In the overwhelming sea of information, access to timely, insightful and independent open-source intelligence (OSINT) analyses is crucial for maintaining the necessary situational awareness to stay on the top of emerging security threats. This blog covers trends and fads, tactics and strategies, intersecting with third-party research, speculations and real-time CYBERINT assessments, all packed with sarcastic attitude
Tuesday, August 26, 2008
Fake Porn Sites Serving Malware - Part Three
This summary is not available. Please
click here to view the post.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Automatic Email Harvesting 2.0
 Just when you think that email harvesting matured into user names harvesting in a true Web 2.0 style with the recently uncovered harvested IM screen names, and Youtube user lists for spammers, phishers and malware authors to take advantage of, someone has filled in the gap that's been around as long as email harvesting has been a daily routine for spammers - dealing with text obfuscations which still remain highly popular online, once it became evident that spammers are in fact crawling for default mailto lines. This email harvesting module can be run a separate script, or get integrated as a module within any botnet, is capable of harvesting the following text obfuscations often used in order to prevent spamming crawlers :
Just when you think that email harvesting matured into user names harvesting in a true Web 2.0 style with the recently uncovered harvested IM screen names, and Youtube user lists for spammers, phishers and malware authors to take advantage of, someone has filled in the gap that's been around as long as email harvesting has been a daily routine for spammers - dealing with text obfuscations which still remain highly popular online, once it became evident that spammers are in fact crawling for default mailto lines. This email harvesting module can be run a separate script, or get integrated as a module within any botnet, is capable of harvesting the following text obfuscations often used in order to prevent spamming crawlers : mail@mail.com
mail[at]mail.com
mail[at]mail[dot]com
mail [space]mail [space]com
mail(@)mail.com
mail(a)mail.com
mail AT mail DOT com
The overall availability and easy of obtaining a huge percentage of valid email addresses within an organizaton, is not just resulting in the increasing segmentation and localization of spam, phishing and malware campaigns, it's increasing the profit margins for the spamming providers which is now not just offering verified to be 100% valid email addresses, but also, can providing the foundations for spear phishing and targeted attacks.
Quality assurance in spamming is still in its introduction phrase, with customers starting to put the emphasis on the number of emails that actually made it through the spam filters, than the number of emails sent as a benchmark for increasing the probability of bypassing anti spam filters. Taking into consideration the big picture, sniffing for email addresses streaming out of malware infected hosts, and stealing huge email databases by exploiting vulnerable online communities, seems to be the tactics of choice for the majority of individuals whose responsibility is to continuously provide fresh and valid email addresses.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Monday, August 25, 2008
A Diverse Portfolio of Fake Security Software - Part Four
 Thanks to the affiliate based business model that's driving the increase of fake security software and rogue codecs serving domains, the very same templates, but with different domain names, continue appearing in blackhat SEO, spam, and malicious doorways redirection campaigns.
Thanks to the affiliate based business model that's driving the increase of fake security software and rogue codecs serving domains, the very same templates, but with different domain names, continue appearing in blackhat SEO, spam, and malicious doorways redirection campaigns.Moreover, with the "time-to-market" of a fake security software decreasing due to the efficiency approach introduced in the form of tips for abuse-free hosting services provided by the "known suspects", and the freely available templates, we're slowly starting to see the upcoming peak of this approach.
In a true proactive spirit, the domains parked at 216.195.56.88 are all upcoming fake security software, to be introduced anytime soon.
fast-pc-scanner-online .com - (92.62.101.41; 91.203.92.48; 91.203.92.106; 58.65.238.171)
top-pc-scanner .com
buy-secure-protection .com
security-scan-pc .com
pc-scanner-online .com
viruses-scanonline .com
virus-scanonline .com
antivirus-scanonline .com
topvirusscan .com
virusbestscan .com
best-security-protection .com
infectionscanner .com
virusbestscanner .com
full-protection-now .com
Pwrantivirus .com - 91.208.0.246
vav-x-scanner .com
vav-scanner .com
scanner.vavscan .com
malware-scan .com
Scanner-Pwrantivirus .com
Xpertantivirus .com
Scanner-xpertantivirus .com
spyware-quickscan-2008 .com - (216.195.56.88)
virus-quickscan-2008 .com
spyware-quickscan-2009 .com
virus-quickscan-2009 .com
winmalwarecontrol .com
antispyware-quick-scan .com
virus-quick-scan .com
antivirus-quick-scan .com
winprivacytool .com
topantispyware2008 .com - (216.195.56.86)
cleanermaster .com - (216.195.56.85)
antivirus777 .com - (67.228.120.3)
pcsecuritynotice .com - (67.228.120.3)
Whereas the average Internet users are falling victims into this type of fraud, what I'm more concerned about is the large traffic the malicious domains receive in general due to all the different traffic acquisition tactics the people behind them apply. This anticipated traffic can then be greatly used as valuable metrics for the many other malicious ways in which it can be monetized.
Ironically, the participant in the affiliate program whose original objective was to drive traffic to the fake security software's site, may in fact start receiving so much traffic due to the combination of traffic acquisition tactics, that introducing client-side exploits courtesy of a third-party affiliate network, may in fact prove more profitable then the revenue sharing partnership with the rogue security software's vendor at the first place.
Related posts:
A Diverse Portfolio of Fake Security Software - Part Three
A Diverse Portfolio of Fake Security Software - Part Two
Localized Fake Security Software
Diverse Portfolio of Fake Security Software
Got Your XPShield Up and Running?
Fake PestPatrol Security Software
RBN's Fake Security Software
Lazy Summer Days at UkrTeleGroup Ltd
Geolocating Malicious ISPs
The Malicious ISPs You Rarely See in Any Report
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Friday, August 22, 2008
Web Based Botnet Command and Control Kit 2.0
 The average web based command and control kit for a botnet consisting of single user, single campaign functions only, has just lost its charm, with a recent discovery of a proprietary botnet kit whose features clearly indicate that the kit's coder know exactly which niches to fill - presumably based on his personal experience or market research into competing products.
The average web based command and control kit for a botnet consisting of single user, single campaign functions only, has just lost its charm, with a recent discovery of a proprietary botnet kit whose features clearly indicate that the kit's coder know exactly which niches to fill - presumably based on his personal experience or market research into competing products.What are some its key differentiation factors? Multitasking at its best, for instance, the kits provides the botnet master with the opportunity to manage numerous different task such as several malware campaigns and DDoS attacks simultaneously, where each of these gets a separate metrics page.
 Automation of malicious tasks, by setting up tasks, and issuing notices on the status of the task, when it was run and when it was ended. Just consider the possibilities for a scheduling malware and DDoS attacks for different quarters.
Automation of malicious tasks, by setting up tasks, and issuing notices on the status of the task, when it was run and when it was ended. Just consider the possibilities for a scheduling malware and DDoS attacks for different quarters. Segmentation in every aspect of the tasks, for instance, a DDoS attacks against a particular site can be scheduled to launched on a specific date from infected hosts based in chosen countries only.
 Customized DDoS in the sense of empowering the botnet master with point'n'click ability to dedicate a precise number of the bots to participate, which countries they should be based in, and for how long the attack should remain active. Quality and assurance in DDoS attacks based on the measurement of the bot's bandwidth against a particular country, in this case the object of the attack, so theoretically bots from neighboring countries would DDoS the country in question far more efficiently.
Customized DDoS in the sense of empowering the botnet master with point'n'click ability to dedicate a precise number of the bots to participate, which countries they should be based in, and for how long the attack should remain active. Quality and assurance in DDoS attacks based on the measurement of the bot's bandwidth against a particular country, in this case the object of the attack, so theoretically bots from neighboring countries would DDoS the country in question far more efficiently.  Historical malware campaign performance, is perhaps the most quality assurance feature in the entire kit, presumably created in order to allow the person behind it to measure which were the most effective malware and DDoS campaigns that he executed in the past. From an OSINT perspective, sacrificing his operational security by maintaing detailed logs from previous attacks is a gold mine directly establishing his relationships with previous malware campaigns.
Historical malware campaign performance, is perhaps the most quality assurance feature in the entire kit, presumably created in order to allow the person behind it to measure which were the most effective malware and DDoS campaigns that he executed in the past. From an OSINT perspective, sacrificing his operational security by maintaing detailed logs from previous attacks is a gold mine directly establishing his relationships with previous malware campaigns.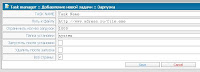 Bot Description:
Bot Description: 1. Completely invisible Bot work in the system.
2. Not loads system.
3. Invisible in the process.
4. Workaround all firewall.
5. Bot implemented as a driver.
2. Not loads system.
3. Invisible in the process.
4. Workaround all firewall.
5. Bot implemented as a driver.
1. Downloading a file (many options).
2. HTTP DDoS (many options, including http authentication).
2. HTTP DDoS (many options, including http authentication).
-- Convenient manager tasks.
-- Every task can be stopped, put on pause, etc. ...
-- Interest and visual scale of the task.
-- Every task can be stopped, put on pause, etc. ...
-- Interest and visual scale of the task.
-- A task manager for DDoS and Loader
Bots involved in DDoS 'f.
Condition of the victim (works, fell).
Condition of the victim (works, fell).
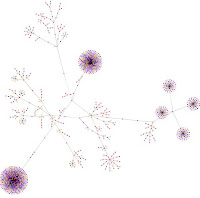
 2. Bots manager
2. Bots manager -- Displays a list of bots (postranichno).
-- Obratseniya date of the first and last.
-- ID Bot.
-- Country Bot.
-- Type Bot.
-- The status Bot (online / offline).
-- Bot bandwidth to different parts of the world (europe, asia).
-- The possibility of removing bots
-- When you click on ID Bot loadable still a wealth of information about it
 3. Statistics botneta
3. Statistics botneta -- Statistics both common and build Bot.
-- Information on the growth and decline botneta dates (and build).
-- Bots online
-- All bots
-- All countries to work on
-- New work by country
-- Online work from country to country
-- Dead bots by country
5. Detailed history botneta
6. Convenient user-friendly interface adding teams
7. Admin minimal server loads
-- Use php5/mysql
 Upcoming features :
Upcoming features : 1. Form grabber (price increase substantially), for old customers will be charged as an upgrade
2. Public key cryptography
3. Clustering campaigns and DDoS attacks
Despite it's proprietary nature, it's quality and innovative features will sooner or later leak out for everyone to take advantage of, a rather common lifecycle for the majority of proprietary malware kits in general.
Related posts:
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Thursday, August 21, 2008
Fake Celebrity Video Sites Serving Malware - Part Two
 Malicious parties remain busy crunching out domain portfolios of legitimately looking celebrity video sites. The very same templates used on the majority of fake celebrity video sites which I exposed in a previous post, remain in circulation with anecdotal situations where they aren't even bothering to match the site's logo with the domain name -- it would ruin the malicious economies of scale approach. And since centralization to some, an laziness to others, remains in tact, the fake security software and fake codecs served remain once parked at the same IP as the fake celebrity sites which I'll expose in this post.
Malicious parties remain busy crunching out domain portfolios of legitimately looking celebrity video sites. The very same templates used on the majority of fake celebrity video sites which I exposed in a previous post, remain in circulation with anecdotal situations where they aren't even bothering to match the site's logo with the domain name -- it would ruin the malicious economies of scale approach. And since centralization to some, an laziness to others, remains in tact, the fake security software and fake codecs served remain once parked at the same IP as the fake celebrity sites which I'll expose in this post.starfeed1 .com - (85.255.117.218)
codecservice1 .com
siteresults1 .com
codecservice6 .com
celebs69 .com
topdirectdownload .com
sexlookupworld .com
favoredtube .com
yourfavoritetube .com
wwvyoutube .com
celebsnofake .com
celebsvidsonline .com
celebstape .com
freevidshardcore .com
topsoftupdate .com
porndebug .com
newfunnyvideo .com
bestfunnyvids .com
pornmoviestube .net
antivirus2008-pro .name
antivirus-2008pro .name
antivirus2008pro .name
antivirus2008pro-download .org
antivirus-2008-pro .org
antivirus2008-pro .org
antivirus-2008pro .org
antivirus2008pro .org
thesoft-portal-08 .com
stars-08 .com
thestars-08 .com
thebigstars-08 .com
funny-08 .com
realonlinevideo-2008 .com
2008-adult-2008 .com
adult18tube2008 .com
adultstreamportal2008 .com
2008-adult-s2008 .com
 new-content-s2008 .com
new-content-s2008 .comnewcontent-s2008 .com
worldstars2008 .com
thestars2008 .com
thebigstars2008 .com
newcontents2008 .com
18x-adult2008 .com
2008adult2008 .com
adult-x2008 .com
hotadulttube08 .com
adultxx-18 .com
newcontent-s2008a .com
antivirus2008pro-download .com
onlinestreamvide .com
onlinestreamvide .com
ns2.onlinestreamvide .com
xxxstreamonline .com4
supersoft21freeware .com
kvm-secure .com
kvmsecure .com
themusic-08portal .com
adultstreamportal .com
streamxxxvideo .com
antivirus-2008-pro .com
antivirus2008-pro .com
antivirus-2008pro .com
thefunny-08 .com
thestars-08 .com
thestars08 .com
celebsnofake .com
adult-s-portal .com
adultsoftcodec .com
adultstreamportal .com
adultxx-18 .com
 And while none of these seem to be taking advantage of client-side exploits, a Russian celebrity site that seems to by syndicating the malicious redirectors from a legitimate advertising network, is an exception worth point out due to the Adobe Flash player exploit it's attempting to take advantage of.
And while none of these seem to be taking advantage of client-side exploits, a Russian celebrity site that seems to by syndicating the malicious redirectors from a legitimate advertising network, is an exception worth point out due to the Adobe Flash player exploit it's attempting to take advantage of. Bestcelebs .ru javascript redirectors through several different doorways :
 crklab .us/index.php => firstblu .cn/3.php?19383577 => xanjan .cn/in.cgi?mytraf => atomakayan .biz/afterftpcheck/2603/index.php =>
crklab .us/index.php => firstblu .cn/3.php?19383577 => xanjan .cn/in.cgi?mytraf => atomakayan .biz/afterftpcheck/2603/index.php => toksikoza .net/fi/index.php?mytraf => toksikoza .net/fi/1.swf
What you see is so not what you get.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Wednesday, August 20, 2008
A Diverse Portfolio of Fake Security Software - Part Three
 One would assume that once you've managed to trick leading advertising providers into accepting your malicious flash ads inside their networks, you would do anything but hijack the end user's clipboard and rely on their curiosity in order to direct them to your fake security software site. Is the curiosity approach working anyway? Naturally, thanks to the effect of "regressive Darwinism".
One would assume that once you've managed to trick leading advertising providers into accepting your malicious flash ads inside their networks, you would do anything but hijack the end user's clipboard and rely on their curiosity in order to direct them to your fake security software site. Is the curiosity approach working anyway? Naturally, thanks to the effect of "regressive Darwinism".Compared to February, 2008's malicious advertising (Malvertising) attack, the current one is less comprehensive and not so well thought of -- thankfully.
What these campaigns have in common is the fake security software served at the bottom line, next to the malware campaigners persistence in introducing new domains, like the very latest ones :
adware-download .com
windows-scanner2009 .com
antivirus2008free .com
antivirusfree2008 .net
antispyware2008scanner .com
softwareantivirus2008 .com
free-2008-antivirus .com
free-2008-antivirus .net
free-antivirus-2008 .com
free-antivirus-2008 .net
free2008antivirus .com
free2008antivirus .net
getas2008xp .com
software-2008-antivirus .com
software-2008-antivirus .net
software-antivirus-2008 .com
software2008antivirus .com
software2008antivirus .net
softwareantivirus .net
2008-software-antivirus .net
2008-xp-antivirus .com
2008antivirusfree .com
2008antivirusfree .net
2008antivirussoftware .com
2008antivirussoftware .net
2008antivirusxp .net
2008freeantivirus .com
2008freeantivirus .net
2008softwareantivirus .com
2008softwareantivirus .net
2008xpantivirus .net
2008-antivirus-free .com
2008antivirusxp .com
2008-free-antivirus .com
2008-free-antivirus .com
2008-free-antivirus .net
2008-antivirus-free .net
2008-antivirus-software .net
2008-antivirus .net
antivirus-2008-free .com
antivirus-2008-free .net
antivirus-2008-software .com
antivirus-2008-software .net
antivirus-free-2008 .com
antivirus-software-2008 .com
No matter how fancy malvertising is in respect to demonstrating the creativity of malicious parties wanting to appear at legitimate sites by abusing their advertising providers, there are far more efficient tactics to do so.
 Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Independent Security Consultancy, Threat Intelligence Analysis (OSINT/Cyber Counter Intelligence) and Competitive Intelligence research on demand. Insightful, unbiased, and client-tailored assessments, neatly communicated in the form of interactive reports - because anticipating the emerging threatscape is what shapes the big picture at the end of the day. Approach me at dancho.danchev@hush.com
Subscribe to:
Comments (Atom)




