.189.226.109; 178.208.77.247; 195.189.226.107; 195.189.226.108 - AS41018 - Email: admin@jokelimo.com
DNS emulation of ns1.lemanbrostm.info reveals two domains belidiskalom.com - 178.208.76.175 - Email: admin@belidiskalom.com and lemanbrostm.info - Email: coz@yahoo.com using the same name server.
Known MD5 modifications for pusk3.exe at rattsillis.com:
c6dab856705b5dfd09b2adbe10701b05
f167213c6a79f2313995e80a8ac29939
f4764cce5c3795b1d63a299a5329d2e2
dae9e7653573478a6b41a62f7cb99c12
69c983c9dfaf37e346004c9aaf54a3d0
d875b8e32a231405c7fa96b810e9b361
628270c6e44b0fa21ef8e87c6bc36f57
9b69dabd876e967bcd2eb85465175e3b
0434c084dba8626df980c7974d5728e1
Related binaries and associated MD5 modifications:
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
rattsillis.com/pusk.exe - MD5: 55d8e25bc373a98c5c29284c989953ab; 368c86556e827d898f043a4d5f378fa0; 7411d0d29db91f2625ee36d438eb6ac4; 3ea4e9fd297b3058ebbb360c1581aaac;
rattsillis.com/pusk2.exe - MD5: dae9e7653573478a6b41a62f7cb99c12; b73705c097c9be9779730d801ad098e0; d7952c1e77d7bb250cdfa88e157fb5a8
Known MD5 modifications for pusk3.exe at sdkjgndfjnf.ru: 8672f021e7705b6a8132b7dfc21617cf
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8; ebf7278a7239378e7d70d426779962ce
sdkjgndfjnf.ru/pusk2.exe - MD5: d9e36e25a3181f574fd5d520cb501d3a
sdkjgndfjnf.ru/pusk.exe - MD5: fce04f7681283207d585561ed91e77b4
sdkjgndfjnf.ru/blood.exe - MD5: 577cf0b7ca3d5bcbe35764024f241fa8
Detection rate for blood.exe:
blood.exe - Trojan-Spy.Win32.Zbot - 25/44 (56.8%)
MD5 : 577cf0b7ca3d5bcbe35764024f241fa8
SHA1 : 30f542a44d06d9125cdfbdd38d79de778e4c0791
SHA256: 1741ef5d24641ee99b5d78a68109162bebc714c3d19abc37e3d4472f3dcd6f18
_FDIC Notification
Spamvertised attachments: FDIC_Document.zip
Detection rate:FDIC_Document.exe - Gen:Trojan.Heur.FU.bqW@a45Fklbi - 35/44 (79.5%)
| MD5 : 7b5a271c58c6bb18d79cd48353127ff6 |
| SHA1 : 6526b6097df42f93bee25d7ea73f95d2fcc24d3a |
| SHA256: a09165c71a8dd2a1338b2bd0c92ae07495041ae15592e3432bd50600e6ef2af0 |
Upon execution phones back to:
rattsillis.com/ftp/g.php
rattsillis.com/blood.exe
rattsillis.com/blood.exe - MD5: 23795cb9b2f5e19eff0df0cf2fba9247; 82b6f18b130a1f0ce1ce928d0980fab0
What's particularly interesting is the fact that both campaigns have been launched by the same cybercriminal, with the same C&C - rattsillis.com also seen in the spamvertised ACH Payment Canceled campaign.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
Tags:
Botnet,
FDIC,
Hacking,
Information Security,
Malicious Software,
Security,
Spam,
Spam Campaign,
Spam Operations
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Tuesday, September 27, 2011
Summarizing ZDNet's Zero Day Posts for August
The following is a brief summary of all of my posts at ZDNet's Zero Day for August. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
01. Study: Rootkits target pirated copies of Windows XP
02. 56 percent of enterprise users using vulnerable Adobe Reader plugins
03. New malware attack circulating on Facebook
04. Kaspersky: 12 different vulnerabilities detected on every PC
05. Spamvertised Uniform traffic tickets and invoices lead to malware
06. Latest version of Skype susceptible to malicious code injection flaw
07. Spamvertised 'Scan from a Xerox WorkCentre Pro' leads to malware
08. Malware Watch: FDIC and Western Union themed emails lead to malware
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
01. Study: Rootkits target pirated copies of Windows XP
02. 56 percent of enterprise users using vulnerable Adobe Reader plugins
03. New malware attack circulating on Facebook
04. Kaspersky: 12 different vulnerabilities detected on every PC
05. Spamvertised Uniform traffic tickets and invoices lead to malware
06. Latest version of Skype susceptible to malicious code injection flaw
07. Spamvertised 'Scan from a Xerox WorkCentre Pro' leads to malware
08. Malware Watch: FDIC and Western Union themed emails lead to malware
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Sunday, September 11, 2011
Summarizing 3 Years of Research Into Cyber Jihad
On this very special day, I'd like to honor the fallen by summarizing my research into cyber jihad, a topic I'm still highly passionate about. Enjoy and share it with your social circle!
- Tracking Down Internet Terrorist Propaganda
- Arabic Extremist Group Forum Messages' Characteristics
- Cyber Terrorism Communications and Propaganda
- A Cost-Benefit Analysis of Cyber Terrorism
- Current State of Internet Jihad
- Analysis of the Technical Mujahid - Issue One
- Full List of Hezbollah's Internet Sites
- Steganography and Cyber Terrorism Communications
- Hezbollah's DNS Service Providers from 1998 to 2006
- Mujahideen Secrets Encryption Tool
- Analyses of Cyber Jihadist Forums and Blogs
- Cyber Traps for Wannabe Jihadists
- Inshallahshaheed - Come Out, Come Out Wherever You Are
- GIMF Switching Blogs
- GIMF Now Permanently Shut Down
- GIMF - "We Will Remain"
- Wisdom of the Anti Cyber Jihadist Crowd
- Cyber Jihadist Blogs Switching Locations Again
- Electronic Jihad v3.0 - What Cyber Jihad Isn't
- Electronic Jihad's Targets List
- Teaching Cyber Jihadists How to Hack
- A Botnet of Infected Terrorists?
- Infecting Terrorist Suspects with Malware
- The Dark Web and Cyber Jihad
- Cyber Jihadist Hacking Teams
- Two Cyber Jihadist Blogs Now Offline
- Characteristics of Islamist Websites
- Cyber Traps for Wannabe Jihadists
- Mujahideen Secrets Encryption Tool
- An Analysis of the Technical Mujahid - Issue Two
- Terrorist Groups' Brand Identities
- A List of Terrorists' Blogs
- Jihadists' Anonymous Internet Surfing Preferences
- Sampling Jihadists' IPs
- Cyber Jihadists' and TOR
- A Cyber Jihadist DoS Tool
- GIMF Now Permanently Shut Down
- Mujahideen Secrets 2 Encryption Tool Released
- Terror on the Internet - Conflict of Interest
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Monday, August 29, 2011
Keeping Money Mule Recruiters on a Short Leash - Part Eleven
The following intelligence brief is part of the Keeping Money Mule Recruiters on a Short Leash series. In it, I'll expose currently active money mule recruitment domains, their domain registration details, currently responding IPs, and related ASs.
Money mule recruitment domains:
ACWOODE-GROUP.COM - 78.46.105.205 - Email: admin@acwoode-group.com
ACWOODE-GROUP.NET - 78.46.105.205 - Email: admin@acwoode-group.net
ART-GAPSON.COM - 78.46.105.205 - Email: admin@art-gapson.com
CONDOR-LLC-UK.NET - Email: admin@condor-llc-uk.net
CONDORLLC-UK.COM - Email: plods@fxmail.net
DE-DVFGROUP.BE
ELENTY-CO.NET - Email: abcs@mailti.com
ELENTY-LLC.COM - 78.46.105.205 - Email: admin@elenty-llc.com
fabia-art.com - 209.190.4.91 - Email: adios@cutemail.org
fine-artgroup.com - 209.190.4.91
GAPSONART.NET - 78.46.105.205 - Email: admin@gapsonart.net
gmd-contracting.com - 194.242.2.56 - Email: admin@gmd-contracting.com
GURU-GROUP.CC - 78.46.105.205 - Email: admin@guru-group.cc
GURU-GROUP.NET - 78.46.105.205 - Email: jj@cutemail.org
INTECHTODEX-GROUP.COM - 78.46.105.205 - Email: uq@mail13.com
ltd-scg.net - 209.190.4.91 - Email: amykylir@yahoo.com
NARTEN-ART.COM - 78.46.105.205 - Email: glamor@fxmail.net
NARTENART.NET - 78.46.105.205 - Email: admin@nartenart.net
panart-llc.com - 78.46.105.205 - Email: admin@panart-llc.com
REFINEMENT-ANTIQUE.COM - 78.46.105.205 - Email: xe@fxmail.net
REFINEMENTUK-LTD.NET - 78.46.105.205 - Email: admin@refinementuk-ltd.net
SKYLINE-ANTIQUE.COM - 78.46.105.205 - Email: blurs@mailae.com
SKYLINE-LTD.NET - 78.46.105.205 - Email: admin@skyline-ltd.net
techce-group.com - 184.168.64.173 - Email: admin@techce-group.com
TODEX-GROUP.NET - 78.46.105.205 - Email: admin@todex-group.net
triad-webs.com - 85.17.24.226
The domains reside within the following ASs: AS24940, HETZNER-AS Hetzner Online AG RZ; AS16265, LeaseWeb B.V. Amsterdam; AS26496, GODADDY .com, Inc.; AS10297, RoadRunner RR-RC-Enet-Columbus.
Name servers of notice:
NS1.MKNS.SU - 85.25.250.244 - Email: mkns@cheapbox.ru
NS2.MKNS.SU - 46.4.148.119
NS3.MKNS.SU - 184.82.158.76
NS1.MNAMEDL.SU - 85.25.250.211 - Email: mnamed@yourisp.ru
NS2.MNAMEDL.SU - 46.4.148.118
NS3.MNAMEDL.SU - 184.82.158.75
NS1.MLDNS.SU - 85.25.145.63 - Email: mldns@free-id.ru
NS2.MLDNS.SU - 46.4.148.74
NS3.MLDNS.SU - 184.82.158.74
NS1.NAMESUKNS.CC - Email: pal@bz3.ru
NS2.NAMESUKNS.CC
NS3.NAMESUKNS.CC
NS1.NAMEUK.AT - Email: admin@nameuk.at
NS2.NAMEUK.AT
NS3.NAMEUK.AT
NS1.UKDNSTART.NET - Email: admin@ukdnstart.ne
NS2.UKDNSTART.NET
NS3.UKDNSTART.NET
Monitoring of ongoing money mule recruitment campaigns is ongoing.
Related posts:
Keeping Money Mule Recruiters on a Short Leash - Part Ten
Keeping Money Mule Recruiters on a Short Leash - Part Nine
Keeping Money Mule Recruiters on a Short Leash - Part Eight - Historical OSINT
Keeping Money Mule Recruiters on a Short Leash - Part Seven
Keeping Money Mule Recruiters on a Short Leash - Part Six
Keeping Money Mule Recruiters on a Short Leash - Part Five
The DNS Infrastructure of the Money Mule Recruitment Ecosystem
Keeping Money Mule Recruiters on a Short Leash - Part Four
Money Mule Recruitment Campaign Serving Client-Side Exploits
Keeping Money Mule Recruiters on a Short Leash - Part Three
Money Mule Recruiters on Yahoo!'s Web Hosting
Dissecting an Ongoing Money Mule Recruitment Campaign
Keeping Money Mule Recruiters on a Short Leash - Part Two
Keeping Reshipping Mule Recruiters on a Short Leash
Keeping Money Mule Recruiters on a Short Leash
Standardizing the Money Mule Recruitment Process
Inside a Money Laundering Group's Spamming Operations
Money Mule Recruiters use ASProx's Fast Fluxing Services
Money Mules Syndicate Actively Recruiting Since 2002
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Keeping Money Mule Recruiters on a Short Leash - Part Eleven
The following intelligence brief is part of the Keeping Money Mule Recruiters on a Short Leash series. In it, I'll expose currently active money mule recruitment domains, their domain registration details, currently responding IPs, and related ASs.
Money mule recruitment domains:
ACWOODE-GROUP.COM - 78.46.105.205 - Email: admin@acwoode-group.com
ACWOODE-GROUP.NET - 78.46.105.205 - Email: admin@acwoode-group.net
ART-GAPSON.COM - 78.46.105.205 - Email: admin@art-gapson.com
CONDOR-LLC-UK.NET - Email: admin@condor-llc-uk.net
CONDORLLC-UK.COM - Email: plods@fxmail.net
DE-DVFGROUP.BE
ELENTY-CO.NET - Email: abcs@mailti.com
ELENTY-LLC.COM - 78.46.105.205 - Email: admin@elenty-llc.com
fabia-art.com - 209.190.4.91 - Email: adios@cutemail.org
fine-artgroup.com - 209.190.4.91
GAPSONART.NET - 78.46.105.205 - Email: admin@gapsonart.net
gmd-contracting.com - 194.242.2.56 - Email: admin@gmd-contracting.com
GURU-GROUP.CC - 78.46.105.205 - Email: admin@guru-group.cc
GURU-GROUP.NET - 78.46.105.205 - Email: jj@cutemail.org
INTECHTODEX-GROUP.COM - 78.46.105.205 - Email: uq@mail13.com
ltd-scg.net - 209.190.4.91 - Email: amykylir@yahoo.com
NARTEN-ART.COM - 78.46.105.205 - Email: glamor@fxmail.net
NARTENART.NET - 78.46.105.205 - Email: admin@nartenart.net
panart-llc.com - 78.46.105.205 - Email: admin@panart-llc.com
REFINEMENT-ANTIQUE.COM - 78.46.105.205 - Email: xe@fxmail.net
REFINEMENTUK-LTD.NET - 78.46.105.205 - Email: admin@refinementuk-ltd.net
SKYLINE-ANTIQUE.COM - 78.46.105.205 - Email: blurs@mailae.com
SKYLINE-LTD.NET - 78.46.105.205 - Email: admin@skyline-ltd.net
techce-group.com - 184.168.64.173 - Email: admin@techce-group.com
TODEX-GROUP.NET - 78.46.105.205 - Email: admin@todex-group.net
triad-webs.com - 85.17.24.226
The domains reside within the following ASs: AS24940, HETZNER-AS Hetzner Online AG RZ; AS16265, LeaseWeb B.V. Amsterdam; AS26496, GODADDY .com, Inc.; AS10297, RoadRunner RR-RC-Enet-Columbus.
Name servers of notice:
NS1.MKNS.SU - 85.25.250.244 - Email: mkns@cheapbox.ru
NS2.MKNS.SU - 46.4.148.119
NS3.MKNS.SU - 184.82.158.76
NS1.MNAMEDL.SU - 85.25.250.211 - Email: mnamed@yourisp.ru
NS2.MNAMEDL.SU - 46.4.148.118
NS3.MNAMEDL.SU - 184.82.158.75
NS1.MLDNS.SU - 85.25.145.63 - Email: mldns@free-id.ru
NS2.MLDNS.SU - 46.4.148.74
NS3.MLDNS.SU - 184.82.158.74
NS1.NAMESUKNS.CC - Email: pal@bz3.ru
NS2.NAMESUKNS.CC
NS3.NAMESUKNS.CC
NS1.NAMEUK.AT - Email: admin@nameuk.at
NS2.NAMEUK.AT
NS3.NAMEUK.AT
NS1.UKDNSTART.NET - Email: admin@ukdnstart.ne
NS2.UKDNSTART.NET
NS3.UKDNSTART.NET
Monitoring of ongoing money mule recruitment campaigns is ongoing.
Related posts:
Keeping Money Mule Recruiters on a Short Leash - Part Ten
Keeping Money Mule Recruiters on a Short Leash - Part Nine
Keeping Money Mule Recruiters on a Short Leash - Part Eight - Historical OSINT
Keeping Money Mule Recruiters on a Short Leash - Part Seven
Keeping Money Mule Recruiters on a Short Leash - Part Six
Keeping Money Mule Recruiters on a Short Leash - Part Five
The DNS Infrastructure of the Money Mule Recruitment Ecosystem
Keeping Money Mule Recruiters on a Short Leash - Part Four
Money Mule Recruitment Campaign Serving Client-Side Exploits
Keeping Money Mule Recruiters on a Short Leash - Part Three
Money Mule Recruiters on Yahoo!'s Web Hosting
Dissecting an Ongoing Money Mule Recruitment Campaign
Keeping Money Mule Recruiters on a Short Leash - Part Two
Keeping Reshipping Mule Recruiters on a Short Leash
Keeping Money Mule Recruiters on a Short Leash
Standardizing the Money Mule Recruitment Process
Inside a Money Laundering Group's Spamming Operations
Money Mule Recruiters use ASProx's Fast Fluxing Services
Money Mules Syndicate Actively Recruiting Since 2002
This post has been reproduced from Dancho Danchev's blog.
Tags:
Cybercrime,
Hacking,
Information Security,
Money Laundering,
Money Mule,
Money Mule Recruitment,
Security
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
A Peek Inside Web Malware Exploitation Kits
With web malware exploitation kits, continuing to represent the attack method of choice for the majority of cybercriminals thanks to the overall susceptibility of end and enterprise users to client-side exploitation attacks, it's always worth taking a peek inside them from the perspective of the malicious attacker.
In this post, we'll take a peek inside three web malware exploitation kits, and discuss what makes them think in terms of infected OSs, browser plugins and client-side exploits.
_Dragon Pack Web Malware Exploitation Kit
What we've got here is a rather modest in terms of activity, web malware exploitation kit admin panel. We've got 45 successful loads based on 588 unique visits, with the JavaRox exploit executed 42 times, successfully infecting 20 Firefox users. The exploits have successfully loaded on Windows XP 14 times, on Windows XP SP2 3 times, on Windows Vista 12 times, and on Windows 7 15 times.
_Dragon Exploit Pack
The Dragon Exploit Pack has 45 successful loads based on 587 unique visitors, with the JavaJDK exploit executed successfully 42 times. The kit is counting 13 successful loads on MSIE 8, and another 20 on Firefox, with 14 successful loads recorded for Windows XP, 2 on Windows XP SP2, 12 on Windows Vista and 15 on Windows 7.
_Katrin Exploit Pack
The Katrin Exploit Pack has 3277 successful loads based on 19933 unique visits, which represents a 17.32% infection rate. The Java JSM exploit has been successfully loaded 535 times, Java SMB has been loaded 576 times, Java OBE has been loaded 914 times, Old 4 PDF has been loaded 87 times, Libtiff PDF has been loaded 726 times, MDAC has been loaded 96 times, Snapshot has been loaded 104 times, and HCP has been loaded 239 times.
The kit is counting 452 successful exploitation attempts against MSIE 5, 786 against MSIE7, 1198 against MSIE 8, 274 against Chrome, 522 against Firefox, 24 against Opera and 14 against Safari. The majority of loads have affected Windows XP installations, with 2107 successful loads targeting the OS, following 625 on Windows Vista, and 503 on Windows 7.
_Liberty Exploit Pack
The Liberty Exploit pack screenshot, is showing the proportion successfully infected web browsers, with total of 555 successful loads based on 3029 unique visitors. 397 loads have affected Internet Explorer 6, 89 Internet Explorer 7, and 54 Firefox.
_Bleeding Life Exploit Pack
In this Bleeding Life web malware exploitation kit, we can clearly seen the dynamics behind the infections taking place. We see 554 successful loads based on 4106 unique visitors. JavaSignedApplet has been executed 161 times, Adobe-90-2010-0188 has been executed 67 times, Adobe-80-2010-0188 has been executed 46 times, Java-2010-0842 has been executed 203 times, Adobe-2008-2992 has been executed 74 times, and Adobe-2010-1297 has been executed 2 times.
The majority of the infected population is based in the U.S, United Kingdom, Qatar, and Malaysia. Windows XP has the highest market share of infected OSs, with 336 successful loads based on 2098 unique visitors. Followed by Windows 7 with 139 loads based on 1256 unique visitors, and 73 unique loads based on 719 unique visitors for Windows Vista.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
In this post, we'll take a peek inside three web malware exploitation kits, and discuss what makes them think in terms of infected OSs, browser plugins and client-side exploits.
_Dragon Pack Web Malware Exploitation Kit
What we've got here is a rather modest in terms of activity, web malware exploitation kit admin panel. We've got 45 successful loads based on 588 unique visits, with the JavaRox exploit executed 42 times, successfully infecting 20 Firefox users. The exploits have successfully loaded on Windows XP 14 times, on Windows XP SP2 3 times, on Windows Vista 12 times, and on Windows 7 15 times.
_Dragon Exploit Pack
The Dragon Exploit Pack has 45 successful loads based on 587 unique visitors, with the JavaJDK exploit executed successfully 42 times. The kit is counting 13 successful loads on MSIE 8, and another 20 on Firefox, with 14 successful loads recorded for Windows XP, 2 on Windows XP SP2, 12 on Windows Vista and 15 on Windows 7.
_Katrin Exploit Pack
The Katrin Exploit Pack has 3277 successful loads based on 19933 unique visits, which represents a 17.32% infection rate. The Java JSM exploit has been successfully loaded 535 times, Java SMB has been loaded 576 times, Java OBE has been loaded 914 times, Old 4 PDF has been loaded 87 times, Libtiff PDF has been loaded 726 times, MDAC has been loaded 96 times, Snapshot has been loaded 104 times, and HCP has been loaded 239 times.
The kit is counting 452 successful exploitation attempts against MSIE 5, 786 against MSIE7, 1198 against MSIE 8, 274 against Chrome, 522 against Firefox, 24 against Opera and 14 against Safari. The majority of loads have affected Windows XP installations, with 2107 successful loads targeting the OS, following 625 on Windows Vista, and 503 on Windows 7.
_Liberty Exploit Pack
The Liberty Exploit pack screenshot, is showing the proportion successfully infected web browsers, with total of 555 successful loads based on 3029 unique visitors. 397 loads have affected Internet Explorer 6, 89 Internet Explorer 7, and 54 Firefox.
_Bleeding Life Exploit Pack
In this Bleeding Life web malware exploitation kit, we can clearly seen the dynamics behind the infections taking place. We see 554 successful loads based on 4106 unique visitors. JavaSignedApplet has been executed 161 times, Adobe-90-2010-0188 has been executed 67 times, Adobe-80-2010-0188 has been executed 46 times, Java-2010-0842 has been executed 203 times, Adobe-2008-2992 has been executed 74 times, and Adobe-2010-1297 has been executed 2 times.
The majority of the infected population is based in the U.S, United Kingdom, Qatar, and Malaysia. Windows XP has the highest market share of infected OSs, with 336 successful loads based on 2098 unique visitors. Followed by Windows 7 with 139 loads based on 1256 unique visitors, and 73 unique loads based on 719 unique visitors for Windows Vista.
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Monday, August 22, 2011
Summarizing ZDNet's Zero Day Posts for July
The following is a brief summary of all of my posts at ZDNet's Zero Day for July. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
01.'Leaked Video of Casey Anthony CONFESSING to Lawyer!' scam spreading on Facebook
02. Anonymous leaks 90,000+ emails from compromised military contractor Booz Allen Hamilton
03. 'This girl must be Out of her Mind to do this on live Television!' scam spreading on Facebook
04. Spamvertised bank statements serving scareware
05. Internet Explorer 9 outperforms competing browsers in malware blocking test
06.'Leaked Video! Amy Winehouse on Crack hours before death' scam spreading on Facebook
07.Pfizer's Facebook hacked by AntiSec
08. 90,000+ pages compromised in mass iFrame injection attack
09. Amazon's cloud services systematically exploited by cybercriminals
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Thursday, July 07, 2011
Keeping Money Mule Recruiters on a Short Leash - Part Ten
The following intelligence brief is part of the Keeping Money Mule Recruiters on a Short Leash series. In it, I'll expose currently active money mule recruitment domains, their domain registration details, currently responding IPs, and related ASs.
Currently active money mule recruitment domains:
ACWOODE-GROUP.COM - 184.168.64.173 - Email: admin@acwoode-group.com
ACWOODE-GROUP.NET - 184.168.64.173 - Email: admin@acwoode-group.net
ART-GROUPINTEGRETED.COM - 78.46.105.205 - Email: admin@art-groupintegreted.com
ARTINTEGRATED-GROUP.NET - 78.46.105.205 - Email: crony@cutemail.org
COMPLETE-ART-GROUP-LTD.COM - 193.105.134.233 - Email: saps@cutemail.org
COMPLETE-ART-UK.NET - 193.105.134.232 - Email: admin@complete-art-uk.net
CONDORLLC-UK.COM - 193.105.134.231 - Email: plods@fxmail.net
CONDOR-LLC-UK.NET - 193.105.134.233 - Email: admin@condor-llc-uk.net
CONTEMP-USAINC.COM - 184.168.64.173 - Email: admin@contemp-usainc.com
CONTEMP-USGROUP.COM - 184.168.64.173 - Email: admin@contemp-usgroup.com
DE-KADEGROUP.CC - 193.105.134.230 - Email: cents@mailae.com
DERWOODE-GROUP.CC - 98.141.220.115 - Email: web@derwoode-group.cc
ELENTY-CO.NET - 184.168.64.173 - Email: abcs@mailti.com
ELENTY-LLC.COM - 184.168.64.173 - Email: admin@elenty-llc.com
GAPSONART.NET - 184.168.64.173 - Email: admin@gapsonart.net
GLACIS-GROUPUK.NET - 78.46.105.205 - Email: admin@glacis-groupuk.net
GURU-GROUP.CC - 184.168.64.173 - Email: admin@guru-group.cc
GURU-GROUP.NET - 184.168.64.173 - Email: jj@cutemail.org
INTECHTODEX-GROUP.COM - 184.168.64.173 - Email: uq@mail13.com
INTEGRATED-EUROPE-IT.NET - 78.46.105.205 - Email: admin@integrated-europe-it.net
ITAGROUP-USA.NET - 98.141.220.117 - Email: admin@itagroup-usa.net
IT-ANALISYS.COM - 98.141.220.115 - Email: yea@mailae.com
ITANALYSISGROUP.NET - 98.141.220.116 - Email: admin@itanalysisgroup.net
KADE-GROUPDE.NET - 78.46.105.205 - Email: zigzag@fxmail.net
MASTERARTUSA.COM - 98.141.220.114 - Email: day@mailae.com
NARTEN-ART.COM - 209.190.4.91 - Email: glamor@fxmail.net
NARTENART.NET - 209.190.4.91 - Email: admin@nartenart.net
quad-groupuk.cc - 78.46.105.205 - Email: prissy@mailae.com
REFINEMENT-ANTIQUE.COM - 184.168.64.173 - Email: xe@fxmail.net
SCAR-BEIINC.COM - 184.168.64.173 - Email: admin@scar-beiinc.com
SKYLINE-ANTIQUE.COM - 209.190.4.91 - Email: blurs@mailae.com
SKYLINE-LTD.NET - 209.190.4.91 - Email: admin@skyline-ltd.net
SMARTLLC-UK.COM - 193.105.134.234 - Email: admin@smartllc-uk.com
SMART-LLC-UK.NET - 193.105.134.233 - Email: pol@mailae.com
SPECIAL-ARTUK.COM - 193.105.134.232 - Email: admin@special-artuk.com
SUBLIMELTD.COM - 98.141.220.118 - Email: admin@sublimeltd.com
TODEX-GROUP.NET - 184.168.64.173 - Email: admin@todex-group.net
The domains reside within the following ASs: AS10297, RoadRunner RR-RC; AS42708; PORTLANE Network; AS26496; GODADDY.com; AS29713, INTERPLEXINC; AS24940, HETZNER-AS Hetzner Online.
Name servers of notice:
NS1.MKNS.SU - 85.25.250.244 - Email: mkns@cheapbox.ru
NS2.MKNS.SU - 46.4.148.119
NS3.MKNS.SU - 184.82.158.76
NS1.MLDNS.SU - 85.25.145.63 - Email: mldns@free-id.ru
NS2.MLDNS.SU - 46.4.148.74
NS3.MLDNS.SU - 184.82.158.74
NS1.MNAMEDL.SU - 85.25.250.211 - Email: mnamed@yourisp.ru
NS2.MNAMEDL.SU - 46.4.148.118
NS3.MNAMEDL.SU - 184.82.158.75
NS1.DNSUS.SU - 217.23.15.137 - Email: wifi@yourisp.ru
NS2.DNSUS.SU - 87.118.81.7
NS3.DNSUS.SU - 87.118.81.10
NS1.NAMEUSNS.SU - 217.23.15.138 - Email: lavier@bz3.ru
NS2.NAMEUSNS.SU - 84.19.161.7
NS3.NAMEUSNS.SU - 84.19.161.10
NS1.USDENNS.SU - 217.23.15.136 - Email: lipstick@free-id.ru
NS2.USDENNS.SU - 84.19.161.7
NS3.USDENNS.SU - 84.19.161.10
NS1.NAMESUKNS.CC - 86.55.210.4 - Email: pal@bz3.ru
NS2.NAMESUKNS.CC - 193.105.134.232
NS3.NAMESUKNS.CC - 193.105.134.237
NS1.NAMEUK.AT - 86.55.210.5 - Email: admin@nameuk.at
NS2.NAMEUK.AT - 193.105.134.233
NS3.NAMEUK.AT - 193.105.134.236
NS1.UKDNSTART.NET - 86.55.210.5 - Email: admin@ukdnstart.net
NS2.UKDNSTART.NET - 193.105.134.233
NS3.UKDNSTART.NET - 193.105.134.236
NS1.DENDRUYOS.NET - 86.55.210.4 - Email: admin@dendruyos.net
NS2.DENDRUYOS.NET - 193.105.134.232
NS3.DENDRUYOS.NET - 193.105.134.237
NS1.DEDNSAUTH.NET - 86.55.210.2 - Email: admin@dednsauth.net
NS2.DEDNSAUTH.NET - 193.105.134.230
NS3.DEDNSAUTH.NET - 193.105.134.239
NS1.DELTOPOOR.AT - 86.55.210.3 - Email: admin@deltopoor.at
NS2.DELTOPOOR.AT - 193.105.134.231
NS3.DELTOPOOR.AT - 193.105.134.238
Monitoring of ongoing money mule recruitment campaigns is ongoing.
Related posts:
Keeping Money Mule Recruiters on a Short Leash - Part Nine
Keeping Money Mule Recruiters on a Short Leash - Part Eight - Historical OSINT
Keeping Money Mule Recruiters on a Short Leash - Part Seven
Keeping Money Mule Recruiters on a Short Leash - Part Six
Keeping Money Mule Recruiters on a Short Leash - Part Five
The DNS Infrastructure of the Money Mule Recruitment Ecosystem
Keeping Money Mule Recruiters on a Short Leash - Part Four
Money Mule Recruitment Campaign Serving Client-Side Exploits
Keeping Money Mule Recruiters on a Short Leash - Part Three
Money Mule Recruiters on Yahoo!'s Web Hosting
Dissecting an Ongoing Money Mule Recruitment Campaign
Keeping Money Mule Recruiters on a Short Leash - Part Two
Keeping Reshipping Mule Recruiters on a Short Leash
Keeping Money Mule Recruiters on a Short Leash
Standardizing the Money Mule Recruitment Process
Inside a Money Laundering Group's Spamming Operations
Money Mule Recruiters use ASProx's Fast Fluxing Services
Money Mules Syndicate Actively Recruiting Since 2002
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Keeping Money Mule Recruiters on a Short Leash - Part Ten
The following intelligence brief is part of the Keeping Money Mule Recruiters on a Short Leash series. In it, I'll expose currently active money mule recruitment domains, their domain registration details, currently responding IPs, and related ASs.
Currently active money mule recruitment domains:
ACWOODE-GROUP.COM - 184.168.64.173 - Email: admin@acwoode-group.com
ACWOODE-GROUP.NET - 184.168.64.173 - Email: admin@acwoode-group.net
ART-GROUPINTEGRETED.COM - 78.46.105.205 - Email: admin@art-groupintegreted.com
ARTINTEGRATED-GROUP.NET - 78.46.105.205 - Email: crony@cutemail.org
COMPLETE-ART-GROUP-LTD.COM - 193.105.134.233 - Email: saps@cutemail.org
COMPLETE-ART-UK.NET - 193.105.134.232 - Email: admin@complete-art-uk.net
CONDORLLC-UK.COM - 193.105.134.231 - Email: plods@fxmail.net
CONDOR-LLC-UK.NET - 193.105.134.233 - Email: admin@condor-llc-uk.net
CONTEMP-USAINC.COM - 184.168.64.173 - Email: admin@contemp-usainc.com
CONTEMP-USGROUP.COM - 184.168.64.173 - Email: admin@contemp-usgroup.com
DE-KADEGROUP.CC - 193.105.134.230 - Email: cents@mailae.com
DERWOODE-GROUP.CC - 98.141.220.115 - Email: web@derwoode-group.cc
ELENTY-CO.NET - 184.168.64.173 - Email: abcs@mailti.com
ELENTY-LLC.COM - 184.168.64.173 - Email: admin@elenty-llc.com
GAPSONART.NET - 184.168.64.173 - Email: admin@gapsonart.net
GLACIS-GROUPUK.NET - 78.46.105.205 - Email: admin@glacis-groupuk.net
GURU-GROUP.CC - 184.168.64.173 - Email: admin@guru-group.cc
GURU-GROUP.NET - 184.168.64.173 - Email: jj@cutemail.org
INTECHTODEX-GROUP.COM - 184.168.64.173 - Email: uq@mail13.com
INTEGRATED-EUROPE-IT.NET - 78.46.105.205 - Email: admin@integrated-europe-it.net
ITAGROUP-USA.NET - 98.141.220.117 - Email: admin@itagroup-usa.net
IT-ANALISYS.COM - 98.141.220.115 - Email: yea@mailae.com
ITANALYSISGROUP.NET - 98.141.220.116 - Email: admin@itanalysisgroup.net
KADE-GROUPDE.NET - 78.46.105.205 - Email: zigzag@fxmail.net
MASTERARTUSA.COM - 98.141.220.114 - Email: day@mailae.com
NARTEN-ART.COM - 209.190.4.91 - Email: glamor@fxmail.net
NARTENART.NET - 209.190.4.91 - Email: admin@nartenart.net
quad-groupuk.cc - 78.46.105.205 - Email: prissy@mailae.com
REFINEMENT-ANTIQUE.COM - 184.168.64.173 - Email: xe@fxmail.net
SCAR-BEIINC.COM - 184.168.64.173 - Email: admin@scar-beiinc.com
SKYLINE-ANTIQUE.COM - 209.190.4.91 - Email: blurs@mailae.com
SKYLINE-LTD.NET - 209.190.4.91 - Email: admin@skyline-ltd.net
SMARTLLC-UK.COM - 193.105.134.234 - Email: admin@smartllc-uk.com
SMART-LLC-UK.NET - 193.105.134.233 - Email: pol@mailae.com
SPECIAL-ARTUK.COM - 193.105.134.232 - Email: admin@special-artuk.com
SUBLIMELTD.COM - 98.141.220.118 - Email: admin@sublimeltd.com
TODEX-GROUP.NET - 184.168.64.173 - Email: admin@todex-group.net
The domains reside within the following ASs: AS10297, RoadRunner RR-RC; AS42708; PORTLANE Network; AS26496; GODADDY.com; AS29713, INTERPLEXINC; AS24940, HETZNER-AS Hetzner Online.
Name servers of notice:
NS1.MKNS.SU - 85.25.250.244 - Email: mkns@cheapbox.ru
NS2.MKNS.SU - 46.4.148.119
NS3.MKNS.SU - 184.82.158.76
NS1.MLDNS.SU - 85.25.145.63 - Email: mldns@free-id.ru
NS2.MLDNS.SU - 46.4.148.74
NS3.MLDNS.SU - 184.82.158.74
NS1.MNAMEDL.SU - 85.25.250.211 - Email: mnamed@yourisp.ru
NS2.MNAMEDL.SU - 46.4.148.118
NS3.MNAMEDL.SU - 184.82.158.75
NS1.DNSUS.SU - 217.23.15.137 - Email: wifi@yourisp.ru
NS2.DNSUS.SU - 87.118.81.7
NS3.DNSUS.SU - 87.118.81.10
NS1.NAMEUSNS.SU - 217.23.15.138 - Email: lavier@bz3.ru
NS2.NAMEUSNS.SU - 84.19.161.7
NS3.NAMEUSNS.SU - 84.19.161.10
NS1.USDENNS.SU - 217.23.15.136 - Email: lipstick@free-id.ru
NS2.USDENNS.SU - 84.19.161.7
NS3.USDENNS.SU - 84.19.161.10
NS1.NAMESUKNS.CC - 86.55.210.4 - Email: pal@bz3.ru
NS2.NAMESUKNS.CC - 193.105.134.232
NS3.NAMESUKNS.CC - 193.105.134.237
NS1.NAMEUK.AT - 86.55.210.5 - Email: admin@nameuk.at
NS2.NAMEUK.AT - 193.105.134.233
NS3.NAMEUK.AT - 193.105.134.236
NS1.UKDNSTART.NET - 86.55.210.5 - Email: admin@ukdnstart.net
NS2.UKDNSTART.NET - 193.105.134.233
NS3.UKDNSTART.NET - 193.105.134.236
NS1.DENDRUYOS.NET - 86.55.210.4 - Email: admin@dendruyos.net
NS2.DENDRUYOS.NET - 193.105.134.232
NS3.DENDRUYOS.NET - 193.105.134.237
NS1.DEDNSAUTH.NET - 86.55.210.2 - Email: admin@dednsauth.net
NS2.DEDNSAUTH.NET - 193.105.134.230
NS3.DEDNSAUTH.NET - 193.105.134.239
NS1.DELTOPOOR.AT - 86.55.210.3 - Email: admin@deltopoor.at
NS2.DELTOPOOR.AT - 193.105.134.231
NS3.DELTOPOOR.AT - 193.105.134.238
Monitoring of ongoing money mule recruitment campaigns is ongoing.
Related posts:
Keeping Money Mule Recruiters on a Short Leash - Part Nine
Keeping Money Mule Recruiters on a Short Leash - Part Eight - Historical OSINT
Keeping Money Mule Recruiters on a Short Leash - Part Seven
Keeping Money Mule Recruiters on a Short Leash - Part Six
Keeping Money Mule Recruiters on a Short Leash - Part Five
The DNS Infrastructure of the Money Mule Recruitment Ecosystem
Keeping Money Mule Recruiters on a Short Leash - Part Four
Money Mule Recruitment Campaign Serving Client-Side Exploits
Keeping Money Mule Recruiters on a Short Leash - Part Three
Money Mule Recruiters on Yahoo!'s Web Hosting
Dissecting an Ongoing Money Mule Recruitment Campaign
Keeping Money Mule Recruiters on a Short Leash - Part Two
Keeping Reshipping Mule Recruiters on a Short Leash
Keeping Money Mule Recruiters on a Short Leash
Standardizing the Money Mule Recruitment Process
Inside a Money Laundering Group's Spamming Operations
Money Mule Recruiters use ASProx's Fast Fluxing Services
Money Mules Syndicate Actively Recruiting Since 2002
This post has been reproduced from Dancho Danchev's blog.
Tags:
Cybercrime,
Hacking,
Information Security,
Money Laundering,
Money Mule,
Money Mule Recruitment,
Security
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Summarizing ZDNet's Zero Day Posts for June
The following is a brief summary of all of my posts at ZDNet's Zero Day for June. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
01. 'Hot Lesbian Video - Rihanna and Hayden Panettiere' scam on Facebook leads to Mac malware
02. Sony Europe hacked by Lebanese grey hat hacker
03. Spamvertised United Parcel Service emails lead to scareware
04. The most common iPhone passcodes
05. AutoRun malware infections declining
06. 'McDonald's Free Dinner Day' emails lead to scareware
07. Two DDoS attacks hit Network Solutions
08. 'The Creator of LulzSec arrested in London' scam spreading on Facebook
09. Federal Reserve themed emails lead to ZeuS crimeware
10. 'Photographer commited SUICIDE 3 days after shooting THIS video!' scam spreading on Facebook
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Wednesday, June 08, 2011
Summarizing ZDNet's Zero Day Posts for May
The following is a brief summary of all of my posts at ZDNet's Zero Day for May. You can subscribe to my personal RSS feed, Zero Day's main feed, or follow me on Twitter:
Recommended reading:
01. Vishing attack on Skype pushing scareware
02. Commtouch: 71 percent increase in new zombies
03. Osama execution video scam spreading on Facebook
04. New MAC OS X scareware delivered through blackhat SEO
05. 'You visit illegal websites' FBI-themed emails lead to scareware
06. Fake Microsoft Patch Tuesday emails lead to ZeuS crimeware
07. 'Enable Dislike Button' scam spreading on Facebook
08. NASA's Goddard Space Flight Center FTP server hacked
09. 'Checkout Your PROFILE Stalkers' scam spreading on Facebook
10. 'The World Funniest Condom Commercial - LOL' scam spreading on Facebook
11. China's Blue Army: When nations harness hacktivists for information warfare
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
Recommended reading:
01. Vishing attack on Skype pushing scareware
02. Commtouch: 71 percent increase in new zombies
03. Osama execution video scam spreading on Facebook
04. New MAC OS X scareware delivered through blackhat SEO
05. 'You visit illegal websites' FBI-themed emails lead to scareware
06. Fake Microsoft Patch Tuesday emails lead to ZeuS crimeware
07. 'Enable Dislike Button' scam spreading on Facebook
08. NASA's Goddard Space Flight Center FTP server hacked
09. 'Checkout Your PROFILE Stalkers' scam spreading on Facebook
10. 'The World Funniest Condom Commercial - LOL' scam spreading on Facebook
11. China's Blue Army: When nations harness hacktivists for information warfare
This post has been reproduced from Dancho Danchev's blog. Follow him on Twitter.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Monday, May 30, 2011
Keeping Money Mule Recruiters on a Short Leash - Part Nine
The following brief summarizes currently active money mule recruitment web sites, actively recruiting money mules for the processing of fraudulently obtained funds.
Currently active sites residing within AS42708, PORTLANE Network www.portlane.com; AS29713, INTERPLEXINC Interplex LLC; AS38913, Enter-Net-Team-AS; AS24940, HETZNER-AS Hetzner Online:
ATLANTALTD-UK.CC - 193.105.134.233
ATLANTA-LTD-UK.NET - 78.46.105.205 - Email: admin@atlanta-ltd-uk.net
3ATLANTA-UK.COM - 193.105.134.233
BLITZNET-GROUPINC.CC - 78.46.105.205 - Email: admin@derwart-group.at
5DALI-STYLE.COM - 98.141.220.117
DALISTYLE-GROUP.CC - 98.141.220.118 - Email: tolls@mailti.com
DERWOODE-GROUP.COM - 98.141.220.117
DERWOODE-GROUP.NET - 98.141.220.117
GLACIS-GROUPLLC.COM - 193.105.134.232
1GLACISGROUP-LLC.NET - 193.105.134.233
IT-AMIRA.NET - 86.55.210.3 - Email: support@it-amira.net
ITAMIRA-DE.COM - 86.55.210.6 - Email: admin@itamira-de.com
ITSERV-DE.CO - 78.46.105.205 - Email: admin@itserv-de.co
IT-SERVICELTD.BE - 78.46.105.205
KADE-GROUP.COM - 86.55.210.4 - Email: admin@kade-group.com
MASTERART-GROUP.COM - 98.141.220.116 - Email: east@mail13.com
MENDRYLTD.COM - 98.141.220.117 - Email: admin@mendryltd.com
MENZEL-GROUP.TV - 98.141.220.118 - Email: admin@devotion-company.com
MITISSANSERVICE-GROUP-LTD.CC - 98.141.220.117 - Email: berra@cutemail.org
MITISSANSERVICEGROUP-LTD.COM - 98.141.220.117 - Email: alibi@mailae.com
oregonltd-uk.cc - 86.55.210.5 - Email: cause@ca4.ru
PARLEN-GROUPLLC.COM - 98.141.220.118 - Email: admin@parlen-groupllc.com
PARLENGROUPLLC.NET - 98.141.220.114
PARLEN-GROUP-USA.COM - 98.141.220.118
quad-groupuk.cc - 86.55.210.6 - Email: prissy@mailae.com
QUAD-GROUPUK.CC - 86.55.210.6 - Email: prissy@mailae.com
QUAD-IT-GROUP.COM - 193.105.134.232 - Email: admin@quad-it-group.com
QUINTAGROUP.CC - 98.141.220.117 - Email: cola@mailae.com
QUINTA-GROUPUS.COM - 98.141.220.118 - Email: admin@quinta-groupus.com
QUINTA-LLC.NET - 98.141.220.118 - Email: admin@quinta-llc.net
REXTECHINNOVATION.COM - 98.141.220.118 - Email: admin@rextechinnovation.com
REXTECHLTD.CC - 98.141.220.115 - Email: blurt@fxmail.net
REXTECHLTD-US.COM - 98.141.220.118 - Email: admin@rextechltd-us.com
SPECIAL-ART-LTD.COM - 193.105.134.233 - Email: admin@special-art-ltd.com
SPECIAL-ART-UK.CC - 193.105.134.234
SUBLIME-LTD.NET - 98.141.220.118 - Email: admin@sublime-ltd.net
TARGETMARKETGROUP-LLC.CC - 98.141.220.117 - Email: admin@targetmarketgroup-llc.cc
TAZPROGLTD-US.COM - 98.141.220.117 - Email: admin@tazprogltd-us.co
VNSPROJECT-DE.CC - 78.46.105.205 - Email: admin@vnsproject-de.cc
VORTEXLLC-UK.COM - 193.105.134.232 - Email: admin@vortexllc-uk.com
VORTEX-LLC-UK.NET - 193.105.134.230 - Email: admin@vortex-llc-uk.net
Name servers of notice:
NS1.NAMESUKNS.CC - 178.162.172.48 - Email: pal@bz3.ru
NS2.NAMESUKNS.CC - 69.10.56.131
NS3.NAMESUKNS.CC - 66.199.229.123
NS1.NAMEUK.AT - 178.162.172.57 - Email: admin@nameuk.at
NS2.NAMEUK.AT - 69.10.56.132
NS3.NAMEUK.AT - 66.199.229.124
NS1.UKDNSTART.NET - 178.162.172.40 - Email: admin@ukdnstart.net
NS2.UKDNSTART.NET - 69.10.56.130
NS3.UKDNSTART.NET - 66.199.229.122
NS1.DNSUS.SU - 217.23.15.137 - Email: wifi@yourisp.ru
NS2.DNSUS.SU - 87.118.81.7
NS3.DNSUS.SU - 87.118.81.10
NS1.NAMEUSNS.SU - 217.23.15.138 - Email: lavier@bz3.ru
NS2.NAMEUSNS.SU - 84.19.161.7
NS3.NAMEUSNS.SU - 84.19.161.10
NS1.USDENNS.SU - 217.23.15.136 - Email: lipstick@free-id.ru
NS2.USDENNS.SU - 84.19.161.7
NS3.USDENNS.SU - 84.19.161.10
Monitoring of money mule recruitment campaigns is ongoing.
Related posts:
Keeping Money Mule Recruiters on a Short Leash - Part Eight - Historical OSINT
Keeping Money Mule Recruiters on a Short Leash - Part Seven
Keeping Money Mule Recruiters on a Short Leash - Part Six
Keeping Money Mule Recruiters on a Short Leash - Part Five
The DNS Infrastructure of the Money Mule Recruitment Ecosystem
Keeping Money Mule Recruiters on a Short Leash - Part Four
Money Mule Recruitment Campaign Serving Client-Side Exploits
Keeping Money Mule Recruiters on a Short Leash - Part Three
Money Mule Recruiters on Yahoo!'s Web Hosting
Dissecting an Ongoing Money Mule Recruitment Campaign
Keeping Money Mule Recruiters on a Short Leash - Part Two
Keeping Reshipping Mule Recruiters on a Short Leash
Keeping Money Mule Recruiters on a Short Leash
Standardizing the Money Mule Recruitment Process
Inside a Money Laundering Group's Spamming Operations
Money Mule Recruiters use ASProx's Fast Fluxing Services
Money Mules Syndicate Actively Recruiting Since 2002
This post has been reproduced from Dancho Danchev's blog.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Keeping Money Mule Recruiters on a Short Leash - Part Nine
The following brief summarizes currently active money mule recruitment web sites, actively recruiting money mules for the processing of fraudulently obtained funds.
Currently active sites residing within AS42708, PORTLANE Network www.portlane.com; AS29713, INTERPLEXINC Interplex LLC; AS38913, Enter-Net-Team-AS; AS24940, HETZNER-AS Hetzner Online:
ATLANTALTD-UK.CC - 193.105.134.233
ATLANTA-LTD-UK.NET - 78.46.105.205 - Email: admin@atlanta-ltd-uk.net
3ATLANTA-UK.COM - 193.105.134.233
BLITZNET-GROUPINC.CC - 78.46.105.205 - Email: admin@derwart-group.at
5DALI-STYLE.COM - 98.141.220.117
DALISTYLE-GROUP.CC - 98.141.220.118 - Email: tolls@mailti.com
DERWOODE-GROUP.COM - 98.141.220.117
DERWOODE-GROUP.NET - 98.141.220.117
GLACIS-GROUPLLC.COM - 193.105.134.232
1GLACISGROUP-LLC.NET - 193.105.134.233
IT-AMIRA.NET - 86.55.210.3 - Email: support@it-amira.net
ITAMIRA-DE.COM - 86.55.210.6 - Email: admin@itamira-de.com
ITSERV-DE.CO - 78.46.105.205 - Email: admin@itserv-de.co
IT-SERVICELTD.BE - 78.46.105.205
KADE-GROUP.COM - 86.55.210.4 - Email: admin@kade-group.com
MASTERART-GROUP.COM - 98.141.220.116 - Email: east@mail13.com
MENDRYLTD.COM - 98.141.220.117 - Email: admin@mendryltd.com
MENZEL-GROUP.TV - 98.141.220.118 - Email: admin@devotion-company.com
MITISSANSERVICE-GROUP-LTD.CC - 98.141.220.117 - Email: berra@cutemail.org
MITISSANSERVICEGROUP-LTD.COM - 98.141.220.117 - Email: alibi@mailae.com
oregonltd-uk.cc - 86.55.210.5 - Email: cause@ca4.ru
PARLEN-GROUPLLC.COM - 98.141.220.118 - Email: admin@parlen-groupllc.com
PARLENGROUPLLC.NET - 98.141.220.114
PARLEN-GROUP-USA.COM - 98.141.220.118
quad-groupuk.cc - 86.55.210.6 - Email: prissy@mailae.com
QUAD-GROUPUK.CC - 86.55.210.6 - Email: prissy@mailae.com
QUAD-IT-GROUP.COM - 193.105.134.232 - Email: admin@quad-it-group.com
QUINTAGROUP.CC - 98.141.220.117 - Email: cola@mailae.com
QUINTA-GROUPUS.COM - 98.141.220.118 - Email: admin@quinta-groupus.com
QUINTA-LLC.NET - 98.141.220.118 - Email: admin@quinta-llc.net
REXTECHINNOVATION.COM - 98.141.220.118 - Email: admin@rextechinnovation.com
REXTECHLTD.CC - 98.141.220.115 - Email: blurt@fxmail.net
REXTECHLTD-US.COM - 98.141.220.118 - Email: admin@rextechltd-us.com
SPECIAL-ART-LTD.COM - 193.105.134.233 - Email: admin@special-art-ltd.com
SPECIAL-ART-UK.CC - 193.105.134.234
SUBLIME-LTD.NET - 98.141.220.118 - Email: admin@sublime-ltd.net
TARGETMARKETGROUP-LLC.CC - 98.141.220.117 - Email: admin@targetmarketgroup-llc.cc
TAZPROGLTD-US.COM - 98.141.220.117 - Email: admin@tazprogltd-us.co
VNSPROJECT-DE.CC - 78.46.105.205 - Email: admin@vnsproject-de.cc
VORTEXLLC-UK.COM - 193.105.134.232 - Email: admin@vortexllc-uk.com
VORTEX-LLC-UK.NET - 193.105.134.230 - Email: admin@vortex-llc-uk.net
Name servers of notice:
NS1.NAMESUKNS.CC - 178.162.172.48 - Email: pal@bz3.ru
NS2.NAMESUKNS.CC - 69.10.56.131
NS3.NAMESUKNS.CC - 66.199.229.123
NS1.NAMEUK.AT - 178.162.172.57 - Email: admin@nameuk.at
NS2.NAMEUK.AT - 69.10.56.132
NS3.NAMEUK.AT - 66.199.229.124
NS1.UKDNSTART.NET - 178.162.172.40 - Email: admin@ukdnstart.net
NS2.UKDNSTART.NET - 69.10.56.130
NS3.UKDNSTART.NET - 66.199.229.122
NS1.DNSUS.SU - 217.23.15.137 - Email: wifi@yourisp.ru
NS2.DNSUS.SU - 87.118.81.7
NS3.DNSUS.SU - 87.118.81.10
NS1.NAMEUSNS.SU - 217.23.15.138 - Email: lavier@bz3.ru
NS2.NAMEUSNS.SU - 84.19.161.7
NS3.NAMEUSNS.SU - 84.19.161.10
NS1.USDENNS.SU - 217.23.15.136 - Email: lipstick@free-id.ru
NS2.USDENNS.SU - 84.19.161.7
NS3.USDENNS.SU - 84.19.161.10
Monitoring of money mule recruitment campaigns is ongoing.
Related posts:
Keeping Money Mule Recruiters on a Short Leash - Part Eight - Historical OSINT
Keeping Money Mule Recruiters on a Short Leash - Part Seven
Keeping Money Mule Recruiters on a Short Leash - Part Six
Keeping Money Mule Recruiters on a Short Leash - Part Five
The DNS Infrastructure of the Money Mule Recruitment Ecosystem
Keeping Money Mule Recruiters on a Short Leash - Part Four
Money Mule Recruitment Campaign Serving Client-Side Exploits
Keeping Money Mule Recruiters on a Short Leash - Part Three
Money Mule Recruiters on Yahoo!'s Web Hosting
Dissecting an Ongoing Money Mule Recruitment Campaign
Keeping Money Mule Recruiters on a Short Leash - Part Two
Keeping Reshipping Mule Recruiters on a Short Leash
Keeping Money Mule Recruiters on a Short Leash
Standardizing the Money Mule Recruitment Process
Inside a Money Laundering Group's Spamming Operations
Money Mule Recruiters use ASProx's Fast Fluxing Services
Money Mules Syndicate Actively Recruiting Since 2002
This post has been reproduced from Dancho Danchev's blog.
Tags:
Cybercrime,
Hacking,
Information Security,
Money Laundering,
Money Mule,
Money Mule Recruitment,
Security
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Subscribe to:
Posts (Atom)