Continuing the "
FBI Most Wanted Cybercriminals" series I've decided to take a closer look at the "Jabber ZeuS" including
Evgeniy Mikhaylovich Bogachev for the purpose of providing actionable intelligence on the fraudulent and malicious infrastructure that was utilized in the campaign including personally identifiable information of the individuals behind it with the idea to assist law enforcement and the U.S Intelligence community with the necessary data to track down and prosecute the individuals behind the campaign.
In this post I'll provide actionable intelligence on the infrastructure used by the "Jabber ZeuS" gang including personally identifiable information for Evgeniy Mikhaylovich Bogachev and some of his known associates.
Sample Personal Photos of Evgeniy Mikhaylovich Bogachev:
Slavik's IM and personal email including responding IP:
bashorg@talking.cc - 112.175.50.220
Personal Address:
Lermontova Str. Anapa, Russian Federation
Instant Messaging account:
lucky12345@jabber.cz
Related name servers:
ns.humboldtec.cz - 88.86.102.49
ns2.humboldtec.cz - 188.165.248.173
Related domains part of a C&C phone-back location:
hxxp://slaviki-res1.com
hxxp://slavik1.com - 91.213.72.115
hxxp://slavik2.com
hxxp://slavik3.com
Slavik's primary email:
luckycats2008@yahoo.com
Slavik's ICQ numbers:
ICQ - 42729771
ICQ - 312456
Related emails known to have participated in the campaign:
alexgarbar-chuck@yahoo.com
bollinger.evgeniy@yandex.ru
charajiang16@gmail.com
Related domains known to have participated in the campaign:
hxxp://visitcoastweekend.com - 103.224.182.253; 70.32.1.32; 192.184.12.62; 141.8.224.93; 69.43.160.163
hxxp://incomeet.com - 192.186.226.71; 66.199.248.195
hxxp://work.businessclub.so
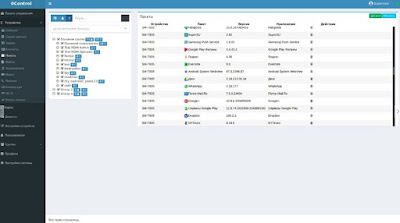
Related information on his colleague (chingiz) as seen in the attached screenshot:
Real Name: Galdziev Chingiz
Related domains known to have participated in the campaign:
hxxp://fizot.org
hxxp://fizot.com - 50.63.202.35; 184.168.221.33
hxxp://poymi.ru - 109.206.190.54
Related name servers known to have participated in the campaign:
ns1.fizot.com - 35.186.238.101
ns2.fizot.com
Related domain including an associated email using the same name server:
hxxp://averfame.org - harold@avereanoia.org
Google Analytics ID: UA-3816538
Related domains known to have participated in the campaign:
hxxp://awmproxy.com
hxxp://pornxplayer.com
Related emails known to have participated in the campaign:
fizot@mail.ru
xtexgroup@gmail.com
xtexcounter@bk.ru
Related domains known to have responded to the same malicious and fraudulent IP - 178.162.188.28:
hxxp://dnevnik.cc
hxxp://xvpn.ru
hxxp://xsave.ru
hxxp://anyget.ru
hxxp://nezayti.ru
hxxp://proproxy.ru
hxxp://hitmovies.ru
hxxp://appfriends.ru
hxxp://naraboteya.ru
hxxp://naraboteya.ru
hxxp://awmproxy.com
hxxp://zzyoutube.com
hxxp://pornxplayer.com
hxxp://awmproxy.net
hxxp://checkerproxy.net
Related domains known to have participated in the campaign:
hxxp://fizot.livejournal.com/
hxxp://russiaru.net/fizot/
Instant Messaging Account:
ICQ - 795781
Related personally identifiable information of Galdziev Chingiz:
hxxp://phpnow.ru
ICQ - 434929
Email: info@phpnow.ru
Related domains known to have participated in the campaign:
hxxp://filmv.net
hxxp://finance-customer.com
hxxp://firelinesecrets.com
hxxp://fllmphpxpwqeyhj.net
hxxp://flsunstate333.com
Related individuals known to have participated in the campaign:
Slavik, Monstr, IOO, Nu11, nvidiag, zebra7753, lexa_Mef, gss, iceIX, Harderman, Gribodemon, Aqua, aquaSecond, it, percent, cp01, hct, xman, Pepsi, miami, miamibc, petr0vich, Mr. ICQ, Tank, tankist, Kusunagi, Noname, Lucky, Bashorg, Indep, Mask, Enx, Benny, Bentley, Denis Lubimov, MaDaGaSka, Vkontake, rfcid, parik, reronic, Daniel, bx1, Daniel Hamza, Danielbx1, jah, Jonni, jtk, Veggi Roma, D frank, duo, Admin2010, h4x0rdz, Donsft, mary.J555, susanneon, kainehabe, virus_e_2003, spaishp, sere.bro, muddem, mechan1zm, vlad.dimitrov, jheto2002, sector.exploits
Related Instant Messaging accounts and emails known to have participated in the campaign:
iceix@secure-jabber.biz
shwark.power.andrew@gmail.com
johnlecun@gmail.com
gribodemon@pochta.ru,
glazgo-update-notifier@gajim.org
gribo-demon@jabber.ru
aqua@incomeet.com
miami@jabbluisa.com
um@jabbim.com
hof@headcounter.org
theklutch@gmail.com
niko@grad.com
Johnny@guru.bearin.donetsk.au
petr0vich@incomeet.com
mricq@incomeet.com
T4ank@ua.fm
tank@incomeet.com
getreadysafebox.ru
john.mikleymaiI.com
aIexeysafinyahoo.corn
rnoscow.berlin@yahoo.com
cruelintention@email.ru,
bind@ernail.ru
firstmen17@rarnbler.ru
benny@jabber.cz
airlord1988@gmail.com
bxl@hotmail.com
i_amhere@hotmail.fr
daniel.h.b@universityofsutton.com
princedelune@hotmail.fr
bxl_@msn.com
danibxl@hotmail.fr
danieldelcore@hotmail.com.
d.frank@jabber.jp
d.frank@0nl1ne.at
duo@jabber.cn
fering99@yahoo.com
secustar@mail.ru
h4x0rdz@hotmail.com
Donsft@hotmail.com
mary.j555@hotmail.com
susanneon@googlemail.com
kainehabe@hotmail.com
virus_e_2003@hotmail.com
spanishp@hotmail.com
sere.bro@hotmail.com
lostbuffer@hotmail.com
lostbuffer@gmail.com
vlad.dimitrov@hotmail.com
jheto2002@gmail.com
sector.exploits@gmail.com
We'll post new updates as soon as new developments take place.
Related posts:
Exposing Iran's Most Wanted Cybercriminals - FBI Most Wanted Checklist - OSINT Analysis
Who's Behind the Syrian Electronic Army? - An OSINT Analysis